*Source of claim SH can remove it.
Floxif
Has your system been infected with a Trojan horse named Floxif malware virus? If you are not really sure what this threat may cause and how to deal with it, then you have landed on the right place. In this article, we are going to disclose all the specifics of this malware as well as Trojan horses in general and will give you some specific instructions on how to remove Floxif virus from your computer.
Being infected with a Trojan horse is not a nice thing and your privacy and your PC might be put in great danger, so the sooner you eliminate all the harmful scripts, the better. The removal guide below contains all the details, but before you scroll down, let us first give you an idea of the nature of Trojans and their dreadful and destructive abilities.
The Floxif Virus
The chance of catching the Floxif Virus while you are browsing the web is greater than catching any other type of malware. This is so because the Floxif virus is considered some of the most widespread and tricky malicious infection.
Their criminal creators prefer them more than the normal viruses because they can easily be masked as something very harmless-looking and can easily trick unsuspecting online users. This ability to camouflage gives them the chance to infect the computers without the victim’s consent and secretly perform the criminal deeds they have been programmed for. What is more, Trojans usually lack visible symptoms and for this reason, they may remain on the machine for long periods of time before they get detected. If the antivirus fails to recognize them, such threats can stay on the PC for months or even years before the victim realizes their presence. In fact, in most of the cases, the users come to know about the infection only after serious damage is done.
What damage may Floxif malware cause?
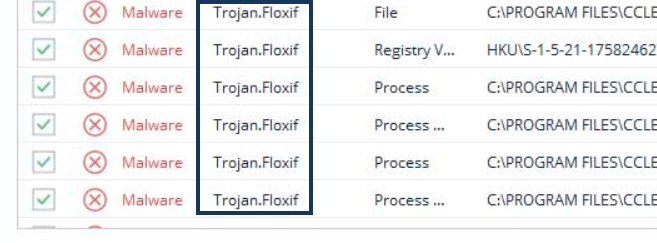
Floxif malware is a new Trojan virus that has recently been detected. As per the latest reports, this threat has the capacity of performing a wide range of criminal tasks. The hackers, who control it, may use it for obtaining some personal information or credentials from your computer. With its help, they may steal your passwords and login credentials, banking details or credit card numbers. Your working files, contacts and correspondence may also be compromised, so basically, all of your data may easily be transmitted to the criminals and can be used for a number of malicious deeds. In some cases, the information on your computer may be completely destroyed or encrypted with the help of a Ransomware virus, which the Trojan may have the task to insert in the system. The crooks may also spy on you or use the machine as a bot and get you involved in spam and malware spreading without your consent. With all this in mind, we believe you don’t need more reasons to remove Floxif virus from your system as soon as possible and eliminate all of its traces. The guide below can be very helpful if you are dealing with such a treat for the first time, so we highly recommend you use it. Alternatively, if you are not confident that you can detect the correct malware manually, you can scan the computer with the professional Floxif virus removal tool. This software can automatically detect the Trojan and remove it along with all the related malicious scripts.
How to protect your PC from Trojans
Once you remove Floxif malware, don’t think that the battle is over. It is of no less importance to protect your system against future infections of this type. For this reason, you should first ensure that your PC has all the needed system updates and security patches as well as reliable antivirus software that can detect new threats like Floxif malware. Of course, this may not guarantee you a 100% of protection, so we advise you to use a few safety tips, especially when you surf the web. Trojans and other malicious threats may be found almost anywhere on the web but you should use your common sense to avoid them as much as possible. Some of the main sources from where you might get infected include malicious emails and attachments as well as fake ads and malvertisements. Our advice for you is not to click on every new pop-up, new tab, link or attractive looking email and keep away from attachments that come from an unknown sender. Stick to safe and trusted web locations, carefully choose your software sources and do not open spam messages, emails or other sketchy content. This may greatly reduce the chance of bumping into a well-hidden infection and may really save you from unpleasant Trojan horse encounter.
SUMMARY:
| Name | Floxif |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Detection Tool |
*Source of claim SH can remove it.
How to Remove the Floxif Virus
In some cases, it is possible that you may be able to remove a Trojan such as the Floxif Virus if you delete (uninstall) the app responsible for getting your computer infected. This is why, we will start with this as the first removal method for this malware. It is the fastest and easiest thing you could try to remove Floxif Virus and if it works out for you, there won’t be any need to go to the more advanced steps.
- You can uninstall any program or app from your computer through the Control Panel so go to it by typing Control Panel in the search box that appears when you open the Start Menu and select the first icon from the search result items.
- When in the Control Panel of your PC, look for the Uninstall a Program button and click on it – this will bring to your screen a list with all the programs and applications that you have been installed on your machine.
- Look at the items in the Uninstall a Program list carefully – you should be looking for a suspicious app/program, especially if it is one that you can’t recall installing or that you remember installing around the time your machine got infected by the Trojan. If you think you can single out such an item, select it and use the Uninstall button at the top of the window to initiate the uninstallation of the suspicious piece of software.
Note: You will probably not see the name of the Floxif Virus and that’s okay – most Trojans try to hide themselves by changing their names to appear harmless so don’t get discouraged if you don’t see the name of the virus in the Uninstall a Program list. - In some cases, the uninstallation would start immediately, in other cases, you’d have to follow the steps from an uninstallation wizard but in most cases you should be able to uninstall the selected software. In some cases, however, you may see the following dialog box pop-up on your screen while you try to uninstall the suspicious app:
 If this shows up, click the NO option or else another unwanted and/or malicious app or program may get installed on the computer.
If this shows up, click the NO option or else another unwanted and/or malicious app or program may get installed on the computer. - If there are more than one suspicious programs you think could be potentially be linked to the virus, uninstall all of them.
- If after completing the uninstallation of all suspicious software the problem with the Floxif Virus persists or if the virus doesn’t allowed you to uninstall the app that contains it, move on to the steps you will find below.

Regardless of the software issue you are faced with and trying to solve, it is almost always better do do it with Safe Mode enabled. When in Safe mode, only the essential processes are left running on the computer so anything that could be linked to the problem (in this case the Trojan virus) would be prevented from running and it won’t interfere with your attempts to remove it. for those of you who are not sure how to enter Safe Mode, click on the link to go to a guide where there’s a detailed explanation on this topic.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Now that you have Safe Mode enabled on your PC, it is time to get down to removing the Trojan from the machine. The first thing you ought to do is press the Ctrl, Shift, and Esc keys together to open the Task Manager and then go to its Processes section. Now you must once again look for anything suspicious that may catch your eye – processes that take up too much RAM memory or CPU and/or ones that don’t seem to be linked to any of the programs and apps that are currently open. Again, the name Floxif Virus may not be seen there but this doesn’t mean that the Trojan Horse process isn’t listed under a different name so look carefully.
Important: Some of the listed processes are essential to the normal functioning of the computer so be sure to always google the name of a given process before you try to stop it and/or delete any files related to it to be sure that it isn’t something important to the system.

If you think you’ve found a process that may have something to do with the virus, right-click on its name and select the Open File Location option and then, in the folder that opens, check each file for malicious code by dragging it to the our free online malware scanner that you can see below.

If the scan tells you any of the files could be malicious, go back to the suspicious file in the Task Manager and kill it (right-click on the process and select End Process). Then return to the file location of the process and delete the whole folder in which the malware files are located.
In some rare cases it is possible that the scanner doesn’t detect a malicious file but if you are certain that a given process and its corresponding files are linked to the Trojan, delete them even if no malware code was detected during the scan.

For the next step, go back to the Start Menu , type system configuration in it, and hit Enter. In the System Configuration window, go to the Startup tab and uncheck all items from the list that look like they may be connected to the virus. Commonly, a startup item related to a malware program would have an Unknown developer so be on the lookout for that.

Once you uncheck the items you deem questionable and unwanted, click on Ok/Apply + Ok to save the changes.

Next, you must check your PC’s Hosts file to see if it has been hacked – most forms of malware make changes to said file to make their removal more difficult. Copy-paste this line: notepad %windir%/system32/Drivers/etc/hosts in the search field of the Start Menu and hit the Enter key – this will open the Hosts file and you must take a look at what’s written under LocalHost. Normally, there should be nothing written below it. If you see strange IP addresses in there, copy them and paste them in the comments so that we can see them end tell you if they must be deleted from the file. Not all IPs in the Hosts file under Localhost come from malware – sometimes regular and legitimate programs may add such IPs as well.

If we tell you that the IPs you’ve send us are likely to be related to the Trojan, go back to the Hosts file, delete them from it, and then save the changes to the file by pressing Ctrl + S on your keyboard.

To complete this step, you will need to make changes in the Registry Editor of your PC. There are lots of important and sensitive settings in the computer’s Registry and if changes are made to the wrong items there, this could destabilize the whole system and lead to all sorts of unforeseen consequences. Therefore, you must proceed with caution and only delete something if you are certain it belongs to the malware and isn’t related to an important system function. In case you are not certain about whether to delete something in the Registry Editor, it’s best to first ask us in the comments for confirmation.
To clean the computer Registry from Trojan Horse data/settings, first go to the Start Menu, type regedit in it, and press Enter. If asked to allow the app to make changes in the system, confirm that by selecting Yes.
When the Editor opens, select the Edit menu at the top and copy-paste the name of the virus in the small search field. Hit Enter to search for items in the Registry that have the same name and if anything gets found, right-click on the item and select the Delete option. Rinse and repeat the search and deletion until nothing that carries the name of the malware remains.
Regardless of whether you found any entries named Floxif/ Floxif Virus, next go to these locations in the Editor and look for folders with odd names such as long sequences of seemingly random characters that stand out from the other folders. Anything like that you find in these next locations, you should delete. Again, if you are not certain about whether a given folder must be deleted, it is best to first ask us about it before you proceed with deleting it.
- HKEY_CURRENT_USER > Software > *Folder with suspicious name*
- HKEY_CURRENT_USER > Software > Microsoft > Windows > CurrentVersion > Run > *Folder with suspicious name*
- HKEY_CURRENT_USER > Software > Microsoft > Internet Explorer > Main > *Folder with suspicious name*

i dont have any IP’s without “#’s” , so am i safe now???
Hi mech,
can you copy and paste the content of the Hosts file ?
# Copyright (c) 1993-2009 Microsoft Corp.
#
# This is a sample HOSTS file used by Microsoft TCP/IP for Windows.
#
# This file contains the mappings of IP addresses to host names. Each
# entry should be kept on an individual line. The IP address should
# be placed in the first column followed by the corresponding host name.
# The IP address and the host name should be separated by at least one
# space.
#
# Additionally, comments (such as these) may be inserted on individual
# lines or following the machine name denoted by a ‘#’ symbol.
#
# For example:
#
# 102.54.94.97 rhino.acme.com # source server
# 38.25.63.10 x.acme.com # x client host
# localhost name resolution is handled within DNS itself.
# 127.0.0.1 localhost
# ::1 localhost
Mam wirusa jakiegokolwiek?
hi mechanik,
you can safely remove these.