This page aims to help you remove .Docm Ransomware Virus for free. Our instructions also cover how any .Docm file can be recovered.
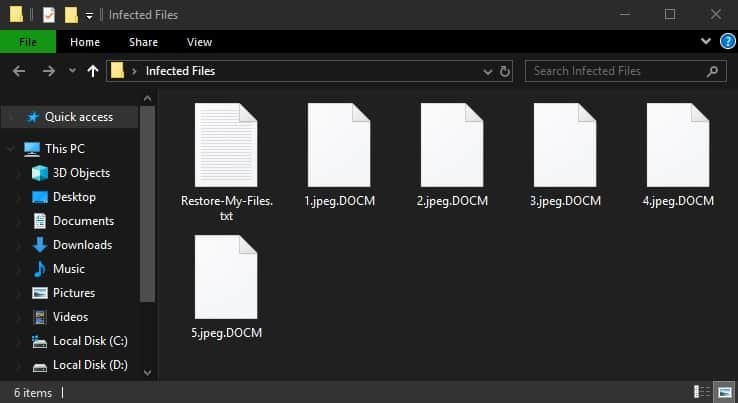
When the virus finishes encrypting your files it drops a Restore-My-Files.txt file with instructions for you to follow:
:-------------
All your files are Encrypted!
For data recovery needs decryptor.
How to buy decryptor:
----------------------------------------------------------------------------------------
| 1. Download Tor browser - https://www.torproject.org/ and install it.
| 2. Open link in TOR browser - http://decrmbgpvh6kvmti.onion/
| 3. Follow the instructions on this page
----------------------------------------------------------------------------------------
Note! This link is available via "Tor Browser" only.
------------------------------------------------------------
Free decryption as guarantee.
Before paying you can send us 1 file for free decryption.
------------------------------------------------------------
alternate address - http://helpinfh6vj47ift.onion/
There are many different kinds of malicious programs that may compromise the safety of your PC system and personal files if you’re not watchful with what you do while surfing the Web. One particularly hazardous form of malware that is going to be the focus of this post is what is referred to as Ransomware cryptoviruses. What this form of virus is usually employed for is blackmailing the targeted victim by demanding that they issue a ransom money payment to the cyber-criminal. Inside the text below, we’ll be focusing on a specific Ransomware cryptovirus which is able to lock-up your private document files, making them inaccessible to anyone who doesn’t have the decryption access key to them. Afterwards, the cryptovirus requests a ransom payment which is required to be executed by the victim in case they would like to get the decryption key for their encrypted software files.
The name of the specific malware program that we’re looking at in this post is .Docm Ransomware. If you’ve come to this article since this malicious malware piece has infected your computer, we might have the ability to aid you in dealing with this software threat.
How the .Docm Virus functions
These malicious virus programs do not operate like any other malware kind and that’s an essential thing to remember when attempting to fight them. Because of the unique way Ransomware viruses work, the majority of users are unable to stop such a virus which, in turn, makes this malware kind especially favored by an increasing number of cyber criminals.
One important thing that many are unaware of regarding Ransomware is that malware viruses of this sort do not typically get spotted and caught in time by the majority of conventional anti-malware programs. The thing that makes Ransomware attacks so sneaky and undetectable is the fact that nothing really gets damaged during the contamination process – instead of that, the piece of malware simply places the encryption on the private data of the attacked user, making the personal documents unavailable.
Something we should really mention here is the fact that the actual process of data encryption is not something that’s intended to cause harm to the targeted data files – the actual intent behind this type of process (when not employed by a Ransomware) is to keep the personal data secure.
Furthermore, there are only handful of difficult to spot red flags that may reveal an ongoing encryption process which makes an actual Ransomware invasion very hard to intercept in time. Still, though, it is not impossible to manually spot a Ransomware invasion – some possible red flags are reduced free Hard drive memory space and higher Virtual memory and Processor time use. Still, if perhaps there are some symptoms of a Ransomware infection, we advise you to ensure that you turn off your Computer and have it examined by a professional or, if it is too late and the files in the computer are now encrypted, it’s best if you try out the guide presented to our readers down below.
SUMMARY:
Remove .Docm Ransomware Virus
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Reply