Hackers have created a phishing page, looking like the Facebook page
Security researchers have spotted a sophisticated Facebook phishing attack. They have come across new tricky methods, which hackers are using to collect Facebook users’ credentials. The malicious agents have created a phishing page, looking exactly like the Facebook page verification form. It is launched through the Facebook app platform and is cleverly masked as a legitimate one. The hackers designed an application that generates content (serving as a phishing page) from another website via an iframe.
The delusion for the users comes from the fact that this phishing application is loaded through the Facebook’s app platform. To look even more legitimate, the attackers have made the malicious page appear like hosted on the Facebook official domain. No warnings are displayed in the browser because the attack is covered up under the Facebook’s own TLS certificate and the external malicious website uses HTTPS. With all these fake credentials, it is hard for average users to detect the attack.
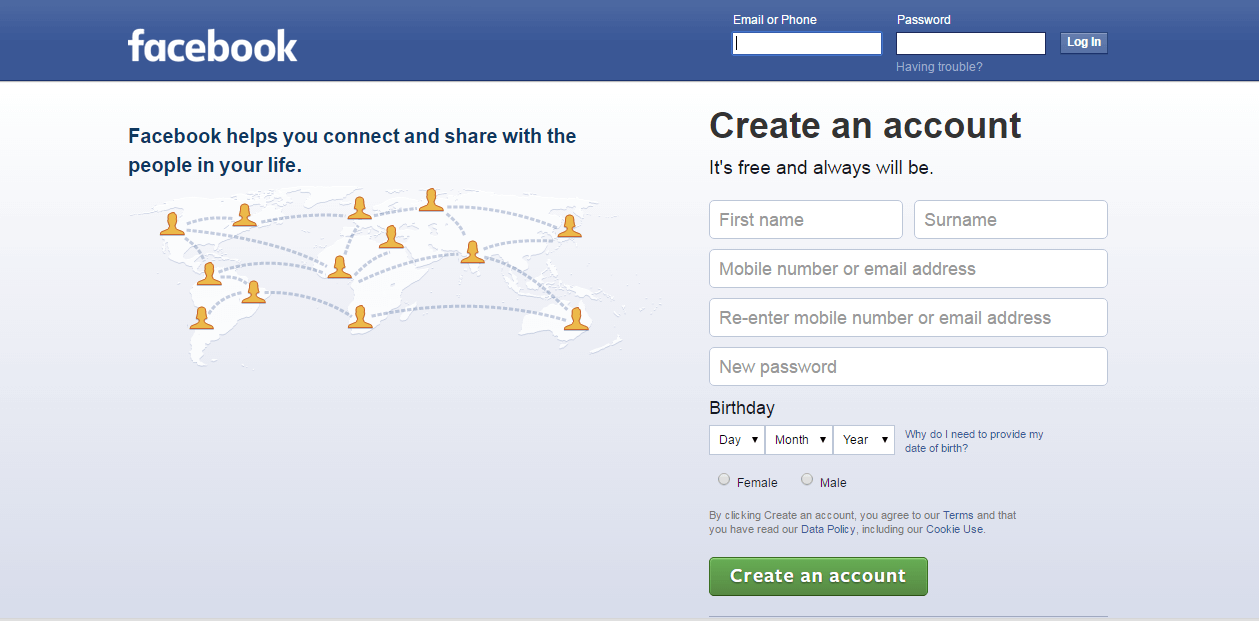
When users launch the fake Facebook page verification form, they are asked to fill in their password, email, mobile number and security question. Once they submit their credentials, the collected details are immediately sent to the attackers’ website. With this information at their hands, they can gain access to the users profile right away and use it for various malicious actions.
To make sure they are not raising any suspicion, the hackers use another clever trick. When the user submits his or hers details for the first time, an error message appears, stating that the username or password is incorrect. This is done to make users believe that the submitted credentials are really checked by Facebook. In case someone gets suspicious about the verification form, he may purposely fill in incorrect data in order to test the legitimacy of the form. The following incorrect message that appears would trick the user to believe in the scam.
After filling in the password, email, and verification details for the second time, the victim of the scam is notified to wait 24 hours for approval. During that time, the attackers can access the account, use it for scams and other malicious actions, or they can sell it to third parties.The abused Facebook account can also be used to trick the victim’s friends to the same phishing page.
To protect themselves from such attacks, users can use a two-step verification method to access their Facebook account. They should also enable the Facebook login alert notification that shows them when and where their account has been logged in from.
A piece of advice our “How to remove” team can give to the users is to always check the browser’s address bar. There should be an “HTTPS” string and a padlock icon that shows the website address. If they notice something different then the website they are thinking they are in, it most probably could be a scam or a phishing page. However, we should bear in mind that malicious actors are constantly improving their techniques in an effort to trick users to become their victims.

My Facebook page is under attack how can I get it back
Nice