Doydo
Doydo is a dangerous malware program that attacks Windows computers with the aim to encryption-lock the data stored on them. Doydo is categorized as Ransomware due to the ransom demand it gives the user that must be paid to have the files decrypted.
Once a Ransomware like Doydo infiltrates a given system, it starts to encrypt the files found on the hard-drives
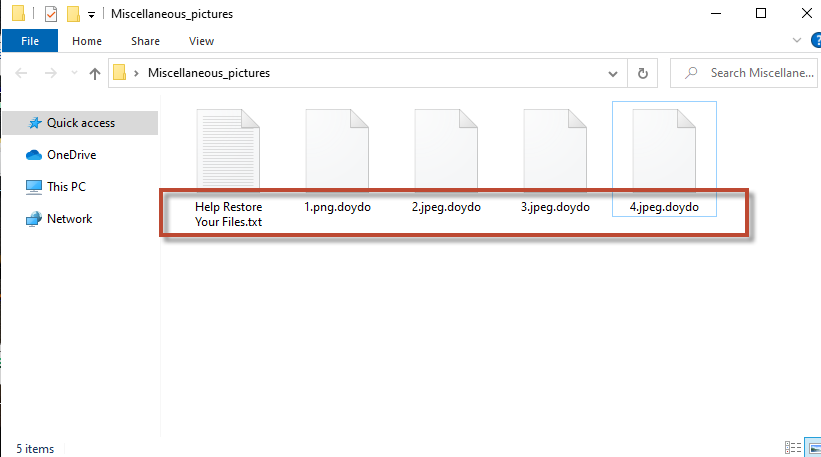
The malicious threats of the Ransomware family can be encountered on many online locations and the infections with them typically occur without visible symptoms. Once a Ransomware like Doydo infiltrates a given system, it starts to encrypt the files found on the hard-drives without any symptoms that can draw the user’s attention to the ongoing process. Upon finishing its data-encrypting task, the virus itself makes its presence known – it typically creates a text file on the user’s desktop in which there are some payment instructions related to a ransom demanded for the unlocking the sealed files. If no payment is made, the user would never get the key to recover their encrypted data meaning that the affected files would stay locked forever (or at least that is what the hackers behind viruses like Doydo would have you believe). Ransomware is undoubtedly one of the worst forms of malware and what’s worst about those threats is the lack of any universal surefire methods for handling such infections. Still, there are quite a few things you can try in order to ameliorate this unpleasant situation and deal with the consequences of the malware attack in the most optimal way.
The Doydo virus
The Doydo virus is a Windows malware program capable of restricting all access to the most valuable files of its victim. The Doydo is to force its victims to pay the hacker a big amount of money for the data’s release.
Paying the ransom may actually seem like a “necessary evil”-type of option to those of the Ransomware victims who have the needed money available to them. However, if you are one of those users who are considering the payment, you must keep in mind that there is absolutely no way to know if the hackers would actually keep any of their promises and allow you to restore your files. For all you know, they may simply keep the money you give them without contacting you back in order to send you a decryption key for your data. This is indeed a very real possibility, which is why it is inadvisable to risk your money by sending it to the blackmailers.
The Doydo file encryption
The Doydo file encryption is the method that Ransomware viruses use as a means of restricting access to the data of their victims. The Doydo file encryption is unbreakable and a key possessed by the hackers is required to unlock it.
The alternative options that you can try may also not result in the full recovery of your data but they will at least not involve a ransom payment to some cyber criminals. If you are willing to try some alternative solutions you can start by completing the removal guide for Doydo you will see below. After its completion and after the malware is gone, you can go to the second section of the manual and try out the recovery options suggested there.
SUMMARY:
| Name | Doydo |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | A Ransomware may consume high amounts of RAM and CPU while encrypting your data. |
| Distribution Method | Misleading click prompts, and spam messages are oftentimes used to spread Ransomware |
| Data Recovery Tool | Not Available |
| Detection Tool |
Remove Doydo Ransomware
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.
![]()
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!
![]()
How to Decrypt Doydo files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment