Fargo2
Fargo2 is a file-encrypting program created for the purpose of blackmail. As you might suspect, this means that Fargo2 is a malicious piece of software that falls into the category of Ransomware.
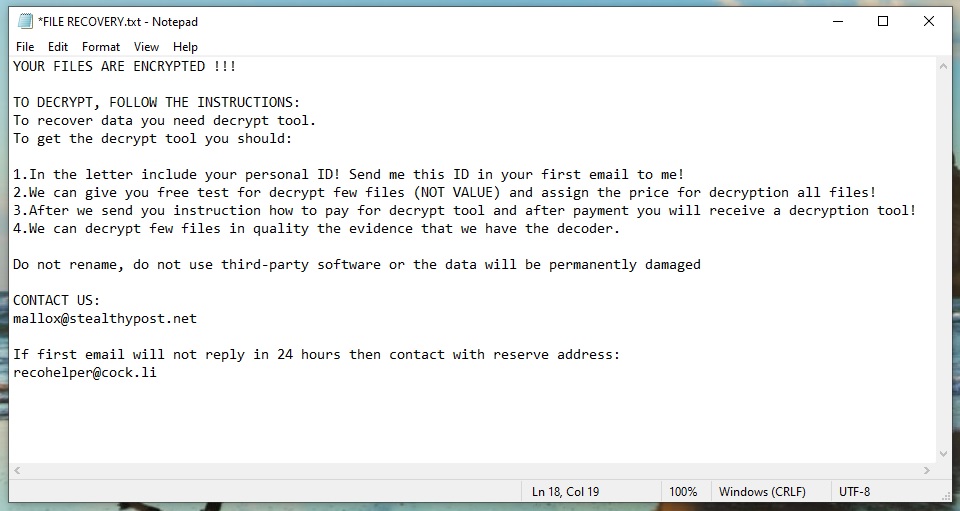
The Fargo2 ransomware will leave a FILE RECOVERY.txt file with instructions
If you have been infected with Fargo2, you may not be able to open, view or use your most frequently accessed files because they have been encrypted with complex code. Nonetheless, the following paragraphs will give you some ideas on how to proceed if you are a victim of this horrible virus. What is even more important, we will provide you with a self-help removal guide that can assist you in removing Fargo2 from your system and potentially recover some of the information that has been encrypted via system backups.
The Fargo2 virus
The Fargo2 virus is a piece of malware that seeks to encode user files and to restrict access to them until a ransom is paid. The Fargo2 virus can enter a computer in many ways but most commonly that happens with the assistance of a Trojan horse.
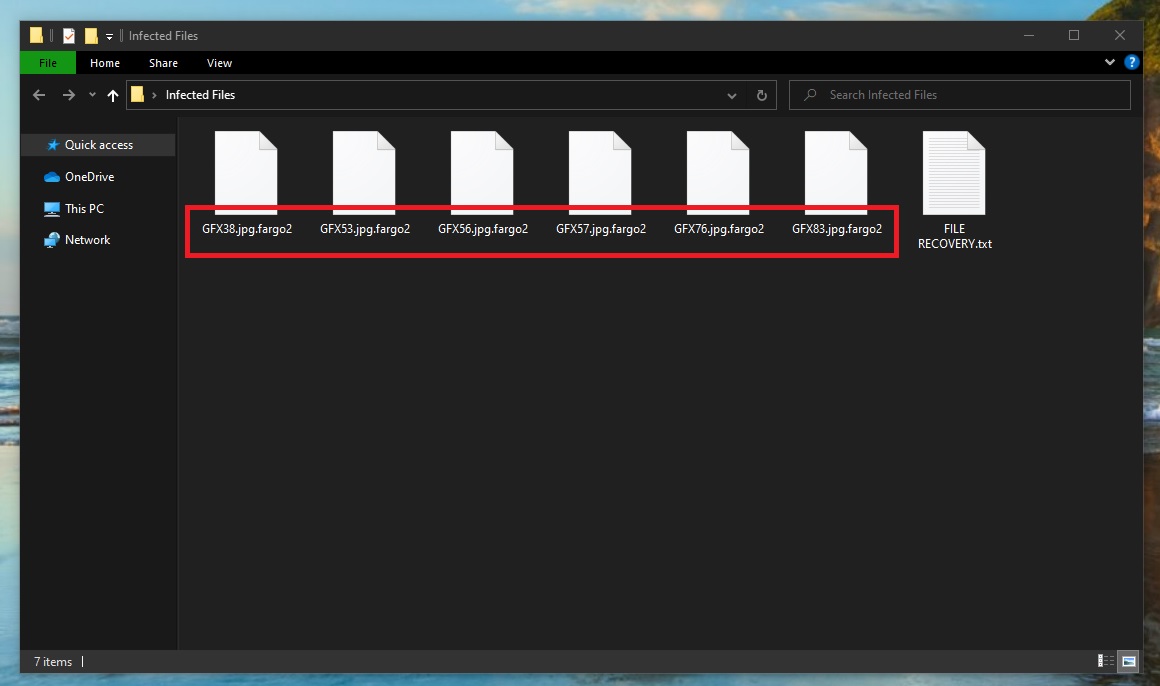
The Fargo2 virus will encrypt your files
The ransomware and its Trojan horse companion can often be embedded in e-mails and their attachments, and if you open such messages either by accident or out of curiosity, the Trojan will detect a vulnerability in your computer’s system and will let the Ransomware come in. Another way to get infected is by simply landing on contagious web pages. You may also get infected if a malicious online ad is loaded on your screen – clicking it will probably redirect you to an infected website where the malware can invade your computer automatically. Nevertheless, other potential sources such as torrents, pirated software installers and web pages for video sharing can also be used for ransomware distribution. The infection method is similar and as soon as you are exposed, you are instantly contaminated by this virus.
The Fargo2 file encryption
The Fargo2 file encryption is a harmful process that hackers use to block access to user data. The Fargo2 file encryption does not destroy the information it targets but simply converts it into unreadable bits of data.
Typically, ransomware such as Fargo2, Ooxa, Oori will render inaccessible some of your most needed and most frequently used files. You will be informed of that immediately after all the files are encoded. Usually, this will happen with a notification on your screen that shows you a list of the files that have been under attack and asks you to make a ransom payment to a given cryptocurrency account in order to decrypt them.
Sadly, it is not enough to pay the required ransom to solve the ransomware problem. In most cases, as soon as they get your money, the hackers can vanish and leave your data encrypted. That’s why if we were in your shoes, we would never pay unless we tried all other options at hand.
If you are ready to pay to remove Fargo2 anyway, you can always go and ask an expert for assistance. Another option is to use some self-help methods such as the removal guide below, a professional removal tool or some specialized software for ransomware recovery. If you have personal backups from where you can recover a major portion of your encrypted information, such methods could save you a lot of money and nerves and can help you remove Fargo2 and have a clean computer to which you can safely connect your backup sources.
SUMMARY:
| Name | Fargo2 |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Data Recovery Tool | Not Available |
| Detection Tool |
Remove Fargo2 Ransomware
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.
![]()
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!
![]()
How to Decrypt Fargo2 files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment