This page aims to help you remove Error 268d3. These Error 268d3 removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows. But before we go about with the removal process, let us have a look at what exactly it is we are dealing with as well as how it is being spread around.
What is Error 268d3?
According to security experts, Error 268d3 is not a virus, but rather a Browser Hijacker. A Browser Hijacker is different from a virus in that a virus is generally malicious and will cause some type of harm to the computer in which it resides. An example for a nasty computer virus is Ransomware. Of course Ransomware viruses are a lot nastier than Browser Hijackers. In comparison Browser Hijackers are typically non-malicious and only seek to display advertisements or other fake messages on your screen. Viruses and Browser Hijackers do share many similarities though, it is for this fact that you will probably want them removed from your machine.
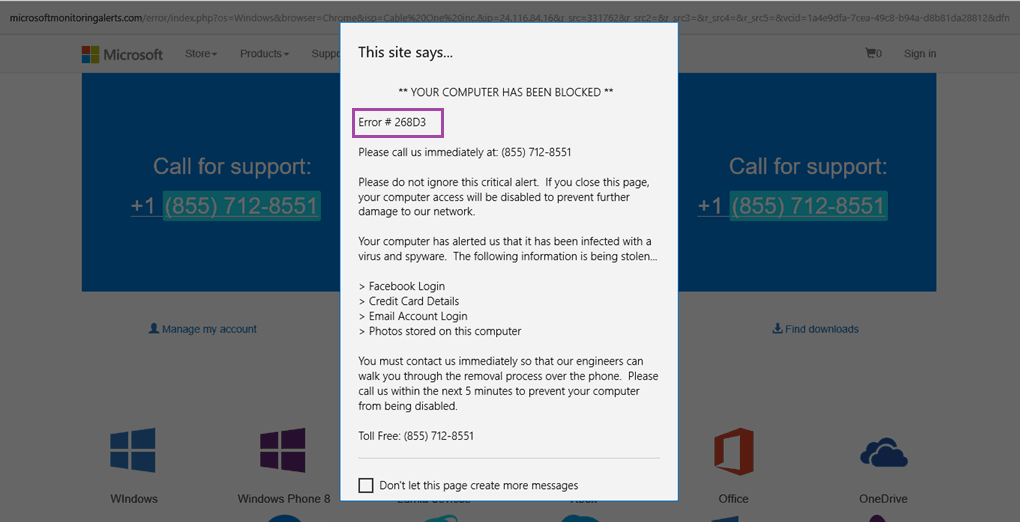
Error 268d3 is an absolute scam and it is in no way related to either the Microsoft or Windows OS support. You should not believe a word this warning message states and should instead follow our instructions to fix your problem.
Error 268d3 is designed in such a way that it is able to integrate itself onto your browsers. This may appear in the form of a search toolbar or it may not create any interface at all. By integrating itself onto your browser, this Browser Hijackers is, then, able to track all your browsing patterns and history, search queries and site visits. It will know what you are inclined towards; your preferences, tastes and likes. All these information will be collected and used to help it to generate ads that are specially designed for you. These pop-ups may look genuine and convincing. These messages appear as banners, pop-up ads and boxes or even as a separate window and they will feature coupons and deals of items that you are inclined towards.
These messages are usually intrusive and most Browser Hijackers is particularly aggressive. On top of that, it may also be hard to get rid of and its ad-generation rate is high for most people’s tastes. Furthermore, this Browser Hijackers may cause your computer’s functioning and responses to slow down due to the extra load imposed by the program. This is because it is running covertly in the background without your knowledge. Therefore, it is a good thing that you are seeking to remove this Browser Hijackers.
Regardless the form and message of the ads, you need to always bear in mind to not click on them. These ads have no real basis to the messages it claimed as they are generated by the Browser Hijackers itself. Uninstalling the Browser Hijacker from your machine is the only way to get rid of this for good.
What will happen if you believe the message?
If you happen to, against all odds, click onto the ads, you will be directed to another page. Sometimes, this page will be that of a site that you frequented or one that you recently visited. In such a case then, even though you might be able to see the deal that the ad featured, it is probably something that you’ve already known about.
Sometimes, the page in which you are being directed to, is one of the many third-party’s pay-per-click sites. By entering such sites, you are aiding the creators to earn some form of income. This gives them further incentives to continue spreading Error 268d3 as well as creating similar programs.
There might also be occasions when the page that you being directed to is, actually, a portal for other Browser Hijackers to enter and access your computer. This will cause your computer to have an increased number of programs that are generating and displaying ads at random, unexpected times.
Another possibility is that the page in which you are being directed to, aggressively prompts the download of a certain program. This program may be bad news, as they are often overpriced for what they do or may even be a potential security risk. This could become a serious form of security threat and problem for you.
In the very unfortunate cases that you call the number as shown on the pop-up you will be no doubt exposing yourself to a very serious security risk. Especially if you allow the fake MS technicians to access your computer.
How did you get infected in the first place?
Sometime in the recent past, you must have had engaged in some form of free (and possibly illegal) program downloads. Creators tend to tie Error 268d3 up together with the free programs into bundles. These bundles are then made available as a set for downloading. This is why the practice of creating these packages is called bundling. In such cases, the extra software baggage usually goes unnoticed by the user.
If you do engage in downloading free programs, all hope is not lost! You only have to exercise extra caution and be diligent during the installation process. One important thing to note is that this Browser Hijackers is unable to function if it has not been installed. Therefore, during the installation process, choose the “Custom Installation” option instead of the “Automatic Installation” option. In “Custom Installation”, there will be a stage where you will be provided with a list of the files that are to be installed onto your computer. At this step, look carefully through the names of all the files. If there are any names that jumps out at you as being weird, funny, questionable or strange, uncheck them immediately.
SUMMARY:
| Name | Error 268d3 |
| Type | Browser Hijacker |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Error 268d3 Scam Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Reply