Eight
Eight is a new ransomware representative that seeks to encrypt user files so that it can demand a ransom for their decryption key. Eight notifies its victims about the harmful consequences of its attack by displaying a notification on their screen.
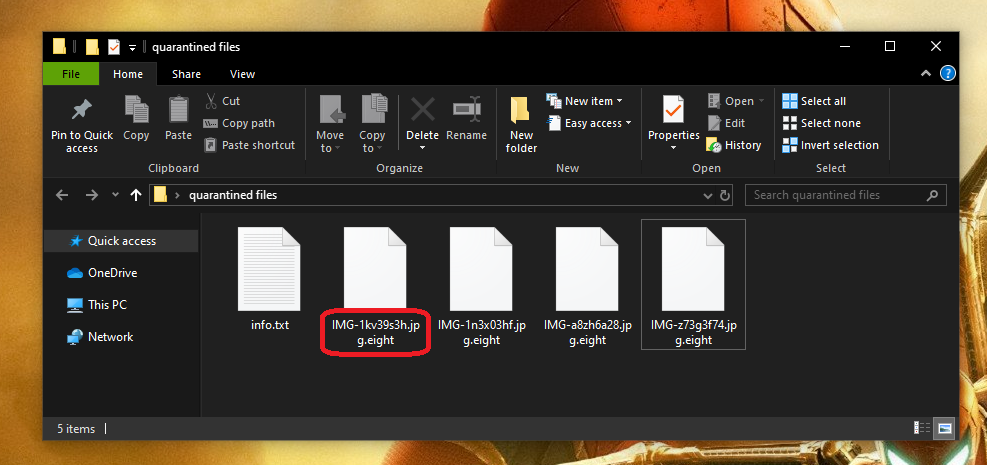
The hackers who stand behind this infection will typically ask you to transfer a certain amount of money to their cryptocurrency account in order to send you the matching decryption key for your files. They will normally provide exact instructions on how to make the payment by placing a .txt file on your screen. Unfortunately, users may lose permanent access to valuable information as a result of the attack of Eight. In addition, this could also cause significant financial losses, especially if the encrypted files are of professional value or have great importance to the user. That doesn’t have to always be the case, though. If you are here because you are looking for alternative methods that may help you remove Eight and recover your information, in the next lines you may find what you need. An important note that we must mention here is that in order to follow the file-recovery steps from the guide below, you first will need to remove the ransomware from your computer. This is important because if the virus is present on the system, any efforts to recover your information will be ineffective. Not to mention that even if you manage to retrieve some of your files, the moment you place them on the infected computer, they will become encrypted again.
The Eight Ransomware
The Eight virus is a ransomware variant that blackmails its victims to pay ransom in order to receive the decryption key for their files. The Eight virus operates in complete secrecy and it is almost impossible to detect and remove it while it is running.
Sadly, most antivirus programs prove quite ineffective in detecting ransomware variants such as Eight because the file encryption initiated by the malware is not a malicious or dangerous process. No actual damage or destruction is caused to the targeted files and, respectively, there is nothing that can prompt an antivirus response. This helps the malware take its victims by surprise and to easily scare them into paying the required ransom. Sadly, out of panic, many people opt for that and end up losing their money, oftentimes, without receiving a decryption key from the hackers.
The Eight file encryption
The Eight file encryption is a time-consuming process that converts user files into bits of data that cannot be opened without a decryption key. The Eight file encryption process runs without visible symptoms and can remain under the radar of most antivirus programs.
There is a removal guide below where we suggest several ways to avoid paying the ransom that the anonymous hackers behind Eight demand and instructions to recover your records by other means. Of course, we have to warn you that we cannot guarantee that our suggestions will work in every single case as every ransomware attack is very individual, as well as the data it affects. Nonetheless, if you want to explore some roundabouts to the ransom payment, we invite you to give our guide a try.
SUMMARY:
| Name | Eight |
| Type | Ransomware |
| Detection Tool |
Eight Ransomware Virus Removal

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt Eight files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment