*Source of claim SH can remove it.
ExtensionInstallForcelist
ExtensionInstallForcelist is a Mac program that actively promotes other websites by producing sponsored ads and page redirects without any control. As soon as it gets installed, ExtensionInstallForcelist introduces new elements in the main web browser, including new toolbars, redirect buttons, a new search engine and a homepage.
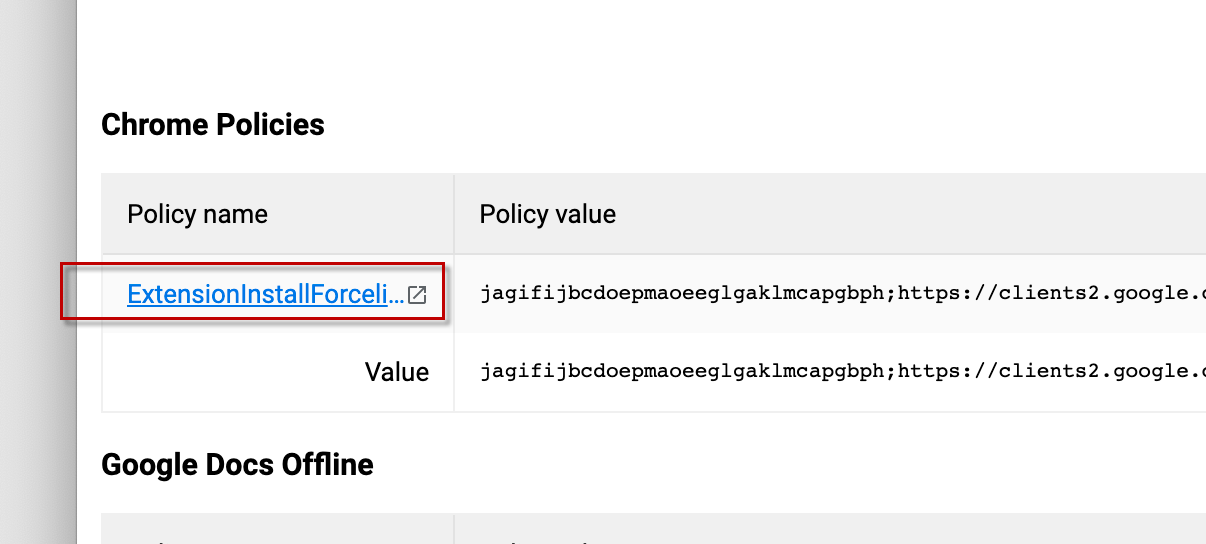
ExtensionInstallForcelist is suitable to control almost every regular Mac web browser, but the most popular targets include Firefox, Chrome and Safari. This does not mean, however, that you will be protected if you change your current web browser or use another one. ExtensionInstallForcelist can change any web browser’s settings and install its own supported homepage that automatically redirects you to different pages. This is why this program is also called a browser hijacker.
The main target of browser hijackers is to generate income for their developers through paid web page redirects and clicks on pay-per-click ads. That’s why they aggressively promote certain banner ads, pop-up messages and redirect prompts on the screen of the hijacked browser and place them in such a way that the users have no other option but to click on them. The more the clicks, the greater the profit.
ExtensionInstallForcelist for Mac
ExtensionInstallForcelist for Mac is a program that is specialized in the display of ads and auto redirects to pages needing promotion. ExtensionInstallForcelist for Mac can change Mac web browser settings and install helpers such as a new search engine, a sponsored homepage or fast forward buttons to specific URLs.
Essentially, the role of these browser modifications is to ensure that you will be prompted to visit and click on the specific promotional messages and web addresses that the hijacker advertises. That’s why the newly installed search engine will predominantly show sponsored results as the first results in your search, while the new homepage will reroute you to a different URL as soon as you open a new tab.
The major problem that a lot of users face is that they struggle with finding relevant search results for their queries due to overload with sponsored materials and frequently land on web locations full of sketchy offers and questionable links. Many people also fear of accidental exposure to virus transmitters, and fake web ads that could potentially deliver Ransomware, a Trojan or other viruses to their system. Moreover, they are frequently trapped in attempts to remove the nagging promotional messages and unwanted browser modifications.
What is ExtensionInstallForcelist?
ExtensionInstallForcelist is a Mac plugin for browser optimization that shows pay-per-click ads. When installed in the system, ExtensionInstallForcelist typically advertises specific products and services and redirects users to their sponsored web pages.
One positive thing about being infected with a browser hijacker like ExtensionInstallForcelist is that this program is not interested in harming your Mac machine the way that a real virus, a Trojan or a Ransomware infection would. However, this software can rarely provide its users with useful features that can compensate for its intrusive online advertising behavior. That’s why programs like ExtensionInstallForcelist are commonly considered to be potentially unwanted and are uninstalled from the system with no regrets.
The ExtensionInstallForcelist app is a program capable of showing a variety of promotional web materials on the screen of any Mac web browser. The ExtensionInstallForcelist app may also redirect user searches to sponsored websites and, in this way, expose the device to potential threats.
In order to uninstall the browser hijacker and protect your Mac from possible encounters with ads and URLs that contain online hazards, we recommend that you use the manual removal guide below. If you don’t have the time and the patience to follow the instructions and want to remove ExtensionInstallForcelist faster, there is a convenient removal tool for automatic assistance.
SUMMARY:
| Name | ExtensionInstallForcelist |
| Type | Browser Hijacker |
| Detection Tool |
*Source of claim SH can remove it.
ExtensionInstallForcelist Removal from Mac
To remove ExtensionInstallForcelist from Mac, you should start with finding and stopping its process, then delete the hijacker files, uninstall any unwanted apps, and lastly clean your browsers.
- For starters, open the Activity Monitor utility, check it for hijacker processes and quit anything suspicious.
- Next, find the following folders on your Mac and delete from them any questionable files that may be from the hijacker: /Library/LaunchAgents, ~/Library/LaunchAgents, /Library/LaunchDaemons, ~/Library/Application Support.
- Thirdly, open the Applications folder and if you find in it any potentially unwanted applications, uninstall them.
- Finally, to remove ExtensionInstallForcelist, open each of your browsers, check for suspicious settings and add-ons, and remove anything that seems like it mustn’t be there.
This overview of the steps needed to delete ExtensionInstallForcelist may be enough for some users to effectively take care of the hijacker problem but if any of you need more details on how to complete one or more of the steps, please have a look at the instructions below.
Detailed ExtensionInstallForcelist Removal
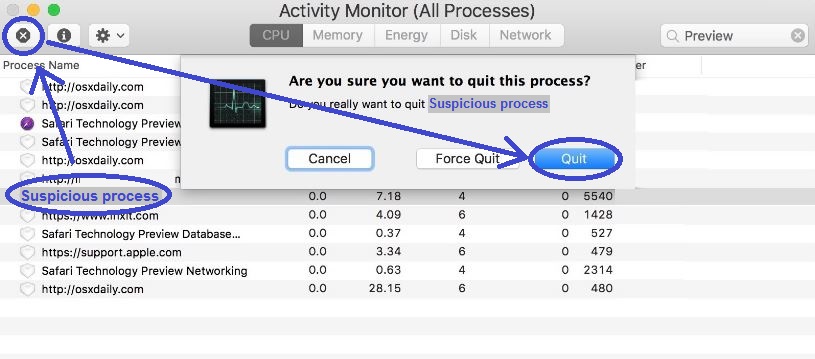
Step 1: Quitting the ExtensionInstallForcelist process(es)
Click Finder from the top of your menu bar, click on Applications from the left, and then access the folder labelled Utilities. From it, start the utility named Activity Monitor and when it opens, look through the processes listed in them, focusing on the ones with the highest RAM, CPU, and battery life consumption.
If any of those most resource-intensive processes seems to have an odd or unusual name that you think could be related to ExtensionInstallForcelist, look up that name on the Internet to see what other users or researchers have said about it. Chances are that if the suspected process has anything to do with the hijacker, this should quickly come up in the search results.
If your quick research has led you to information from a reliable source that suggests that the process in question could be from the hijacker, be sure to quit that process – click on it, select the X in the top-left, and then select Quit.
Step 2: Delete rogue hijacker files
WARNING! READ CAREFULLY BEFORE PROCEEDING!
The next thing you must do is visit several folders where unwanted software and malware tend to create rogue files in order to gain persistence and more control over the system.
First, press the following keyboard combination: Command + Shift + G. Next, one by one, copy each of the following folder locations, place them in the Go to Folder search field, and click GO:
- /Library/LaunchAgents
- ~/Library/LaunchAgents
- /Library/LaunchDaemons
- ~/Library/Application Support
Once you get to each of those folders, scan all files in them that have been created since the hijacker first appeared in the system. We suggest using the following online scanner that we offer for free on our site and that can be used directly from the browser:

Needless to say, if a given file is flagged as a potential threat, you should delete it by dragging it to the Trash.
When you open the ~/Library/Application Support folder, instead of files, look for unwanted/suspicious sub-folders. You can still use the scanner to scan the files in the different sub-folders to figure out if any of them contain malware. If a given folder has unwanted/malicious files in it, you should delete that entire sub-folder (and not only the malicious file).
Step 3: Check the Applications Folder
It is common for hijackers for Mac to get distributed via seemingly normal apps that carry the unwanted software component. Therefore, open Finder > Applications again and look for questionable-looking items that are in it. If any of the apps there seem unfamiliar, unwanted, or suspicious, it’s best to delete that app by dragging it to the Trash.
Once you are done with this step, be sure to Secure Empty the Trash.
Uninstall ExtensionInstallForcelist from Safari
To uninstall ExtensionInstallForcelist from Safari, clean the browser from rogue add-ons and then refresh its settings.
- Start by opening Safari, clicking the browser’s menu from the top of the screen, and then click the Preferences option.
- From the Preferences bar, click on Extensions and explore the items in the page that opens.
- If any of the extensions listed on that page are unfamiliar to you or seem unwanted/unneeded, uninstall them to remove ExtensionInstallForcelist from Safari.
- Quit the browser, restart the computer, and open Safari again – browser the Internet for some time to see if the issue is gone.
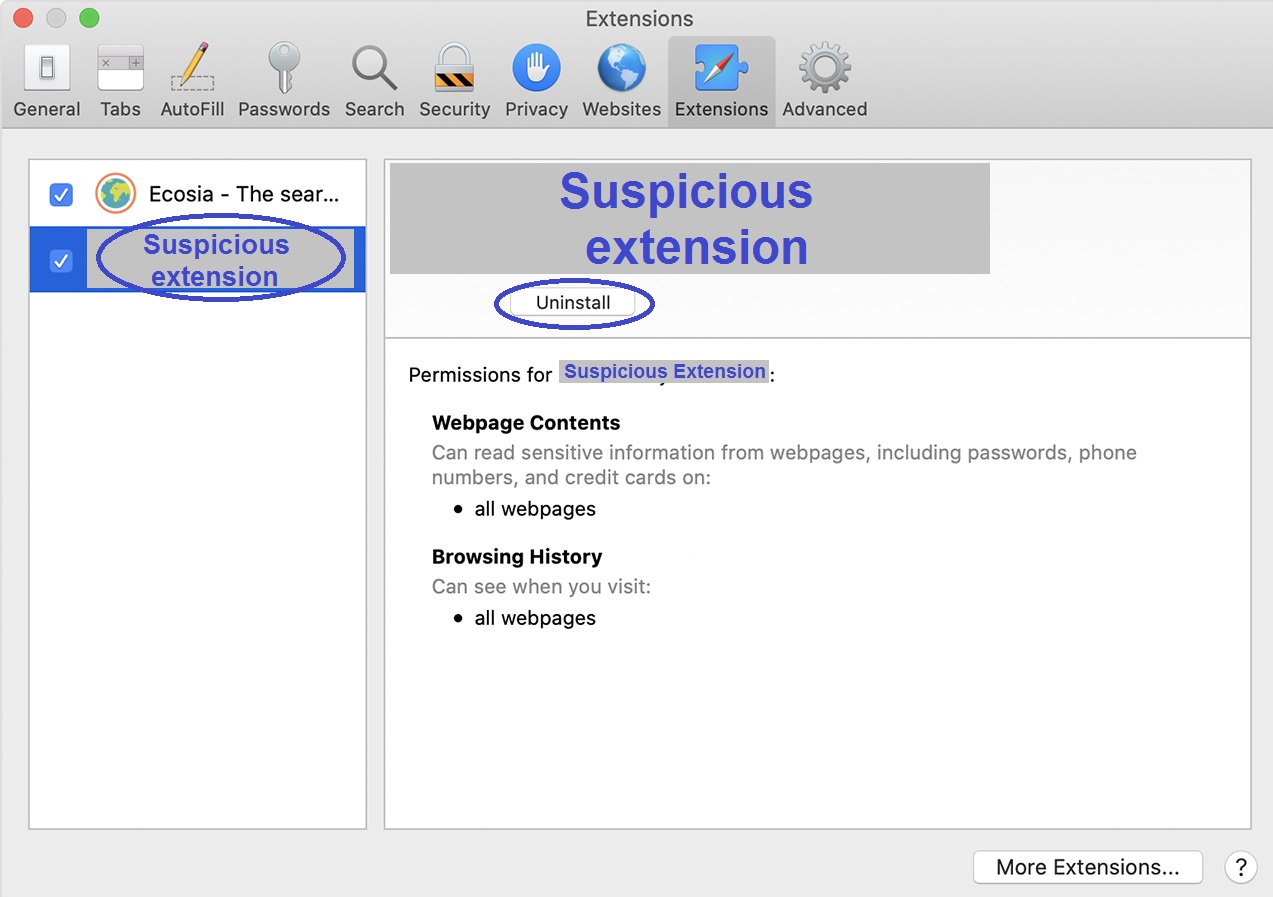
If ExtensionInstallForcelist has stopped bothering you while you are using Safari, then there may be no need to take any further action to clean the browser. Still, we strongly recommend that you complete the remaining instructions for Safari to make sure that there’s really nothing left related to ExtensionInstallForcelist inside the browser.
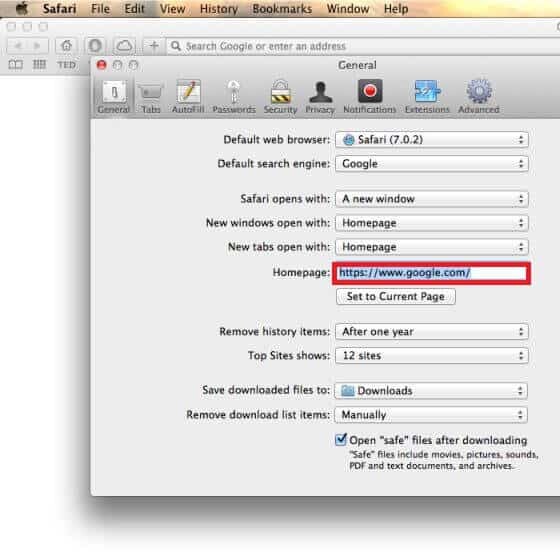
Start by clicking the General tab from Preferences and checking the browser’s homepage. If its address seems to have been tampered with/replaced by ExtensionInstallForcelist, then you must restore the previous starting page address (or replace the current one with a different address of your choosing).
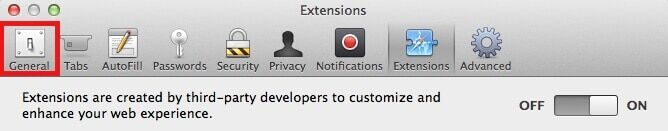
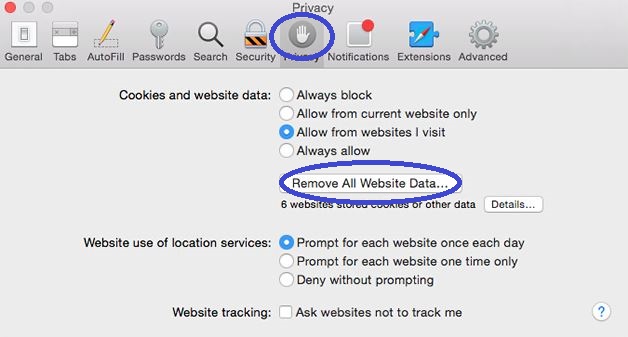
Next, click on Privacy from Preferences and then select Remove All Website Data. Confirm the action and wait for the browser data to be deleted – this will help ensure that there are no files left from the hijacker in your system.
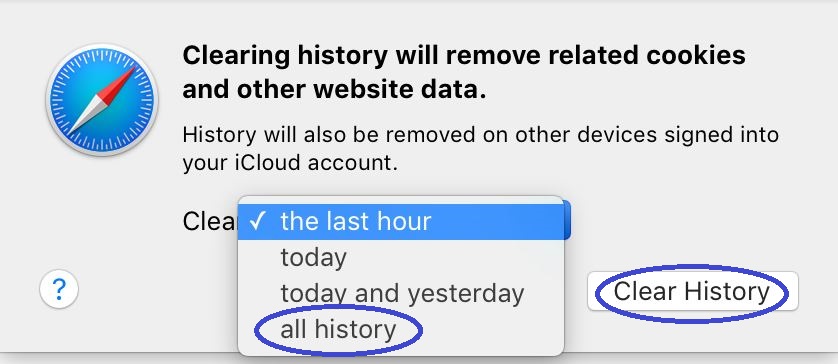
The last thing you must do in Safari is click the History menu, select Clear History, opt for the All History setting, launch the command, and wait for its completion.
If you have other browsers, check them too
Browser hijackers like ExtensionInstallForcelist are hardly ever limited to a single browser. Instead, they typically try to get integrated with all browser installed on the targeted device. Therefore, if you have other browsers in addition to Safari on your Mac, you should check them too for hijacker components and settings even if you don’t use those other browsers and/or if they don’t seem to display symptoms related to ExtensionInstallForcelist.
How to clean Firefox
Start the Firefox browser, click its menu from the top-right, and go to Add-ons. Disable and then uninstall any add-ons that you think are unwanted from the browser and hen select the Plug-ins section. There, check the different plug-in items and if any of them look suspicious, disable them.

To revoke any other changes that ExtensionInstallForcelist may have made in the browser, visit this guide on how to refresh the settings of Firefox and complete the instructions there.
How to clean Chrome
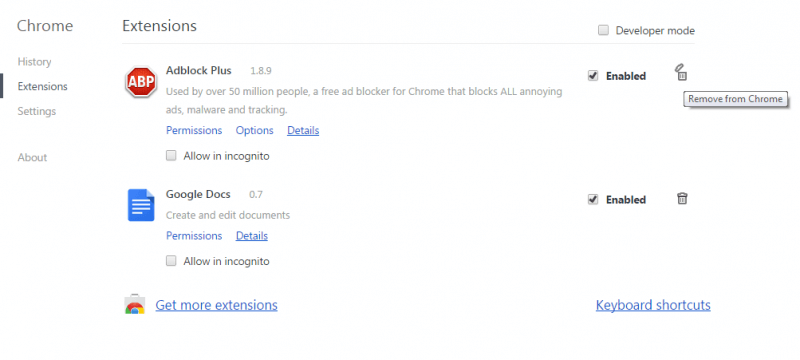
Just like with Firefox, open the Chrome browser, and select the menu from the top-right corner. Then go to More Tools and click the Extensions option from the sub-menu. In the extensions menu, find, disable, and delete any browser extensions that seem unwanted or that you don’t normally use.
Open the Chrome menu again, go to Settings > Search Engine (from the left) > Manage Search Engines and look for unfamiliar search engines listed there. If you find any, click the icon with three dots next to them and select the Remove from the list option to block those search engines.
Lastly, open this link and follow the Chrome instructions posted there to refresh the settings of the browser and make sure that no changes that ExtensionInstallForcelist may have made in the Chrome are allowed to stay.
What if ExtensionInstallForcelist didn’t get removed?
In case the instructions here didn’t help you fully remove ExtensionInstallForcelist, we recommend using a specialized removal tool to check your computer for unwanted data and delete it for you. It is possible that there’s a hidden malware in your system that is helping ExtensionInstallForcelist stay active, in which case using a professional anti-malware to help you take care of the problem is the suggested course of action. The removal software linked on this page is perfect for this task as it has been tested against both unwanted software like this hijacker as well as against highly-problematic threats including Trojans, Spyware, and Ransomware.

Leave a Comment