This page aims to help you remove Dozensearch “Virus”. These Dozensearch “Virus” removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
The most likely reason why you are reading this article is because you probably have had some rather unpleasant technical issues, that are likely related to Dozensearch”Virus” .
The source behind all kinds of Ads, pop-ups and banners is an browser hijacker program. It is called Dozensearch “Virus” and it is also classified as potentially unwanted software for the reasons you are already experiencing. In the text below we are going to discuss its typical characteristics and effects.
Characteristics of browser hijackers
Browser hijacker is a type of software that generates pop-ups, banners, pop-unders or other different versions of advertisements. What’s more, this software product could open new browser windows and tabs without the user’s approval and consent. There are some experts who claim that browser hijacker might actually represent an even greater issue than most malware at when it comes to the number of the infected machines. At first glance the Dozensearch “Virus” may seem as just a disturbing distraction with a great number of and possibly hard-to-close pop-up ads. Nevertheless, browser hijacker may even compromise the overall computer performance because displaying plenty of ads could use up a lot of system resources. That’s probably why this ad-generating software might be easily mistaken for a computer virus or other type of malware, a typical example being Ransomware. However, in most of the cases, browser hijacker is rather harmless. Computer viruses and ransomware in particular tend to produce greater and lasting damage.
How does browser hijacker enter your system and what are its effects?
Here come a few words on the effects and the distribution methods of browser hijacker. Most commonly, when you download and install some free software bundle from the Internet, the browser hijacker programs that may be hiding inside it also get installed. Almost all popular browsers: Chrome, Firefox and Explorer can get infected with browser hijacker.
You may become a victim of such an browser hijacker infection whenever you choose the “Quick/Default” installation option of a program installer. That is how you allow the installer to integrate into your computer any possibly unwanted program that has been lurking into the particular software bundle. Actually, most of the time such additional programs included in the software bundles are exactly browser hijacker-like.
This is one of the reasons why we always recommend that you should select the “Advanced/Custom” installation option, instead of the default one. Also, it is important that you carefully read through all menus in order to have all the information about the software that is installed and to have the opportunity to opt-out of the components and applications that you don’t really need.
However, if you realize that you have been infected, it is not a reason for panic! Don’t forget that browser hijacker DOES NOT copy and use your private information such as passwords or accounts credentials. In fact, it might only keep track of your browsing history and generate ads that match your most common search requests. However, be careful because there could also exist certain browser hijacker that might sell the data about your surfing activities to 3rd parties.
Why is browser hijacker added to some software bundles?
Advertisements make a lot of money and this is an easy way for programmers to fund their further activities. Most browser hijacker-based programs work according to the pay-per-click scheme and the more ads they generate, the more money their developers earn. It is a possible reason why there sometimes appear whole streams of constantly popping-up ads. Some of them could even be programmed to open a new pop-up on closing the previous one.
Typical features of Dozensearch
As you might expect, Dozensearch acts just like any other browser hijacker program and might sometimes have some questionable features. Some specialists have even classified it as a potentially unwanted program (PUP). However, no one has identified it as malicious software (like Ransomware, for instance). Dozensearch is not the same as a virus as it can’t damage your computer on its own.
This type of browser hijacker has been first developed as a direct-marketing tool. The advertisements it generates might come in many different forms. The behaviour of Dozensearch depends on your habitual browsing movements. In most of the cases it strives to display only ads that are relevant to your personal preferences and recent search requests.
Is it possible to remove Dozensearch?
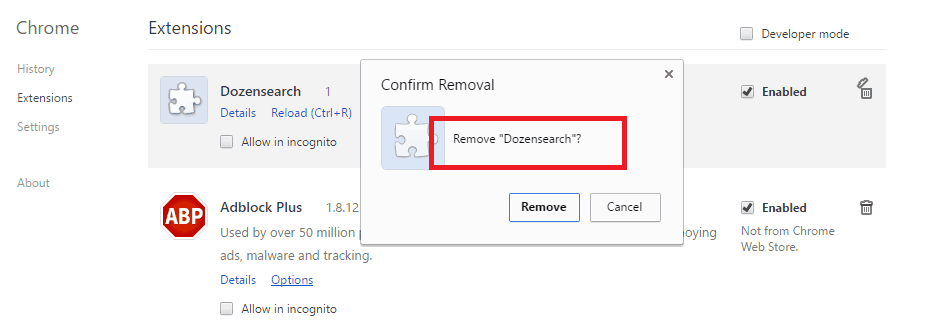
In certain cases it might be easy to uninstall Dozensearch. It is even possible that you may remove it just by choosing the uninstall option that can be accessed within the “Add/Remove programs” section of the Windows Control Panel feature, but that may not be the case always.
However, uninstalling Dozensearch from your system may require some additional actions. The removal guide below will come in handy to you if you have made a decision to remove this software.
SUMMARY:
| Name | Dozensearch |
| Type | Browser hijacker |
| Detection Tool |
Dozensearch Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Hi Sameer,
these IPs are fine. We researched them and they happened to be legit.