*Eqew is a variant of Stop/DJVU. Source of claim SH can remove it.
Eqew File
The Eqew file encryption is a malicious technique employed by a ransomware threat to lock the files on a victim’s computer or network. The process involves transforming the files into an unreadable format that can only be unlocked with a specific decryption key held by the attackers. Once the encryption is complete, the ransomware presents a message demanding payment in exchange for the decryption key. The Eqew file encryption relies on powerful encryption algorithms, making it incredibly challenging, if not impossible, to decrypt the files without the correct key. This form of ransomware encryption is a destructive strategy used by cybercriminals to extort money from their victims, effectively blocking access to vital data and systems until the ransom is paid.
To decrypt Eqew ransomware files, start by disconnecting the infected machine from your network to stop the ransomware from spreading further. Next, determine the exact variant of ransomware that has infected your system, as different variants may require different decryption methods. To find potential solutions, visit trusted cybersecurity websites or forums where you can find specialized tools or decryption keys designed for your specific variant of ransomware. If you come across any reliable tools, download and run them cautiously, following the instructions provided to maximize the chances of successful decryption.
To remove Eqew ransomware virus and potentially restore your files, there are certain steps you can follow. Start by disconnecting the infected computer from the network to prevent the ransomware from spreading further. Then, use an antivirus or anti-malware software that is regularly updated to scan your system and remove the ransomware. After successfully removing the ransomware, it’s important to ensure that your system is fully updated and patched to minimize any future vulnerabilities. If you have backup copies of your files stored on an external device or in a cloud service, you can safely restore them after verifying that your system is clean. However, if you don’t have backups, you may consider exploring data recovery options or seeking assistance from a professional cybersecurity service to check if there are any decryption tools available for the specific variant of ransomware you encountered.
Eqew Virus
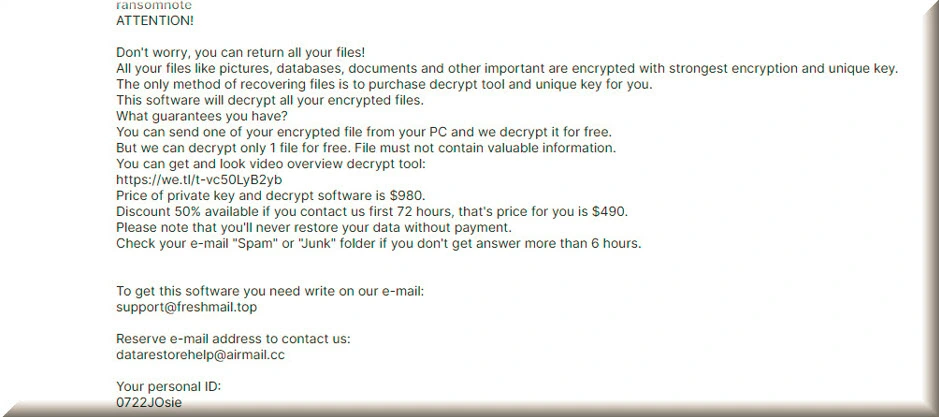
The Eqew virus is a malicious piece of software from the ransomware category that employs an advanced encryption process to lock the files found on an infected computer. It demands a ransom from the victim to regain access to the encrypted files, following the instructions set by the malware creators. If you discover that your computer has been infected with the Eqew virus, it is important to approach the situation with a clear mindset. Although the option of paying the ransom may appear tempting, it is not recommended because there is a possibility that the hackers may take your money without providing the necessary file decryption key, making this the worst course of action.
Eqew
Ransomware infections, such as Eqew, Jzie, Eqza are malware programs that have a distinct objective. Rather than causing damage or stealing data, their main purpose is to seize control of files and demand a ransom for their release. These ransomware variants utilize sophisticated encryption codes to lock the targeted files, rendering them inaccessible to the victim. To communicate their demands, the Eqew ransomware presents a text message on the victim’s desktop, outlining the required payment to regain file access. Typically, a specific deadline is provided, usually within a day or two, for the ransom to be paid. If the payment is not made or is refused, the victims are often threatened with permanent loss of access to their files.
.Eqew
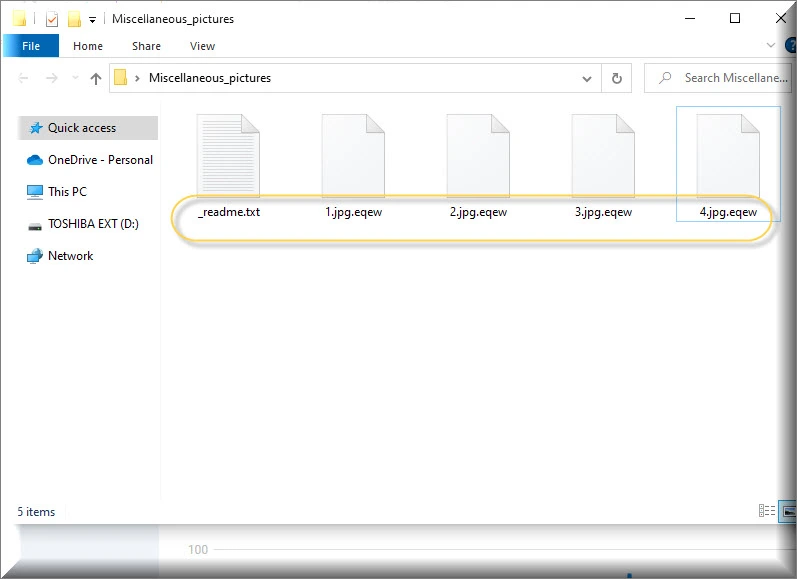
When the Eqew ransomware infects files, it adds a distinctive .Eqew suffix to them, making them inaccessible and unusable without a specific decryption key. This suffix serves as a way for the attackers to hold the victim’s files hostage, demanding a ransom payment in exchange for the decryption key. The ransomware that uses the .Eqew suffix typically spreads through deceptive tactics, including illegal downloads, spam messages, and Trojan Horse backdoors. Therefore, it is crucial for users to be cautious when downloading files from untrustworthy sources and stay alert to suspicious emails or attachments to reduce the risk of falling prey to this malicious software.
Eqew Extension
When the Eqew ransomware infects your files, it encrypts them and modifies their original extensions or adds new ones. This alteration is noticeable when you see the presence of the Eqew extension appended to your regular files. For instance, a file that is regularly named “image.jpg” could be renamed to “image.jpg.Eqew”. This change in file extensions serves as a clear indication that your files have been compromised by ransomware. If you encounter such modifications, particularly the Eqew extension, get your system equipped with a good antivirus program and follow the instructions in the guide below to remove the threat safely and quickly.
Eqew Ransomware
During the Eqew ransomware encryption process, the symptoms may be minimal and almost invisible to the user. This malware typically operates silently in the background, encrypting files without causing noticeable disruptions or changes to the system. The encryption process is designed to be covert, aiming to maximize the attacker’s chances of success. As a result, users may not immediately realize that their files are being encrypted until they try to access them and encounter error messages or find their files inaccessible. These subtle symptoms make it challenging to detect the Eqew ransomware at an early stage, highlighting the importance of proactive security measures and regular backups to mitigate the potential impact of such attacks.
What is Eqew File?
When a file is encrypted by ransomware, it’s not necessarily a dangerous file itself. Think of it as a regular file on your system that has been put under lock and key using encryption. The Eqew file encryption process scrambles the contents of the file, making it unreadable and inaccessible without the decryption key. But rest assured that the Eqew file itself is not inherently dangerous— it’s just locked away from you until you find a way to break free from the ransomware’s grip. The danger lies in the fact that you’re being held hostage by cybercriminals who demand a ransom payment in exchange for the key to unlock your valuable files, which is frustrating and can cause a lot of stress.
SUMMARY:
| Name | Eqew |
| Type | Ransomware |
| Detection Tool |
*Eqew is a variant of Stop/DJVU. Source of claim SH can remove it.
Eqew Ransomware Removal

The first step of this guide explains how to boot into Safe Mode. In order to remove the malware from your computer, we recommend that you begin by clicking on the Safe Mode link and completing the steps there.
Please bookmark this page so that you don’t have to search for the Eqew removal instructions every time you restart your computer.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Eqew is a variant of Stop/DJVU. Source of claim SH can remove it.
Eqew ransomware is difficult to detect because it can remain invisible for an extended period of time and cause significant damage to the system.
When this ransomware infects your computer, one of the most difficult things you’ll have to do is discover and stop its malicious processes. Please follow the instructions in the following paragraphs to ensure the safety of your computer.
Press CTRL+SHIFT+ESC on your computer’s keyboard at the same time. Focus your attention on any processes that could be related to the hazard. The Processes tab in Windows Task Manager shows this information.
The next step is to investigate any suspicious processes’ associated files. Select Open File Location by right-clicking on a process that appears suspicious.

For your protection, you can run a free scan of the files associated with this process using the online scanning tool provided below.

You must first end the processes associated with any of the files that have been flagged as potentially dangerous by right-clicking on them and selecting End Process. After that, return to the infected files and delete them from their file location.
![]()
You should also disable any startup items that the malware may have installed without your knowledge, in addition to shutting down the malicious processes associated with Eqew. To see if there are such dangerous items on your system, go to the Startup tab in System Configuration.
Entering msconfig in the Windows search bar will open up the System Configuration window. In the Startup tab, take a look at the items listed there:

Your first priority should be to remove any ransomware-related startup items. When the system boots up, look for startup components that are not normally associated with the apps that are running. Unchecking the checkboxes will disable them.
![]()
Remove any registry entries found in your registry editor in the fourth step of this guide to ensure that the ransomware is completely removed and no harmful components are left behind.
To do that, type Registry Editor in the windows search field and press Enter. Use the CTRL+F keyboard shortcut and search for ransomware-related files by typing the malware’s name in the Find box. After that, click Find Next to begin the search. A dangerous entry can be removed by right-clicking on it.
Attention! When dealing with Registry entries, make sure you are removing only the ones that are associated with ransomware. Making any other changes or deleting files that are unrelated to the infection may lead to serious system corruption. If you need help, please use the anti-malware program linked on this page that can help you get rid of the virus and other malware on your computer.
Check out the locations below to see if there are any other files or sub-folders that may be malicious. You can open them by searching for them in the Windows search field and then pressing Enter.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Any newly added files or subfolders that appear suspicious should be thoroughly investigated. Delete everything in the Temp folder to rid your computer of any potentially harmful temporary files.
You’ll then want to check your computer for any malicious changes to the Hosts file. The following command can be entered in the Run dialog box by holding down the Windows key and the R key simultaneously:
notepad %windir%/system32/Drivers/etc/hosts
Any suspicious IP addresses under “Localhost” in the Hosts file should be reported to us so that we can investigate further. Don’t hesitate to ask us anything in the comments section if you have any questions or concerns.

![]()
How to Decrypt Eqew files
Dealing with the consequences of ransomware data encryption can be difficult both for normal users, as well as experienced professionals. The good news is that there are some file-restoration options that allow you to decrypt encrypted data. Before you dig deeper into them, though, you must first determine the type of Ransomware you’re dealing with in order to begin the process of file recovery. The file extensions at the end of the encrypted files are good place to look for this information.
New Djvu Ransomware
STOP Djvu is one of the most recent Djvu Ransomware versions that you may encounter. You’ll be able to tell this particular threat apart from others because it typically adds the .Eqew file extension to encrypted files.
Those who have had their data encrypted by this new variant may have some hope of recovering it, especially if an offline key was used to encode their files. A file-decryption tool that can help you recover your files can be downloaded by clicking on the link below.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Decryption
Run the decryption tool file you’ve downloaded by clicking “Run as Administrator” and then clicking “Yes” to begin. Please read the included instructions and the attached license agreement carefully before continuing to use this product. The decryption process will begin as soon as you click the Decrypt button.
If you need to decrypt files encoded with unknown offline keys or online encryption, please note that this program may not be able to decrypt them. If you have any questions or concerns, please feel free to post them in the comment section below this guide.
Important! Before attempting to decrypt data that has been encrypted, be sure to thoroughly scan your computer for ransomware-related files and dangerous registry entries. If you have Eqew-related malware on your computer, this page’s free online virus scanner and the recommended anti-virus software can help you remove it.

Leave a Comment