FadBlock
If you have noticed that your computer is behaving strangely, then your system might have been infected by a Trojan horse called FadBlock. Many signs might hint towards a Trojan infection like this one. For instance, you might notice that your PC has become slow or unresponsive, or your internet connection might suddenly become shaky. You may also find new icons on your desktop, or your antivirus might keep popping up warnings about suspicious activity. Some other symptoms include unwanted pop-up ads, changes in your homepage or default search engine, or even weird emails sent from your account. Remember, Trojans like FadBlock are deceptive and often hide their tracks well, so these symptoms may not always be present.
Is FadBlock safe?
Fadblock’s safety is now uncertain due to potential malicious code introduced by successive owners. The original developer’s sale without disclosure raises concerns, highlighting the importance of transparency in software ownership changes. The situation underscores the risk of malware infiltration through seemingly benign applications. Users should exercise caution when using Fadblock and consider alternatives like Fadblock Origin, developed by the original creator. This cautionary tale serves as a reminder of the need for vigilance and skepticism, especially in the ever-evolving landscape of digital security threats.
What is FadBlock?
Wondering what exactly the FadBlock Trojan horse is? The term “Trojan horse” comes from the Greek myth of the Trojan War where the Greeks used a giant wooden horse, seemingly a peace offering, to infiltrate the city of Troy. In the cyber world, a Trojan horse or “Trojan” is a type of malicious software that misrepresents itself to appear harmless just like FadBlock. The user might think it’s a useful software, a video, or a link to something interesting. But once clicked or downloaded, it releases its destructive payload, leading to various unwanted effects.
Is FadBlock a Virus?
FadBlock is malicious software from the Trojan horse category, but it is not exactly the same as a virus. Although both are types of malware, they differ significantly in their operations. A computer virus can insert itself into a healthy program and replicate, infecting other programs. A Trojan like FadBlock, on the other hand, doesn’t replicate but deceives you into installing it, believing it to be useful or entertaining. In terms of distribution, both use various methods, including emails, downloads, or even websites. But a Trojan’s malicious activities often go beyond what a virus does – from stealing personal information, spying on the user, to creating backdoors for other malware.
FadBlock Virus
FadBlock may often be referred to as the FadBlock virus, especially by people who don’t understand the difference between the different types of malware. Regardless of how you call it, the kind of havoc the FadBlock virus can unleash is serious and the list is long and scary. A Trojan of this type can spy on you, steal sensitive data like passwords or financial information, corrupt files, or even use your computer as a part of a botnet to launch attacks on other systems. It can download more malware onto your system, manipulate your files, and even hijack your system’s operations. What is more, Trojans are often part of broader cyberattacks, acting as a gateway for other malicious software.
FadBlock Malware
Perhaps the most alarming thing about threats like the FadBlock malware and Kavaca is their stealthiness. They can infiltrate your system, operate undetected for years, and cause continuous damage. Trojans are crafty. They can disguise themselves as regular files or software and can even disable your antivirus or firewall without raising any suspicion. This stealthiness makes them one of the most formidable cyber threats today. They can be embedded in apps, pop up as ads, and even hide in executable (.exe) files. It’s a reminder to all of us to stay vigilant and use robust cybersecurity measures. After all, just like the mythological Trojan horse, threats like the FadBlock malware often come from where we least expect.
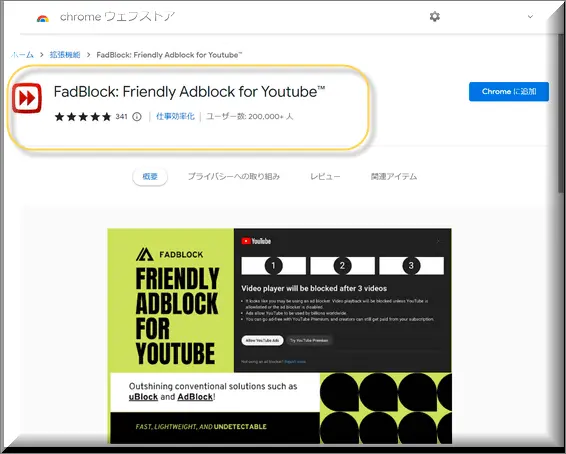
FadBlock on Chrome
FadBlock on Chrome is a Trojan Horse, a malicious entity often masquerading as a benign file. Once activated, its impact on a Windows computer can be multifaceted. Beyond the typical threats of data theft, such Trojans might also manipulate system settings, making the system more vulnerable to other infections. FadBlock on Windows can modify registry entries, deactivate vital security features, or introduce other harmful software. This Trojan can also slow system performance, display unsolicited ads, or reroute internet traffic, often directing users to phishing sites. The changes in system settings can make the removal challenging and might result in software malfunctions or data loss. Regular system scans with reputable security software can help counteract such threats.
SUMMARY:
| Name | FadBlock |
| Type | Trojan |
| Detection Tool |
FadBlock Removal
To try and remove FadBlock quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the FadBlock extension (as well as any other unfamiliar ones).
- Remove FadBlock by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of FadBlock and any other suspicious items.
If this does not work as described please follow our more detailed FadBlock removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the FadBlock app and kill its processes
Uninstall the FadBlock app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from FadBlock. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to FadBlock, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to FadBlock.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo FadBlock changes made to different system settings
Undo FadBlock changes made to different system settings
It’s possible that FadBlock has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for specific system elements that may have been affected, and pressing Enter to open them and see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window

 Remove FadBlock from your browsers
Remove FadBlock from your browsers
- Delete FadBlock from Chrome
- Delete FadBlock from Firefox
- Delete FadBlock from Edge
- Go to the Chrome menu > More tools > Extensions, and toggle off and Remove any unwanted extensions.
- Next, in the Chrome Menu, go to Settings > Privacy and security > Clear browsing data > Advanced. Tick everything except Passwords and click OK.
- Go to Privacy & Security > Site Settings > Notifications and delete any suspicious sites that are allowed to send you notifications. Do the same in Site Settings > Pop-ups and redirects.
- Go to Appearance and if there’s a suspicious URL in the Custom web address field, delete it.
- Firefox menu, go to Add-ons and themes > Extensions, toggle off any questionable extensions, click their three-dots menu, and click Remove.
- Open Settings from the Firefox menu, go to Privacy & Security > Clear Data, and click Clear.
- Scroll down to Permissions, click Settings on each permission, and delete from it any questionable sites.
- Go to the Home tab, see if there’s a suspicious URL in the Homepage and new windows field, and delete it.
- Open the browser menu, go to Extensions, click Manage Extensions, and Disable and Remove any rogue items.
- From the browser menu, click Settings > Privacy, searches, and services > Choose what to clear, check all boxes except Passwords, and click Clear now.
- Go to the Cookies and site permissions tab, check each type of permission for permitted rogue sites, and delete them.
- Open the Start, home, and new tabs section, and if there’s a rogue URL under Home button, delete it.

Leave a Comment