.dharma Ransomware
The article we are going to present in the following paragraphs is focused on one of the nastiest malware programs ever known to users in the world – .dharma Ransomware. No matter whether your case involves being contaminated by that virus, or simply being curious about its effects and its roots, we are going to give you important prevention, removal, as well as some informative tips about that. Read the paragraphs below carefully and hopefully, they will help you solve your issues.
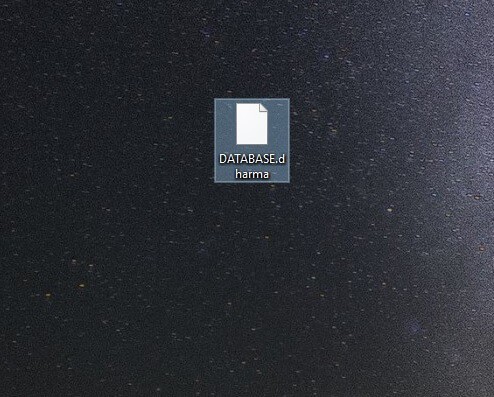
.dharma Ransomware
.dharma – how, when and where you have got to know it?
Unfortunately, the virus your system has caught is not from the relatively harmless ones. It is a part of the group of the most dangerous malware – Ransomware. These programs are created with the single purpose of harassing you, blackmailing you, disturbing your online experience and extorting money from you. .dharma is not an exception as it does exactly that. .dharma usually comes to your PC together with its dearest friend – a Trojan horse virus. The two fellows are hazardous enough by themselves, but together they can really harm your machine in many different and evil ways. Those two troublemakers could be found in various online places like torrents and software bundles. They may be lurking inside a contaminated website. However, the thing you need to be especially careful with are the strange emails you receive, either in your Spam folder or your Inbox, and their attachments. Avoid opening and downloading anything suspicious from your email at any cost because this is the favorite residing place of all versions of Ransomware and the Trojans that come with them.
The role of the Trojan in this dangerous duo is to ensure the successful passage of the Ransomware to your system. Usually it does that stealthily and secretly, just like the Trojan horse from the popular myth, you are unlikely to notice any of its activities. Once the Trojan succeeds in sneaking in .dharma , the second fellow is free to start working according to its plan. Its plan actually consists of two parts: during the first part this virus completes a scan of all the places in your system where you keep data. From the results of the scan, .dharma chooses the files/ locations you most regularly go to/ use and puts them in a list. The last and the most horrible action this Ransomware completes is to begin encoding all the enlisted files. For this purpose, it uses a double-component encryption key. The two components of the key are different. The public one is given to you after the encryption process, but the private part you have to purchase by paying the requested ransom in order to have your files back. To top it all, after all the disturbing activities are done, you get a notification that informs you about the infection and about the requests of the hackers.
Here we would like to mention something very important: you should never trust any hacker. They are criminals just like any physical ones. You shouldn’t rush into paying the ransom because doing that doesn’t mean that you will get your files back. It just means that you will pay criminals and in this way you may encourage them to blackmail more users. What you also need to know is that the removal of the malware doesn’t guarantee you recovery of your access to the locked-up data. Do some research, talk with someone who is adept at Ransomware and then make an informed decision, because any decision here represents a risk to your important data.
Some advice on prevention and removal
Prevention is the only successful instrument when it comes to fighting any form of Ransomware. The first piece of advice is to make sure that your entire system is not vulnerable. Install the best anti-virus system, update and turn on your Firewall. These tools have been created to keep you safe, so let them do their job. If you manage to win the battle with .dharma somehow, don’t forget to deal with the Trojan from the duo as well. The Trojan is a very subtle virus and can get you into a lot of trouble. Remove it before or after you remove the Ransomware. It is a must! The most ignored but still important step towards a healthy PC is to browse the web in a clever way. This means to read more about possible dangers, to educate yourself and to avoid anything that seems suspicious online: websites, torrents, software bundles and letters in your email.
SUMMARY:
| Name | .dharma |
| Type | Ransomware |
| Detection Tool | .dharma may be difficult to track down. Use SpyHunter – a professional parasite scanner – to make sure you find all files related to the infection. |
.dharma File Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

127.0.0.1 htagzdownload .pw
127.0.0.1 texttotalk.org
127.0.0.1 360devtraki ng. website
127.0.0.1 room1. 360dev .info
127.0.0.1 djapp. info
127.0.0.1 technologievimy. com
The IP that you’ve send us do not belong in your Hosts file and need to be removed from there. Remove them, save the changes and then continue with the rest of the guide.