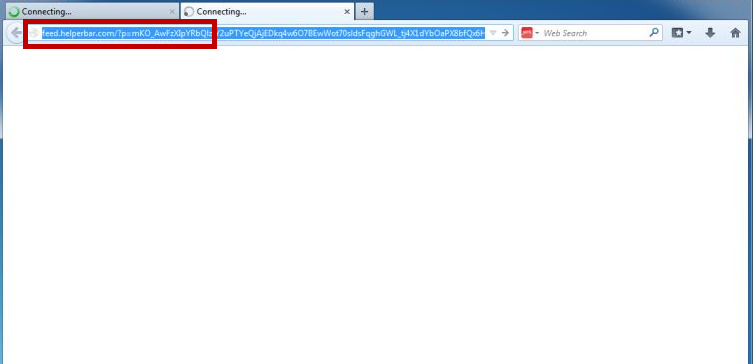
If you are faced with intrusive online ads, frequent redirects to promoted websites and if your browser has gotten altered in some way without you having given your permission for the changes, then you most probably have Feed.helperbar.com on your hands. Feed.helperbar.com will set the homepage and search engine for your web browser to http://search.snapdo.com/?q=.
Feed.helperbar.com Virus
Such applications are able to add a new search engine, homepage or new-tab page to your browser (Chrome, Opera, IE, Firefox or any other) as well as trigger the appearance of various types of ads, banners, box messages, new-tabs, etc. One recently released piece of software that has been reported to display such unpleasant and irritating behavior is Feed.helperbar.com “Virus” and on this page, you can learn everything you might need to know about it.
The Feed.helperbar.com Virus
Although browser hijackers (also known as page-redirects) like Feed.helperbar.com Virus are typically not regarded as dangerous and as harmful for the computer system or for the user’s virtual identity, such applications can still be very irritating and can at times indirectly expose one’s PC to certain risks. Because of this, it is advisable that anyone who has Feed.helperbar.com “Virus” or some other similar hijacker on their machine uninstalls it and fully removes it from the computer so that no further complications may arise from it.
In the lines below, we will show you how to handle hijackers and make sure that they do not get to your PC as well as remove Feed.helperbar.com “Virus” from your computer in case it has gotten installed on it.
As far as their functionality is concerned, as you have probably already guessed, browser hijacker applications are primarily advertising software tools that are utilized for conducting different marketing campaigns which, unfortunately, are usually rather aggressive and unpleasant to the end user. Any changes that a hijacker might try to make to your browser or to your Internet settings would have been introduced for the purpose of making the advertising more effective. For example, if a new search engine has replaced your browser’s default one, then it would be highly likely that if you use the new engine to search for something, the results displayed to you would be modified in a way that would push sites, pages or other content that the hijacker is supposed to promote.
Aside from that, as we already mentioned, you might directly get redirected to and displayed content such as banners, pop-ups, newly-opened browser tabs and browser windows that Feed.helperbar.com “Virus” is supposed to advertise. Naturally, this doesn’t really benefit the user in any way. Surely, sometimes an offer might come up that you might consider interesting but let’s be real – online advertisements are currently everywhere as it is and hardly anyone would need any more web-ads getting displayed on their screen when trying to use the browser. Some hijackers might also come with other functions that are supposedly useful and helpful but then again, you can likely get these same functions from some other, less irritating software that doesn’t try to constantly flood your screen with promoted content.
What we would advise you
If a Feed.helperbar.com “Virus” has gotten in your system, we recommend you get rid of it using the guide posted on this page. Such software is not only highly irritating but it could also trigger certain risks for your computer. The main problem regarding that is the variety of ads and page redirects that get generated by the hijacker. Most of them should be safe and some you might even find interesting. However, there’s always the chance that a number of the ads might actually link to shady and hazardous locations – ones that might be used by hackers to spread malicious viruses like Trojans, Spyware, Rootkits, Worms, Ransomware, etc. Of course, in itself, Feed.helperbar.com “Virus” is no Trojan, Ransomware or any other type of virus but the fact that not all of its advertising contents can be verified as safe should be enough to remind you to avoid anything generated by it.
Another important thing to be mentioned here is that you need to be careful from now on so that you don’t get any more hijackers installed on your PC. To avoid future encounters with such irritating and unwanted applications, always make sure that you explore the setup installers of software that you want to install on your PC – check if there are any bundled applications to the main program by accessing the Custom/Advanced setup menu and if you indeed find something there that doesn’t look trusted, opt-out of its installation before you proceed. Also, be sure to avoid suspicious online content such as spam messages and questionable web ads and also remember to keep away from illegal sites or sites with low reputation.
SUMMARY:
| Name | Feed.helperbar.com |
| Type | Browser Hijacker |
| Detection Tool |
How To Remove Feed.helperbar.com from Browser
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone.

Also, seach for Quoteexs in registry and delete all records. Keep URL, which is supplied by this adware and search in registry & replace by some you want…