.Domn
.Domn is a dangerous computer threat categorized as a Ransomware cryptovirus. If .Domn is in your computer, you won’t be able to open your files, and you’d be asked to pay a ransom for their release.
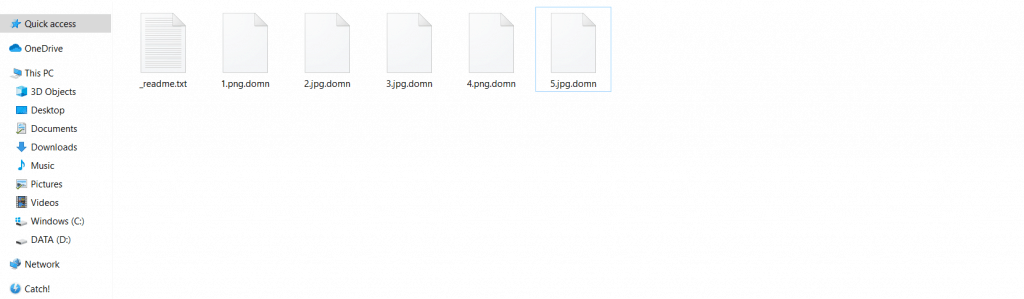
The results of .domn’s encryption.
This is how pretty much all Ransomware cryptovirus infections operate – once they infiltrate a given computer, they locate the user files that belong to certain commonly used file formats, and then go on to lock up those files using data-encryption. What this encryption does is it makes the targeted pieces of data inaccessible to anyone who tries to open them without the corresponding decryption key. Without that key, an encrypted file cannot be opened, or modified in any way, or by any program. The corresponding key is kept on the servers of the hackers behind the Ransomware, and their goal is to blackmail their victims for the release of the sealed files. The user is told to pay a certain amount of money, and promised that they would receive the needed access key as soon as the payment gets completed. We understand that many victims of Ransomware may not be able to afford such a payment, which is why it is important to have other methods of dealing with this threat at hand. Also, it should be mentioned that even if you can pay the ransom, doing so isn’t really an advisable course of action, as you may simply waste the money without getting anything helpful from the hackers.
The .Domn virus
The .Domn virus is a malware of the Ransomware variety. The Domn virus will encrypt the files of the targeted victims and make them unreadable unless a ransom payment is paid out. The .Domn file extension would be added to any encrypted files and the affected users would need a decryption key to get them back.
The .Domn virus is among the latest Ransomware representatives, and dealing with it may be quite tricky. Still, our removal guide for the .Domn virus would hopefully help you take care of this threat.
The instructions you will find after the current article should be enough to enable you to rid your computer of this nasty malware threat so that it won’t encrypt any more files in your system. And if for some reason the manual steps weren’t enough to fully eliminate this Ransomware, the suggested removal anti-malware tool that is also available in the guide is another option that could help you remove the cryptovirus.
The .Domn file encryption
The .Domn file encryption is a very complex algorithm, and breaking or bypassing it may not always be possible. What’s even worse is that the .Domn file encryption would remain on your files even after the virus is removed.
As we said earlier, you’d need a decryption key to unlock the files, but we do not advise you to pay a ransom for it. Instead, what we would suggest you do is remove the malware with the help of the guide below, and then head to the second part of the guide, where you can find some alternative options related to the recovery of your files. Though they may not always work, they are free to try, and may get you some of your files restored without you paying a ransom for their recovery.
How the .Domn Ransomware works
The .Domn ransomware sneaks in through the use of a trojan horse that is still active on your computer. We advise you to avoid plugging in any external devices or sending your contacts or the .Domn ransomware may infect them as well.
SUMMARY:
| Name | .Domn |
| Type | Ransomware |
| Detection Tool |
Remove .Domn Virus
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

If there are suspicious IPs below “Localhost” – write to us in the comments.
see below :
127.0.0.1 localhost
0.0.0.0 serius.mwbsys.com
0.0.0.0 keystone.mwbsys.com
The second and the third addresses should be deleted from your Hosts file.
help
Hello dear
PLEASE HELP ME
my computer have Ransomware .domn. i can delete ransomware. How to decrypt my files. i have read me file. i don’t have money that fix this crypt
To get this software you need write on our e-mail:
[email protected]
Reserve e-mail address to contact us:
[email protected]
Your personal ID:
0164fshYSf73ygdqLYgtlynVHEM3sgkspEUEIAKN1QO7M9cCGxD4Bt1
Hello Gankhorol, try to look for a decryptor on our page, if you cannot find one I’m sorry but your files cannot be recovered at this point.