Easy2lock
Easy2lock is a ransomware cryptovirus that has recently been identified by security experts. Easy2lock uses encryption to lock user files and then use those files as leverage in a blackmail scheme.
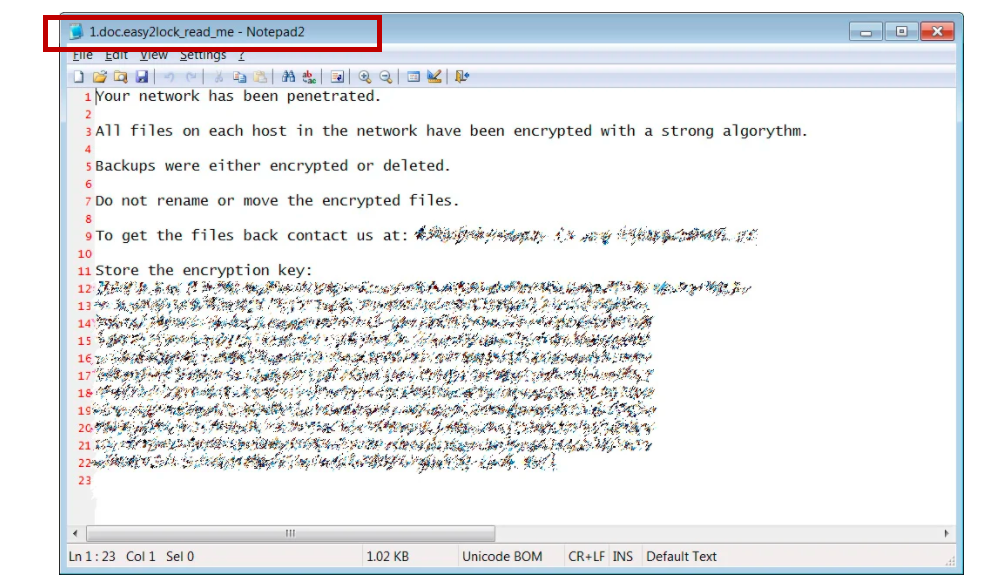
The Easy2lock Ransomware note with instructions
Ransomware actually gets its name from this very blackmail scheme, as its creators demand a ransom be paid for something – depending on the type of ransomware. In the case of Easy2lock and the file-encrypting subcategory in general, the ransom is requested for a decryption key.
In turn, this decryption key is necessary to undo the encryption that the virus has applied to the files on the infected machine. If you aren’t familiar with this concept, encryption basically means that the files on the victim’s computer are locked or made inaccessible. Hence, you lose the ability to open or in any way use the data stored on your PC as a result of the ransomware’s actions.
The targeted file types can be anything from audios and videos, photos, text documents, to databases and in some cases even system files. Once Easy2lock has completed the process, it will display a note on the desktop or some other visible place on the computer for the victim to see. And in that note, it will provide the ransom demands for the decryption key, possibly paired with threats and scare tactics to make it all seem more convincing.
The Easy2lock virus
The Easy2lock virus rarely displays any symptoms that would give its presence away. This is one of the reasons why ransomware like the Easy2lock virus is so difficult to combat.
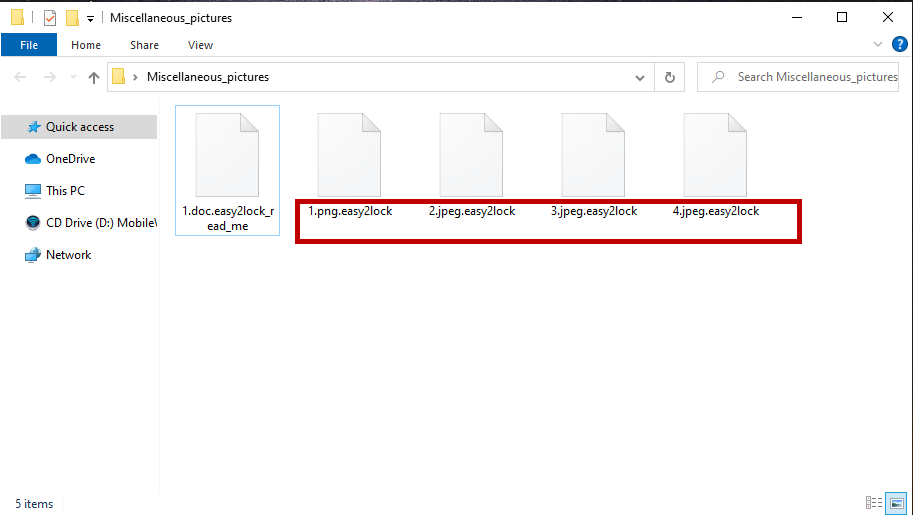
The Easy2lock virus encrypted files
In some rare instances the encryption process may cause a noticeable system slowdown due to the amount of system resources used. And if the victim user is vigilant enough, they may check the Task Manager to see what the cause is. In this event, the ransomware will usually be an unfamiliar process visible at the very top of the list. And that should prompt the user to immediately shut down their computer and seek professional assistance.
The Easy2lock file extension
It’s easy to spot the encrypted files thanks to the Easy2lock file extension. The Easy2lock file extension replaces the regular extension of the encrypted files and essentially prevents software from being able to recognize the file format.
If you’re considering paying the ransom in order to regain access to your data, you have every right to. However, we would suggest exploring other alternatives first. In the guide below we’ve included several possible solutions that you can try and none of them involve sending money to anyone.
However, before you try anything to restore your files, it is crucial that you see to the removal of the ransomware first. The removal guide below is designed to help you out with this. But there’s also a professional removal tool linked in the guide, if you would rather have this process handled automatically.
In addition, be sure to run a scan of your system for any potential Trojans as well. Trojan horse viruses are often used as a backdoor for ransomware, so there’s a chance that Easy2lock may have been delivered to you by one.
SUMMARY:
| Name | Easy2lock |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
| Data Recovery Tool | Not Available |
| Detection Tool |
Remove Easy2lock Ransomware
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.
![]()
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!
![]()
How to Decrypt Easy2lock files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment