*Foza is a variant of Stop/DJVU. Source of claim SH can remove it.
Foza
Foza is a very dangerous piece of computer malware that can make any file on your computer inaccessible. The method Foza uses to lock up the data of its victims is an advanced file encryption process that no conventional software can revert.
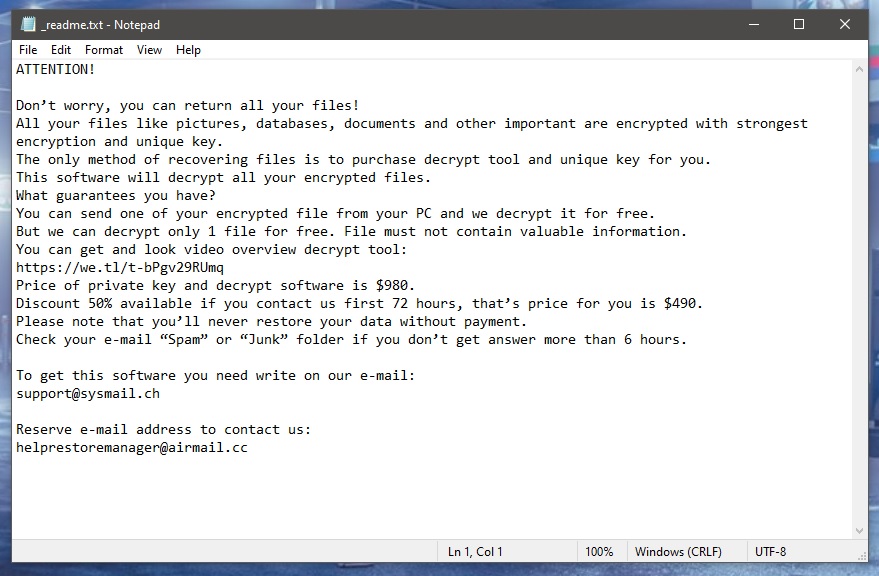
Once the Foza virus enters the computer of its victims, it starts searching for data that belongs to certain preset file formats – typically, ones that users use frequently in their daily life. Some examples are different text document formats, spreadsheets, various types of image files, audio and video files, and so on. The goal is to lock those files using encryption and keep them unavailable until the victim sends a set amount of money to the people controlling the virus. According to a note that the virus shows the user once the encryption process is over, once the victim pays the hackers the demanded ransom amount, they will immediately be sent a matching access key, capable of releasing the sealed data.
Many users either don’t value the files that have been locked enough to release the payment or simply can’t afford to spend so much money for the ransom payment at the moment and so they don’t complete the payment. Some, however, do opt for this variant as soon as they see the ransom message and this is a course of action that we strongly advise against. The issue is that you may still not receive a working decryption solution even after completing the payment. There isn’t a guarantee that the blackmailers would do exactly what they have promised and so trusting them is inadvisable and can cost you a lot of money wasted for absolutely nothing.
The Foza virus
The Foza virus is an extortionist virus used for the purpose of blackmailing its victims for payment by restricting access to their own files. The Foza virus locks the files through means of data encryption that is applied without any visible symptoms.
Most antivirus and antimalware programs, even the most popular and strong ones, are typically ill-equipped to detect Ransomware during the time of the ongoing encryption process. Even security tools with specialized anti-ransomware features don’t always manage to spot the encryption process on time. To make matters even worse, there are also almost no visible symptoms that can tip you off to the virus’ presence. This makes it quite difficult to spot and intercept such threats like Coza, Coty, which is why prevention is the single best way of dealing with Ransomware.
The Foza file decryption
The Foza file decryption is the software process that is supposed to restore access to files locked by this malware. The Foza file decryption is usually not possible if you don’t have the key that matches its algorithm on your computer.

Getting that key is, as we already pointed out above, not guaranteed even if you pay the ransom in full. However, there are several suggestions we have for you that might allow you to recover some data through alternative means. Those suggestions you can find after the removal instructions for Foza. We strongly advise you to first complete the removal part of the guide so as to prevent further encryption of more data on your computer in the future.
SUMMARY:
| Name | Foza |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Data Recovery Tool | Not Available |
| Detection Tool |
*Foza is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Foza Ransomware

If you want to remove ransomware from your computer, you need to take every step in this guide to ensure that you succeed. First, we recommend that you unplug any external storage devices and USB drives that are attached to the infected computer. After that, ensure that the ransomware can’t interact with the malicious servers by disconnecting your computer from the Internet.
Bookmarking this removal in your browser is also a smart idea because your computer will need to be rebooted, so you may simply go back to where you left off by clicking on the bookmark. As an alternative, you can open this Foza removal guide on another device and follow the steps from there.
And speaking about a computer restart, we recommend that you restart your computer in Safe Mode to ensure that the removal procedure is completed in the most efficient way possible. You may do a Safe Mode restart by clicking on this link and then following the on-screen directions. Return to this page and go to the next step when the computer has been rebooted.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Foza is a variant of Stop/DJVU. Source of claim SH can remove it.
In the second step, open the Task Manager on the infected machine (press Ctrl+Shift+ESC simultaneously) and go to the Processes tab. Take a look at the list of all currently active processes, and then sort them by the amount of memory or CPU they use. If you notice a process that appears to use way more resources than normal, or has a strange name, right-click on it and select Open File Location, just as shown on the image:

To see whether this folder contains any harmful files, just drag its contents to the scanner on the right:

It’s important that you first end the process that’s presently running (Right-click on the process>>>End Process) in order to remove any hazardous files from the folder. After that, return to the file location folder and remove any files that are flagged as dangerous to your computer.

Afterwards, press the Win key and R key at the same time, and then type the following command in the Run box that appears:
notepad %windir%/system32/Drivers/etc/hosts
Notepad should open a Hosts file on the screen when you press Enter. Make a note of any IP addresses that appear in the text under “Localhost” that seem to be untrustworthy. Report any questionable IPs in the comments section below. We’ll check into them and get back to you if we find anything troubling.

Files related to Foza may also be found in the System Configuration window, so this is the next place to look in. Using the Start menu, type “msconfig” in the Windows Search field, and then press Enter. Then, take a look at the startup items that are checked in the “startup” tab.
Disable any startup items you suspect are linked to the virus by removing their checkbox. Finally, you may close the window by pressing the OK button. If you’re uncertain about anything, you should better look it up online and only then decide what to do.


*Foza is a variant of Stop/DJVU. Source of claim SH can remove it.
The registry is a common location for malicious software to hide its components, allowing it to stay on a computer for a long time. When a system is rebooted, the virus may be prevented from being entirely erased and then reinstalled using the files from the registry. That’s why, if there are files that are linked to Foza, you must find and remove them from the registry using the Registry Editor. To access it, type regedit in the Windows search bar and then click Enter.
In the Registry Editor, you may look for files that are linked to the infection by pressing the CTRL and F keys on your keyboard together and opening a Find box. Once you’ve entered the threat’s name into the Find box, choose Find Next and start the search.
Attention! Ransomware files in the registry might be difficult to remove, especially for those unfamiliar with malware cleanup. At the same time, the system’s overall performance and stability may be affected if any registry entries are incorrectly deleted. For this reason, non-technical users who suspect their machine is infected with Foza and want to remove it should turn to a malware removal tool. Antivirus software like the one on this page may also be used to protect the machine against future malware attacks.
You should also manually scan the following locations on your computer for more ransomware files, since it is possible that they may hide there. To do that, type the name of each one in the Windows Search bar and then press Enter.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
It is necessary to thoroughly check the directories above, but you should not remove any files unless you are convinced that doing so will eliminate the threat. When you open the Temp folder, select all the files, and then press the delete key on your keyboard to erase all the temporary files on your computer.

How to Decrypt Foza files
Even for experts, decrypting ransomware-encrypted data is not an easy task, and there may be situations that make it more difficult to handle. Ransomware’s decryption techniques might differ from version to version, which is one of the reasons why inexperienced users may have a hard time to deal with such a threat. For this reason, it’s critical to figure out which variant of ransomware you’re dealing with specifically. To determine what kind of ransomware has infected your system, look at the file extensions that have been attached to the encrypted data.
Antivirus software like the one available on our site should be used before any data recovery can take place, because if the ransomware is still on the system, it may quickly encrypt everything that you may potentially recover. That’s why recovering data should not begin until the system has been thoroughly inspected for malicious software, best with the help of a professional antimalware software.
New Djvu Ransomware
STOP Djvu is a variant of ransomware, that encrypts a broad range of data types and then demands money from its victims in order to provide them with a decryption key. Typically, it is possible to identify the exact ransomware type by looking for the suffix .Foza, which is often tacked to the end of the encrypted files. Once you’ve figured this out and made sure your machine is virus-free, you may want to try using a decryptor, like the one linked below, to see if you can get your data back that way.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Don’t proceed with decryption until you have read the license agreement and any other instructions that come with the STOPDjvu executable file you downloaded from the URL above. Keep in mind that this program’s ability to decrypt your data is not guaranteed, especially if the files were encrypted using an unknown offline key or online encryption mechanism.
If the manual methods mentioned in this article fail to eradicate Foza efficiently, you will need to use a powerful anti-virus application. You may do a manual virus check on any file you’re concerned about using our free online virus scanner. If you have any questions about any of the steps in this guide, please leave a comment, and we’ll get back to you as soon as possible.

Leave a Comment