Do You Do Any of These Embarrassing Things
“Do You Do Any of These Embarrassing Things” is a cyber threat categorized as a Trojan Horse and it can enter your computer unnoticed and then start manipulating critical system processes and files. Online scammers often use “Do You Do Any of These Embarrassing Things” to threaten their potential victims and intimidate them into paying a ransom.
A new email scam has recently been gaining popularity among the cyber criminal circles and a number of web users have already fallen victims of the shady scheme. This scam involves sending an email message to the targeted users, which message asks the victims to send money to a given BitCoin wallet and could also be related to the distribution of a nasty Trojan Horse infection named “Do You Do Any of These Embarrassing Things”. The criminals behind the bitcoin scam email typically focus on spamming the users’ mailboxes with ransom-demanding and phishing messages that state the system has been infected with malware and now there is a hacker who has gained remote access to the computer and has gotten his hands on some sensitive information, embarrassing photos and other personal data. The crook threatens to do some nasty stuff to the data and the machine if the victim doesn’t send a fixed amount of money to the hacker’s BitCoin wallet. Unfortunately, a number of users have already been greeted by phishing emails of this type and some of them have been tricked into fulfilling the hacker’s demands. The security experts, however, warn that there is no real reason to believe such emails and threatening messages unless there really is a malware inside the given machine. That’s why, instead of giving money to some self-proclaimed hackers, one of the first things that the users should do is scan their computers with reliable antivirus software. If the scan does not detect anything disturbing, then you probably have come across a ruse/fake message, the only aim of which is to trick you into sending your money.
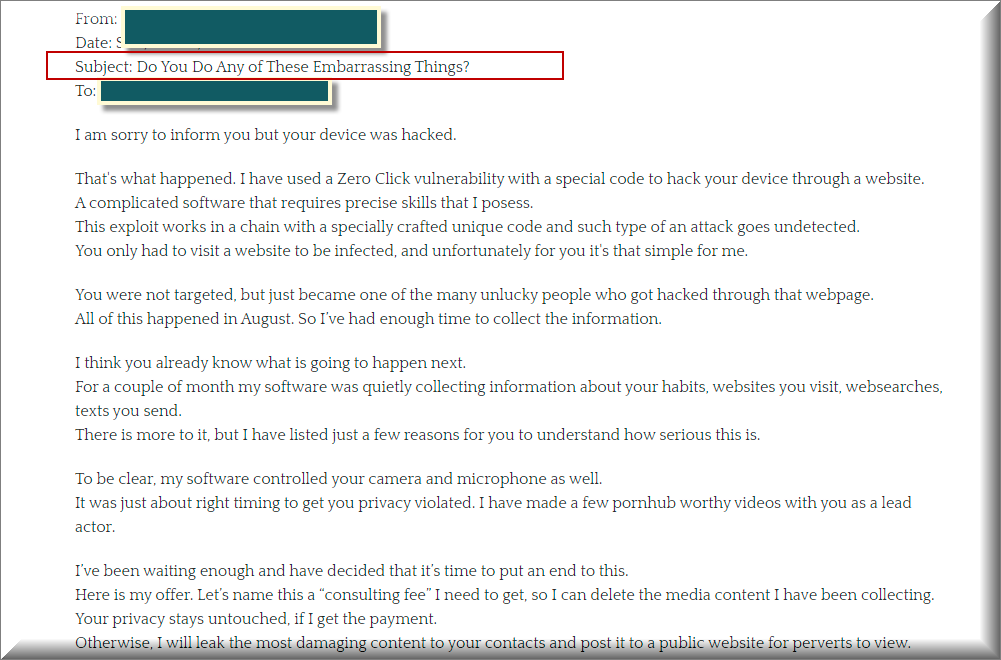
Many of our users reported to us about an ongoing email spam with the following message:
Subject: Do You Do Any of These Embarrassing Things?
I am sorry to inform you but your device was hacked.
That’s what happened. I have used a Zero Click vulnerability with a special code to hack your device through a website.
A complicated software that requires precise skills that I posess.
This exploit works in a chain with a specially crafted unique code and such type of an attack goes undetected.
You only had to visit a website to be infected, and unfortunately for you it’s that simple for me.You were not targeted, but just became one of the many unlucky people who got hacked through that webpage.
All of this happened in August. So I’ve had enough time to collect the information.I think you already know what is going to happen next.
For a couple of month my software was quietly collecting information about your habits, websites you visit, websearches, texts you send.
There is more to it, but I have listed just a few reasons for you to understand how serious this is.To be clear, my software controlled your camera and microphone as well.
It was just about right timing to get you privacy violated. I have made a few pornhub worthy videos with you as a lead actor.I’ve been waiting enough and have decided that it’s time to put an end to this.
Here is my offer. Let’s name this a “consulting fee” I need to get, so I can delete the media content I have been collecting.
Your privacy stays untouched, if I get the payment.
Otherwise, I will leak the most damaging content to your contacts and post it to a public website for perverts to view.You and I understand how damaging this will be to you, it’s not that much money to keep your privacy.
I don’t care about you personally, that’s why you can be sure that all files I have and software on your device will be deleted immediately after I receive the transfer.
I only care about getting paid.My modest consulting fee is 1700 US Dollars to be transferred in Bitcoin. Exchange rate at the time of the transfer.
You need to send that amount to this wallet: [ Details deleted ]The fee is non negotiable, to be transferred within 2 business days.
Obviously do not try to ask for help from the law enforcement unless you want your privacy to be violated.
I will monitor your every move until I get paid. If you keep your end of the agreement, you wont hear from me ever again.Take care and have a good day.
Sometimes, however, Trojans such as “Do You Do Any of These Embarrassing Things” may really compromise the system of your computer with the help of spam messages and scam emails like the one that we described above. The worst thing is that you may not realize it until something really bad happens to your computer or the hacker who’s behind the threat contacts you with a similar scam message. That’s why, in the removal guide below, we will show you how to detect and remove this threat on time.
The Do You Do Any of These Embarrassing Things Email
Threats such as the “Do You Do Any of These Embarrassing Things” Email can sneak inside the computers without being detected and can cause a lot of trouble. The “Do You Do Any of These Embarrassing Things” Email can provide its criminal creators with remote to the infected computer and allow them to get their hands on anything they want that’s inside the machine.
That’s why receiving threatening emails with blackmailing agendas is just the tip of the iceberg. If not removed on time, aside from tricking you into sending money to anonymous hackers, the Trojans may insert other malware such as real Ransomware or Spyware and steal your login credentials, banking details, passwords and more. They are the perfect tools for various types of fraud, theft, espionage and harassment. That’s why you should waste no time and instead remove those nasty infections in the fastest and the most reliable way. If you don’t have a professional scanner and removal tool which can easily detect and delete “Do You Do Any of These Embarrassing Things” we suggest you use the malware removal tool on this page which can carefully check your entire system and remove all the related Trojan files.
SUMMARY:
| Name | “Do You Do Any of These Embarrassing Things” |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | The Trojan infections typically hide their symptoms and are extremely difficult to detect without a proper security tool. |
| Distribution Method | Different email scams, malicious attachments, infected links, fake ads, contaminated software installers, illegal websites. |
| Detection Tool |
Remove “Do You Do Any of These Embarrassing Things” Email
If you are looking for a way to remove “Do You Do Any of These Embarrassing Things” you can try this:
- Click on the Start button in the bottom left corner of your Windows OS.
- Go to Control Panel -> Programs and Features -> Uninstall a Program.
- Search for “Do You Do Any of These Embarrassing Things” and any other unfamiliar programs.
- Uninstall “Do You Do Any of These Embarrassing Things” as well as other suspicious programs.
Note that this might not get rid of “Do You Do Any of These Embarrassing Things” completely. For more detailed removal instructions follow the guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:


Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.

Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment