This page aims to help you remove Everyday Tab. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
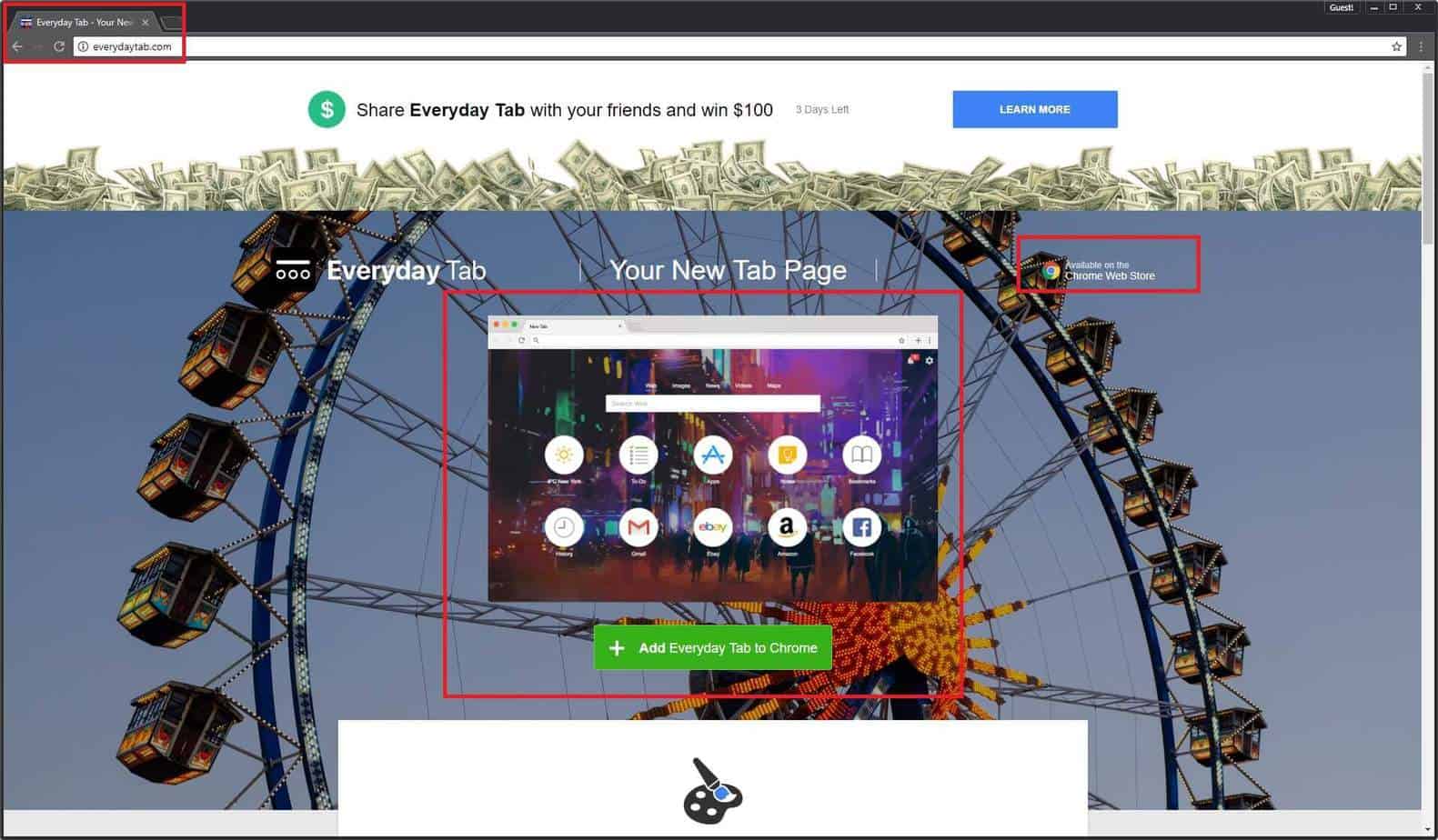
If all of your browsers have begun the annoying broadcast of online advertisements (such as pop-ups, banners, new tabs tabs), or in case their usual homepages and search engines have somehow been substituted by new ones. Also, if your browser apps have started redirecting you to unfamiliar web locations, it is likely that your PC has caught a member of the browser hijacker category. Its name is Everyday Tab and it may affect all of the most common browsers such as Chrome, Firefox, Opera or Explorer, and the less famous browsers, too. Below we have gathered all the info you may need in order to fight Everyday Tab successfully.
What does the term “browser hijacker” really mean?
To begin with, all browser hijackers are programs that have the aforementioned features; all of them can modify the settings and the appearance of your browser apps as mentioned above. Such consequences might greatly annoy you with the ad streams, or default homepage/ search engine modifications. The probable redirection that may result from the contamination caused by Everyday Tab could indeed be very irritating because the broadcast pages might be absolutely unfamiliar, or even shady-looking. Furthermore, you were not really asked to approve of the recently enabled homepages and search engines your browser apps may start showing. To summarize, the way such a hijacker could affect any PC may be harmless indeed, but it could still be awfully irritated.
Does Everyday Tab fall into any malicious category?
As a member of the browser hijacker category, this product never acts like any kind of malware at all. To illustrate our statement with examples, any representative of Ransomware is able to self install on your device, and after that access your storage spaces and encrypt all the important data it can find on them. Such harmful effects are completely impossible when it comes to a browser hijacker infection. Nonetheless, why are most browser hijackers so irritating? All the annoying changes Everyday Tab could result in are actually legal, and lead to no actual harm. Its designers have make this piece of software simply promote new homepages, less famous search engines, products, services, etc. This type of promotional activity is neither malicious, nor illegal. However, the flow of pop-ups and banners, which is perhaps overwhelming you while you are browsing, could not be what you want to experience at all. In spite of that, hijackers aren’t even close to what we can consider cyber threats. Actually, the reason why programmers create hijackers is that by using them for advertising they can accumulate big profits.
The tips to follow in order to remove Everyday Tab:
Scroll down and carefully go through the Removal Guide we have attached here.
If Everyday Tab is not a virus, how has your PC ended up infected?
Everyday Tab may come from plenty of possible different sources. Any torrent or a shareware-distributing web page could have it as a component, and right after you open or download anything from such a website, you may give Everyday Tab your approval to get installed on your device. It might also be hiding inside the infamous program bundles. Nonetheless, the act of simply downloading a bundle is not what infects your device with an ad-generating piece like this. Having it installed improperly, however, could leave you under the attack of many bothering ads.
What does ‘a bundle’ mean? The way to install a program bundle correctly:
Generally speaking, a bundle is a package of several free programs (apps/games), assembled and spread together, usually for free. The wisest way to have such a bundle installed on your device (or simply any separate program from it), is not to give your permission for the entire content of such a bundle to get inside your PC. The installation features that provide the chance to opt in and out of any program/ bundle components are the Custom or also the Customized (the Advanced) ones. Select whichever one of them is available for the successful and safe completion of any installation process.
In addition, we need to also point out the installation possibilities you cannot afford to select if you want to keep your computer hijacker-free. They are the ones that provide an easy installation process. Most commonly, they are labeled as the ‘Recommended’, ‘Easy’, ‘Quick’ or ‘Default’ ones. Don’t select any of them for the safety of your PC!
SUMMARY:
| Name | Everyday Tab |
| Type | Browser Hijacker |
| Detection Tool |
How to Uninstall Everyday Tab
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment