Frameboxxindore.com
Frameboxxindore.com is one of the latest browser hijacker representatives to be reported by users. Frameboxxindore.com is known to infiltrate popular web browsing applications and take over some of their main settings.
Typically, when a computer is attacked by some form of malware like a Trojan horse, a rootkit or ransomware virus, the invading malicious program usually doesn’t initially give away its presence in any way. Instead, it tries to stay hidden for as long as possible until its nefarious task is finally complete. The same cannot be said about browser hijackers like Frameboxxindore.com or Gooddaywith-captcha.top which is one of the reasons why, although apps like this one may seem harmful, they aren’t really regarded as highly dangerous software.
A browser hijacker app is more of an annoying browser add-on for Chrome, Firefox and other browsers than a malicious and harmful malware infection. Once it latches onto the user’s browser, it set a new search engine as default and also change the homepage and new-tab page address in order to spam ads, page redirects, banners and pop-ups inside the browser more easily and effectively. This, in fact, is the main purpose of apps like Frameboxxindore.com : to swarm users’ screens with nagging advertisements as a means of making money for the people who have created them.
In many instances, an application of this type may be presented to you as something that you are told you would find useful. For example, a helpful add-on for your browser that can help you make your browsing time safer or better optimized. The problem is that if you are indeed dealing with a hijacker like Frameboxxindore.com , there would hardly be any actual usefulness. Instead, all you will probably get from such software is the irritation from its unwelcome browser changes and obstructive ads. The good news, though, is that handling this situation and cleaning your browser isn’t really all that difficult. Still, there are certain things that need to be done before you can be certain that the hijacker is uninstalled and you can learn more about that from the removal guide below.
It’s important to quickly remove Frameboxxindore.com once you find it inside your system because otherwise the ads will keep on swarming your screen and obstructing your online activities. In addition to that, we must also tell you that you are advised against clicking on any of the randomly displayed pop-ups, banners, blinking messages and other advertisements that you may see from Frameboxxindore.com .
First of all, not all of them may be what they seem. As you likely know, oftentimes, the adverts that you may see online may actually be linked to sites and offers different from what seems to be advertised. This could also apply to the ads that the hijacker delivers on your screen.
And since you can never be sure what the real origins of a given ad are, you should always keep in mind that there is a certain chance that some online adverts could even redirect you to malicious and illegal online locations. And this can, in turn, lead to all sorts of problems like getting your computer invaded by ransomware, worms, Trojans and other viruses. Therefore, keeping a safe distance from the commercial messages and removing Frameboxxindore.com as soon as possible is what we would advise you to do.
SUMMARY:
| Name | Frameboxxindore.com |
| Type | Browser Hijacker |
| Detection Tool | Some threats reinstall themselves if you don't delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don't harm your system by deleting the wrong files. |
Remove Frameboxxindore.com Malware
In the event that you don’t want to go through this entire guide, here are some quick instructions that you may want to try to remove Frameboxxindore.com from your system:
Navigate to the the hijacked browser’s main menu by clicking the menu button in upper-right corner.
In the drop-down menu, select More Tools/Add-ons.
To access browser extensions, click the Extensions tab or the Extensions sub-menu. You can remove any ad-generating extensions by clicking the “remove” button found next to each one of them.
You can start a new browsing session to see if the extensions you removed from your browser had any effect.
If the problem with Frameboxxindore.com has been resolved, nothing else needs to be done. To remove hijacker-induced browser changes from your computer, however, you may need to follow the detailed instructions provided below.

We strongly recommend that you bookmark this page for future reference because if you do so, you’ll be able to quickly find your way back to this guide when you restart your computer. If you prefer, you can open the instructions on a different device and follow them from there.
To remove the browser hijacker, you must first restart your computer in Safe Mode. When only the most essential programs and processes are running in Safe Mode, it is much easier to spot suspicious activity. To learn how to restart your computer in Safe Mode, go to this link.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
With a few clicks with your mouse, you can see what’s running on your system’s background. As a start, open the Windows Task Manager by typing “task manager” in the search bar and pressing Enter. Look in the Processes tab for processes that have unusual names or high CPU/RAM usage, as well as processes that perform tasks like ad generation and redirection.
Investigate each suspicious process by right-clicking and selecting Open File Location from the context menu. If you right-click on the process name and open the file location folder, you’ll see all of the files associated with it.

Run a virus scan on these files to make sure they aren’t infected with anything malicious. A free scanner is available below so that you can scan your files.

Removing any scanned files that your scanner warns you of being dangerous is highly recommended. If you want to successfully delete those files, however, you may first need to stop the process that uses them. Right-click on the process in the Task Manager and select “End Process” from the quick menu that pops up. You can now try to delete the files by going back to the original File Location folder.

In the third step, we will show you how to scan your computer for any potentially harmful software. Hold down the Windows key while simultaneously pressing the R key. Type appwiz.cpl in the Run box that appears on the screen and click OK.

The Control Panel window will display all installed software on your computer in a list. To see the programs that were recently installed, you can sort the results by the date they were installed. Do your homework before uninstalling any piece of software. Once you have found enough evidence that a given program is linked to the browser hijacker that you want to remove, select that program from the list and then click Uninstall at the top of this window to remove it from your system. After you are done, close the Control Panel window and move on with the next instructions from this guide.
Type msconfig in the Windows search bar and hit the Enter key. After this action, System Configuration will appear on the screen.
View and disable startup items associated with Frameboxxindore.com from the System Configuration Startup tab. In order to prevent the hijacker’s startup items from being activated when your computer is restarted, remove the checkmark from those items.


*Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
You can restore your computer’s DNS settings to their original state by following the instructions below.
- Type “Network Connections” in the Windows search bar and then press Enter.
- Choose Properties from the context menu by performing a right-click on the network adapter currently in use.
- This will open a new window where you can select the Internet Protocol Version 4 (ICP/IP) settings and then click on the Properties button bottom right.
- To access the Advanced settings, select obtain DNS server address automatically and then click the Advanced button in the new window that opens.
- To get rid of any rogue DNS entries, go to the DNS tab and click the Remove button in the newly displayed window. Once you click OK, the changes you made will be saved.

If you press Windows and R at the same time, a new Run window will appear. Enter the following command and press the OK button:
notepad %windir%/system32/Drivers/etc/hosts
Once you press the OK button, you should see a new file in your Notepad program called Hosts. Check to see if any of the IP addresses listed below “localhost” are suspicious.
Any IP addresses you find that don’t look trustworthy in the file should be copied and posted in the comments section below this guide.


Searching your computer’s registry for entries related to potentially unwanted software is essential to removing browser hijackers. Potentially unwanted software can reinstall itself if these registry entries are not removed. As a result, we strongly recommend that you read each and every one of the following steps in full.
Enter regedit in the Windows search bar and hit Enter. The Registry Editor will appear on the screen.
Hold down the CTRL key while pressing F to open a Find window. If you know the hijacker’s name, you can easily search for it. Using the Find Next button, look for any hijacker entries with the same name as the one you’d like to remove. The right-click menu option “Delete” can be used to remove a detected item.
When the Find box returns no results, the left panel of the Editor can be accessed and searched manually:
- HKEY_CURRENT_USER—-Software—–Random Directory.
- HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
- HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
The operating system and the applications on your computer may malfunction if Registry entries are incorrectly removed. So you need to be very careful when dealing with registry files. Using a virus removal program like the one on this page will help you clean up your computer’s registry of malicious software and potentially unwanted programs with ease.

It is more common for users to focus on removing the unwanted software from their primary browser rather than checking all of their browsers for hijacker-associated changes. However, in this way, the hijacker remains in the other browsers and keeps reminding of its presence. For this reason, we have prepared a step-by-step guide on how to remove the hijacker from three of the most popular browsers.
Right-click on the browser shortcut icon and select Properties from the pop-up menu.

It will open the browser’s Properties window. Click on the Shortcut tab and check the Target section to see if anything new has been added after .exe. After removing everything there as shown in the image, click OK to save your changes.

![]() Remove Frameboxxindore.com from Internet Explorer:
Remove Frameboxxindore.com from Internet Explorer:
Open the browser and then click the gear icon in the upper right corner of the window to access the main menu. Select Manage add-ons from the drop-down menu and remove any extensions or add-ons linked to Frameboxxindore.com from there.
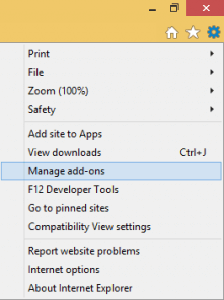
In addition to that, click again the gear icon and select the Internet Options to see if anything has changed there. Ifyou detect any sponsored links on your homepage, remove them and insert a homepage URL that you trust in their place! When you’ve finished editing, click the Apply button.
![]() Remove Frameboxxindore.com from Firefox:
Remove Frameboxxindore.com from Firefox:
The three-line menu button in the upper right corner of Firefox can be used to access extensions.
By clicking on the Remove button in the Extensions menu, you can remove any Frameboxxindore.com -related extensions from your browser. Before attempting to remove an extension, it’s a good idea to disable it first.

![]() Remove Frameboxxindore.com from Chrome:
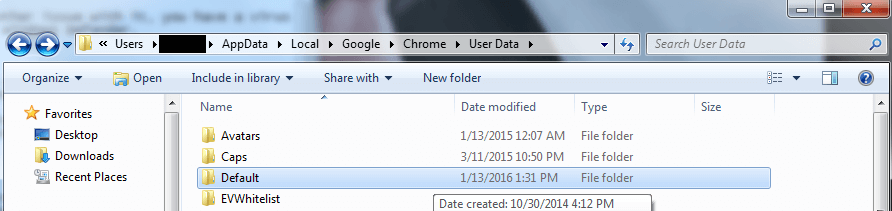
Remove Frameboxxindore.com from Chrome:
In order to complete the next instructions, you must first close Chrome down. Once you’ve done that, head to the following location on your computer:
C:/Users/!!!!USER NAME!!!!/AppData/Local/Google/Chrome/User Data.
You can change the name of the default folder by renaming it “Backup Default”. Right-click and select Rename from the context menu to rename it.
If manual removal isn’t an option due to lack of time or patience on your part, you can always use the removal program we recommend on our website. Make sure there are no suspicious files left behind by using our free online virus scanner. If you have any questions, feel free to ask them in the comments section below and we’ll respond as soon as possible.


Leave a Comment