Exe.io
Experts classify Exe.io as a typical browser hijacker application. This implies that Exe.io targets the browsers on infected computers. Exe.io is compatible with most popular web browsing programs such as Chrome, Firefox and Edge.
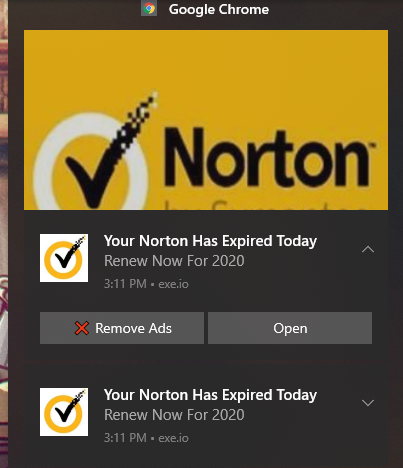
For example, Exe.io may be the reason that your browser has all of a sudden started triggering page redirects to random web locations. In addition, this is the program you may hold responsible for all the numerous popups, banners and other types of online ads that have all of a sudden started spamming your screen. And have you noticed your new search engine that mysteriously replaced the old one? Or the fact that it’s been displaying an unusually large number of sponsored search results for your queries? That, too, is the work of Exe.io.
Furthermore, this software may have also changed your browser’s homepage and added some new toolbar or other elements. And all of this is done in the name of making a profit for its developers, which is really the sole purpose of any browser hijacker. And what many users claim to be quite frustrating is the fact that once they start witnessing all these changes, no matter how hard they try – they can’t seem to get rid of them. It is as though the browser has a mind of its own, and that’s not too far from the truth in this case.
Exe io
For one, the presence of a hijacker like Exe io is likely to make your system more vulnerable to actual threats such as the aforementioned malware and viruses. Long-term exposure to so many ads and unsolicited redirects to various web addresses may at some point land you on a page or website that may be infected with Trojans, ransomware and all sorts of other malicious code.
In order for you to be able to recover your browser settings to their previous state, you will first need to remove Exe.io from your PC. And this usually requires a little extra effort compared to regular types of software. But never worry, as below we have put together a detailed removal guide that will show you exactly how to handle this browser hijacker infection in the most secure and efficient way.
The Exe.io Virus
Once the Exe.io Virus has become part of your browser, it will change some of its configurations in order to enable online advertising practices directly within your browser. This will ultimately have a great impact on your online sessions and will most likely decrease your browsing experience.
You have every right to be worried about the safety of your system if you’re concerned about the nature of this browser hijacker. And while most experts agree that Exe.io is not some malware or a virus and it cannot actually inflict any harm, they still see it as potentially unwanted for a number of reasons.
For this reason we also highly recommend trying to avoid interacting with any of the content generated and displayed by Exe.io. But that should also go for other online ads you come across when browsing the web.
SUMMARY:
Exe.io Virus Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning. You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Reply