This page aims to help you remove Ffshrine. Our removal instructions work for every version of Windows.
Ffshrine
Ffshrine is a Trojan Horse that enables cybercriminals to see everything you do on your computer and cllect sensitive information. Ffshrine does this by allowing remote access to your computer to the offenders.
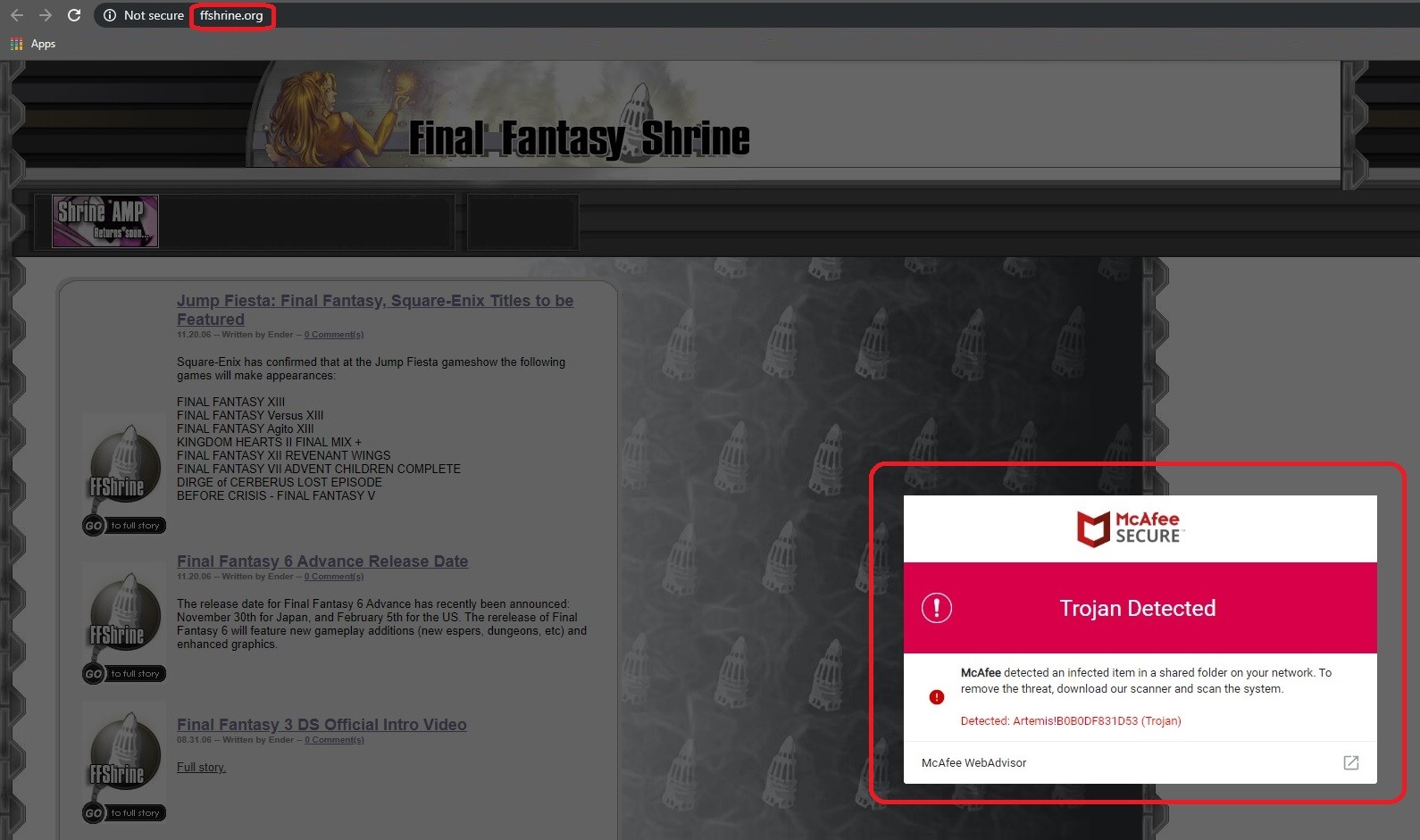
The ffshrine.org is a legitimate website that has suffered a malware attack. Upon loading the ffshrine.org page a message will pop up up claiming your computer has been infected, it will also offer a downloadable file which will install malicious software if you run it.
This article you’re about to read has been created to help you fight Ffshrine. This virus falls under the Trojan Horse category and, in the next lines, you will learn how to remove it and how to protect your system from it. The Trojan Horse viruses are widely known as some of the most common and most malicious threats that can be found online.
A Trojan such as Ffshrine can generally be used for many insidious purposes. We’re going to point out only the most common ones with the idea to help you understand what you can expect from such an infection inside your machine. We are also going to provide you with a detailed removal guide and a trusted automatic removal tool for a full system scan.
The Trojan’s specifics
Typically, most Trojans can operate in a very stealthy manner – they can infect your system and you may not even notice it. This may explain why the representatives of this malicious group have been named after the ancient wooden Trojan horse from the Trojan War myth. A virus such as Ffshrine can infiltrate your system without showing any symptoms and, once nested inside, it can patiently and silently wait for the perfect time to fulfill its malicious task.
Sadly, there can be dozens of harmful activities that can be conducted in your PC with the help of this malware. Starting from file corruption and software destruction, to theft of sensitive information and even insertion of other viruses such as Ransomware. A Trojan can also destroy specific data, delete your hard drive’s contents, or modify important system records. As a consequence, your computer may not be able to perform any tasks. The Trojans are also a tool used to distribute other viruses. Such threats can infiltrate your device and secretly sneak a Spyware or a Ransomware program into your system, and that, without any visible symptoms. This is certainly one of the worst scenarios.
Another goal of the cyber criminals behind Ffshrine may be to exploit the resources of your system – they may want to turn your computer into a bot and use it to spread spam or mine cryptocurrencies. This is also a very unpleasant scenario because, as you, being the owner of the hijacked computer, may be accused of online crimes that you have never actually committed.
Another common use of many Trojans is surveillance – the hackers behind the malware may be interested in some sensitive information related to your workplace or your personal life. And with the help of the Trojan, they may gain access to it either by keeping track of your keystrokes, or by hacking directly into your webcam or microphone.
After all that we said above, it is clear why you have to remove Ffshrine immediately. As far as prevention is concerned, we advise you to install a good anti-malware program and to try to avoid spam emails, fake online adverts, random links, torrents, or illegal web platforms which are known to spread pirated software, as these may frequently be used to distribute Trojans.
SUMMARY:
Remove Ffshrine Trojan
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Reply