.Efji
.Efji is a malware program that can block the access to your personal files in a matter of minutes using a military-grade encryption algorithm. Once .Efji puts its encryption on your data, it will show you a ransom-demanding message for the recovery of your data.
This type of malware has been around for about two decades but in the last five or six years, it has undergone a serious evolution, becoming one of the most dreaded computer threats that one could get their system infected with. Viruses like .Efji, .Foqe and .Mmpa are called Ransomware because their main goal is to get their victims to send some of their money to the hackers controlling the virus. There are different types of Ransomware that blackmail their victims in different ways but the most widespread Ransomware sub-type is the one that targets the files, locking them with an advanced encryption algorithm and then telling the user that a ransom must be paid in exchange for the private decryption key – supposedly the only thing that can return the locked files to their regular accessible state.
Depending on what data you keep stored on your computer and whether you have any external backups, the attack from this otherwise devastating threat may not be all that serious. For instance, if the files that the malware has encrypted are not all that important to you or if you have safe and secure copies of them stored somewhere on an external device, then there is little that the virus can do to force you to pay the ransom and the hackers won’t have any leverage they can use to blackmail you. However, sadly, in most cases, the attacked users do indeed have sensitive and important data on their computers that they cannot afford to lose and that hasn’t been backed up. In those cases, there are several different things you can do and it is very important to not act out of panic and instead assess the situation and pick the best course of action for your case.
The .Efji virus
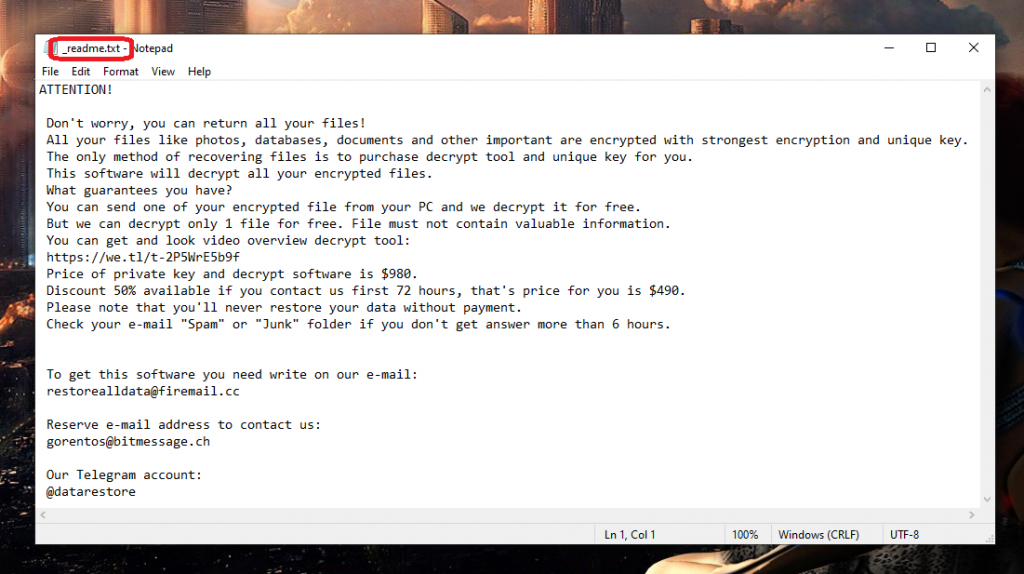
The .Efji virus is an advanced Ransomware threat with file-locking abilities that will keep your data unavailable until you pay a ransom to its creators. The .Efji virus will give you detailed instructions on how to perform the ransom payment once it completes the encryption.
Following those instructions and paying the ransom, however, is the last thing we’d advise you to do. The reason is that you stand to lose lots of money without any guarantee that the decryption key would be sent to you. That is why it is better to first explore the other options that may help you recover your data.
The .Efji file encryption
The .Efji file encryption is the advanced file-locking algorithm that this virus uses to block all access to your files. The .Efji file encryption can be unlocked if you have the private decryption key but there may also be certain ways to bypass it altogether.

We will show you some possible alternatives that may help you do that in the next guide but it is important to first go through the removal steps in order to get rid of the virus, thus preventing it from locking once again any of the data you may manage to recover.
SUMMARY:
.Efji Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Reply