Extension Settings
Just like other undesirable software types, browser hijackers like Extension Settings typically rely on stealthy methods of distribution so as to reach more users. This doesn’t mean that a hijacker would infect your machine like an actual malicious virus would but it’s still highly likely that you may get an app like Extension Settings installed on your computer without initially realizing it.
If your Chrome, Safari, IE, Firefox or whatever other browsing programs you typically use has recently started to behave in an odd way, displaying many intrusive ads, spamming you with page redirects and having some of its elements such as the search engine tool and the starting page replaced, it is understandable if you suspect that there might be some kind of malicious virus inside your PC. However, if the aforementioned symptoms are the only ones that you (or rather your PC) are experiencing, then the most likely cause for this is a software piece of the browser hijacker family. Extension Settings, for example, is a recently reported representative of the said software group. It is a software component similar to a browser add-on which typically streams ads and page redirects and also affects the way the user’s browser works without asking for permission. Of course, this could be really irritating and is likely to aggravate most users who come to experience it but if you are presently struggling with a similar issue, know that it is likely not coming from some malicious infection with a nasty virus program such as a Trojan Horse, a Rootkit, a Ransomware or some other similar cyber threat. Hijackers are usually not harmful in themselves as they are mostly used for the purposes of online advertising. The creators of such apps tend to earn significant amounts of money if they manage to get their products installed onto a big enough number of machines since the greater exposure the hijacker-generated advertising materials receive, the bigger the end-profit that the hijacker’s creators would gain. Still, though, despite the relative harmlessness of most hijacker apps, such software components are undoubtedly some of the most irritating and unpleasant to have forms of software which is also the main reason why we’ve come up with this current write-up. In this article, our goal is to inform you about the main characteristics of hijacker apps and also to help you remove them from your PC if you currently have one such software piece inside your system. The guide below will help you deal with the recently released Extension Settings Virus as this is one of the most widespread hijackers at the current time. Make sure you follow the instructions and also use the suggested removal tool if you need extra help and remove the hijacker.
The Extension Settings Virus
The honest answer here would be yes – theoretically, a hijacker the likes of Extension Settings, Lookaside.fbsbx.com, Realsrv.com could indeed lead to the exposure of your computer system to threats like Ransomware, Trojans and so on. However, this doesn’t mean that such is the intended purpose of the hijacker. It’s just that some of the ads coming from it might be unsafe and unreliable if their original sources are shady.
We advise you not to interact with any of the promotional contents displayed on your screen while the hijacker’s still in your system and browser. The same goes for using the custom search engine, toolbar, new-tab page and homepage that such an app might have tried to impose on your browsing program. All in all, the safest course of action if Extension Settings or any other similar app is presently on your computer would be to take the necessary actions towards uninstalling the unwanted software and fully removing any leftover data and files that it might have left behind so as to ensure that there’s no way for the hijacker to return.
How you can land a hijacker and what you should do in order to keep your PC clean from now on
For instance, if you open the attachment of a spam social network message or of a spam e-mail, you might actually unknowingly download a hijacker. The same goes for interacting with obscure and questionable online offers, sketchy update requests, obscure adverts and so on. Another thing that could get you a hijacker is if you use the Quick/Default setup settings when installing new software. Oftentimes, programs have additional software components bundled with their installers and if the program you’re trying to install has a hijacker bundled with it and you use the default setup option to install it, then you are likely going to get the hijacker. However, if you use the Advanced setup menu and from there uncheck any added components you deem undesirable, the bundled app wouldn’t get inside your system after the installation has been completed.
SUMMARY:
| Name | Extension Settings |
| Type | Adware/Browser Hijacker |
| Detection Tool |
Remove Extension Settings Virus
To try and remove Extension Settings quickly you can try this:
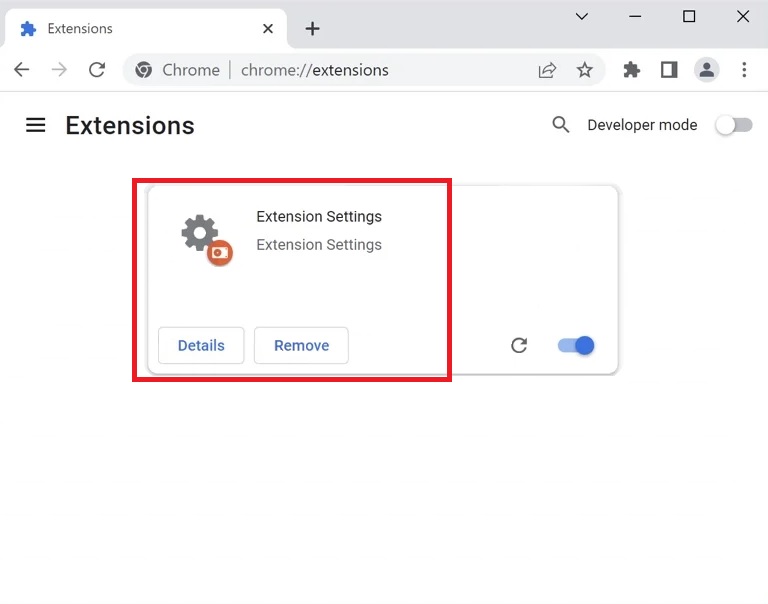
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Extension Settings extension (as well as any other unfamiliar ones).
- Remove Extension Settings by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Extension Settings and any other suspicious items.
If this does not work as described please follow our more detailed Extension Settings removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab (the “Details” Tab on Win 8 and 10). Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them.
Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Open the start menu and search for Network Connections (On Windows 10 you just write it after clicking the Windows button), press enter.
- Right-click on the Network Adapter you are using —> Properties —> Internet Protocol Version 4 (ICP/IP), click Properties.
- The DNS line should be set to Obtain DNS server automatically. If it is not, set it yourself.
- Click on Advanced —> the DNS tab. Remove everything here (if there is something) —> OK.


- After you complete this step, the threat will be gone from your browsers. Finish the next step as well or it may reappear on a system reboot.
Right click on the browser’s shortcut —> Properties.
NOTE: We are showing Google Chrome, but you can do this for Firefox and IE (or Edge).

Properties —–> Shortcut. In Target, remove everything after .exe.

![]() Remove Extension Settings from Internet Explorer:
Remove Extension Settings from Internet Explorer:
Open IE, click ![]() —–> Manage Add-ons.
—–> Manage Add-ons.
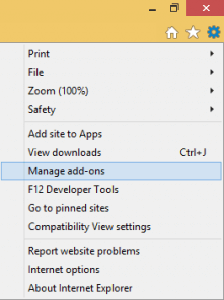
Find the threat —> Disable. Go to ![]() —–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
—–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
![]() Remove Extension Settings from Firefox:
Remove Extension Settings from Firefox:
Open Firefox, click ![]() ——-> Add-ons —-> Extensions.
——-> Add-ons —-> Extensions.

![]() Remove Extension Settings from Chrome:
Remove Extension Settings from Chrome:
Close Chrome. Navigate to:
C:/Users/!!!!USER NAME!!!!/AppData/Local/Google/Chrome/User Data. There is a Folder called “Default” inside:
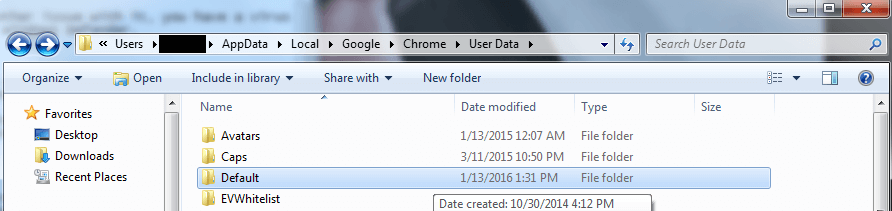
Rename it to Backup Default. Restart Chrome.

Type Regedit in the windows search field and press Enter.
Inside, press CTRL and F together and type the threat’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment