The Fake Amnesty International Antivirus
A fresh example of how hacking organizations are fast to capitalize on global events and adapt their attack operations to maximize their effect is the discovery of threat actors distributing malware pretending to be security software intended to protect against NSO Group’s Pegasus surveillanceware.
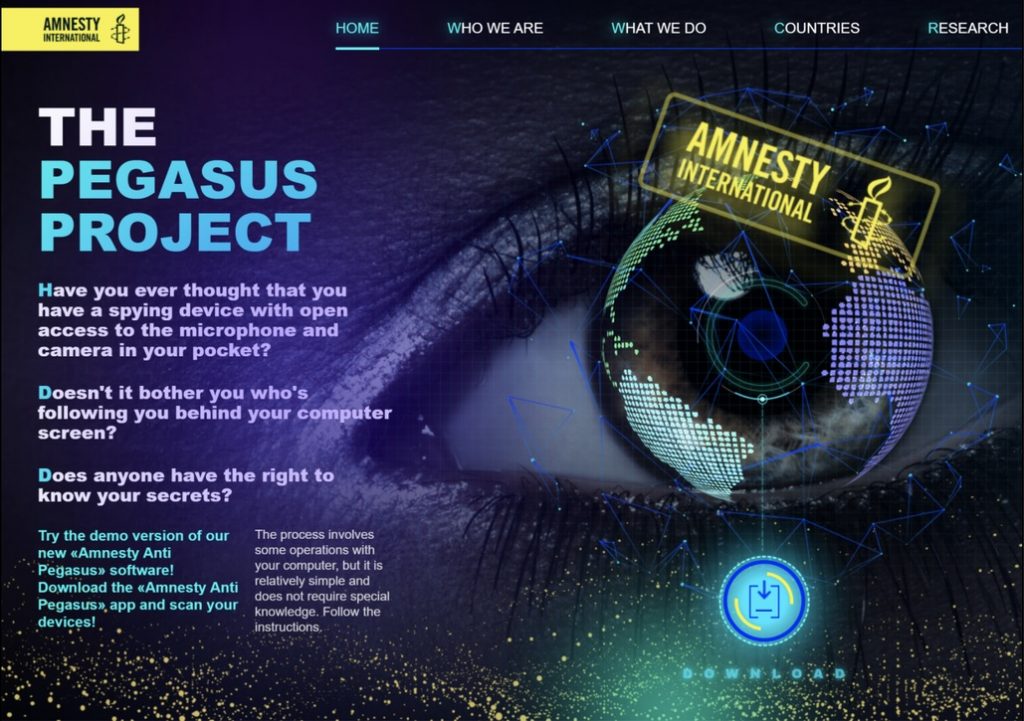
According to the information that Cisco Talos has revealed, threat actors have created a fake website that appears like Amnesty International’s — a non-governmental organization dedicated to human rights — and directs users to an antivirus program that is said to protect against the NSO Group’s Pegasus tool. The download, in reality, sets up the obscure Sarwent virus.
The United Kingdom, the United States, Russia, India, Ukraine, the Czech Republic, Romania, and Colombia are among the countries most hit by the bogus attack campaign. It is believed that the attacks may be targeted at people who are specifically looking for security against this the Pegasus danger. However, it is still unknown how the victims are tricked into accessing the phony Amnesty International website.
The news comes after a shocking research from July this year, that showed widespread usage of Israeli firm Pegasus “military-grade malware” for human rights abuses by spying on global leaders, activists, journalists, and attorneys. To assist people check their iPhones and Android devices for signs of compromise, the NGO has subsequently developed a Mobile Verification Toolkit (MVT).
While attempting to trick the visitor into downloading an “Amnesty Anti Pegasus Software” that looks and feels exactly like Amnesty International’s legitimate portal, the modus operandi also uses social engineering techniques to trick the visitor into providing sensitive information, such as login credentials, in exchange for the bad actor’s “Amnesty Anti Pegasus Software”.
Sarwent, a Delphi-coded malware version, has a high level of customization, and is capable of granting remote desktop access through VNC or RDP and executing command line or PowerShell instructions received from an attacker-controlled domain.
According to the analysis of Talos, the level of modifications made to the supposed antivirus are probable evidence that the malicious actor seems to has access to the source code of the Sarwent malware. It is interesting to note that Russian-speaking actors have been using the Sarwent backdoor more actively since January this year.
Researchers have shared that the attack is aimed mainly at individuals who are worried about being tracked by Pegasus malware. However, it is also likely this is just a publicity stunt by someone with a financial interest in seizing fresh opportunities.

Leave a Comment