Galaxy Swapper
Galaxy Swapper is a software associated with the game Fortnite, offering features related to in-game cosmetics. It allows users to download and enjoy their favorite items, suggesting a focus on enhancing the gaming experience by personalizing the appearance of in-game characters. This software is a free Fortnite skin changer built in WPF (Windows Presentation Foundation), that boasts a user-friendly interface and gives players the ability to modify game files to replace a cosmetic they own with one they desire. However, the Galaxy Swapper v2 has raised concerns due to a significant number of users reporting Fortnite account bans after using it. In light of these concerns, we decided to conduct thorough research on the matter and provide you with valuable insights and assistance in addressing any potential issues that may arise from this software.
Galaxy Swapper V2 is promoted as a safe software for customizing Fortnite cosmetics, however, users should exercise caution when using it, as there are reported cases where this has caused a ban in Fortnite user accounts.
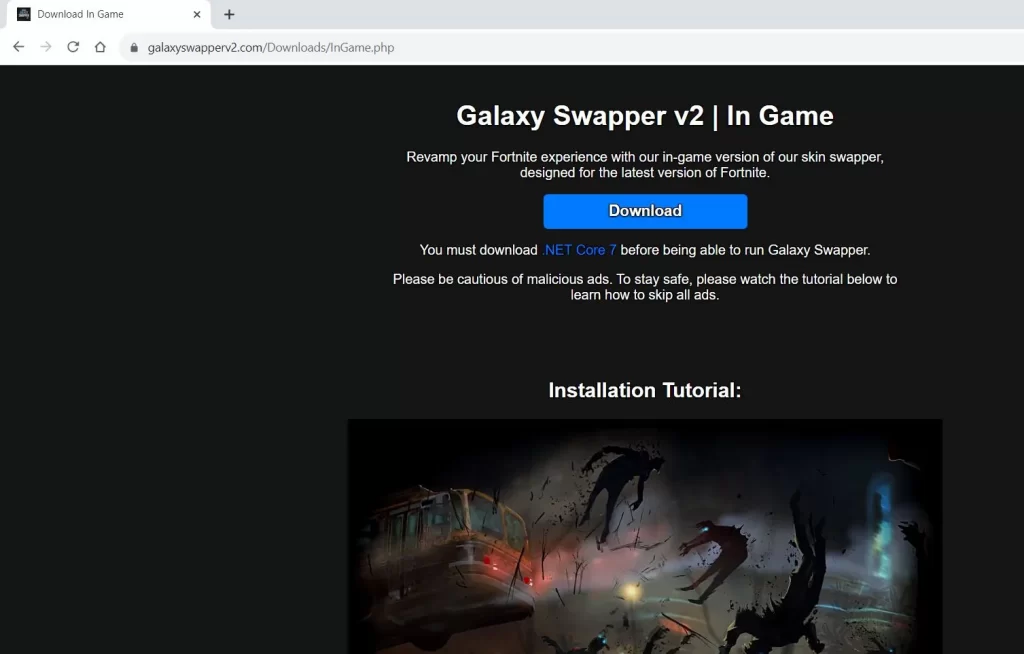
Galaxy Swapper V2 download
The Galaxy Swapper V2 download file can be downloaded from its official website. It typically requires users to claim a free key, available every 48 hours, to gain access to the software’s features. However, software with the same name may strategically be distributed through unofficial channels and unwary users may inadvertently install it by visiting questionable websites or becoming targets of spam campaigns. This is a deceptive tactic used by cybercriminals to facilitate the widespread distribution of different malware through programs like the Galaxy Swapper v2 download and other fake software updates or attractive deals. Therefore, users should stay vigilant against such tactics and the potential threats that they may hide.
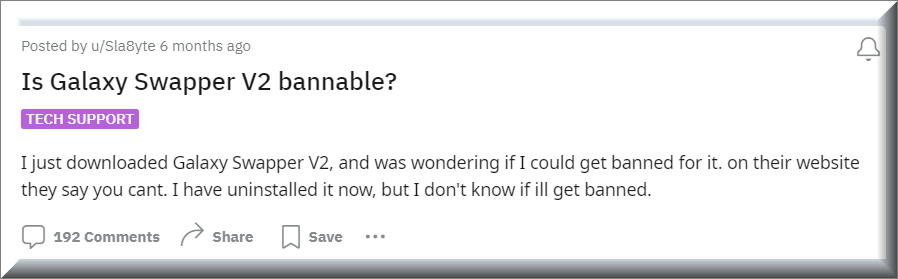
Is Galaxy Swapper V2 bannable?
Whether using Galaxy Swapper V2 is bannable in Fortnite is an important question for many players. This is because, modifying game files, even for cosmetic purposes, can be against the terms of service of many online games, including Fortnite. Using such software might carry the risk of account suspension or banning, depending on the game’s policy on modifications. Therefore, players considering using Galaxy Swapper V2 should weigh the potential risks against the benefits and understand the game’s terms of service regarding file modifications to avoid any unintended consequences.
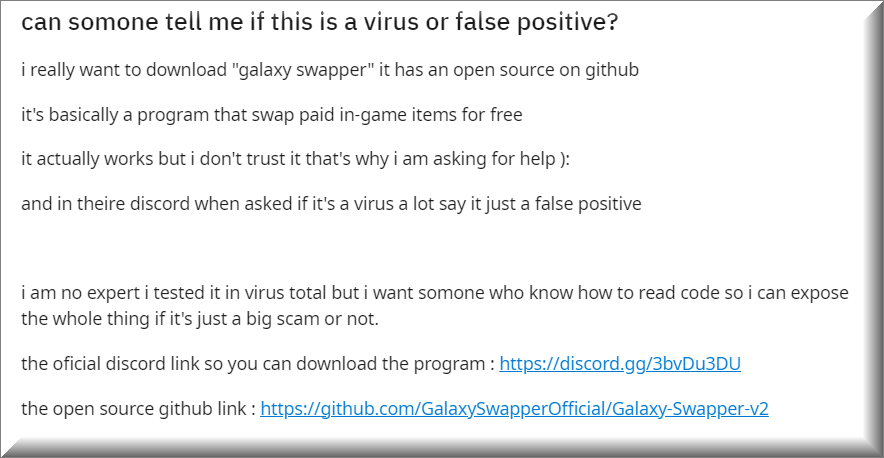
Is Galaxy Swapper V2 a virus?
Galaxy Swapper V2 is often referred to as a virus due to concerns about its safety and potential impacts on users’ computers. This classification is technically incorrect and stems from doubts about the authenticity and the origin of this Fortnite skin swapper, which may have rogue code hidden in its file, if obtained from unofficial sources. The software has been wrongly labeled as the Galaxy Swapper v2 virus also because some users have raised questions about its unusual website appearance, and the possibility of a malicious version of the software distributed under the same name, that could pose potential dangers. If you are concerned about being infected with such a version that you have obtained from a questionable source, and you have detected potential issues stemming from this software, below, we’ve prepared a step-by-step guide that explains how to remove it.
Galaxy Swapper V2 ban Fortnite account
The Galaxy Swapper V2 ban Fortnite account risk is an issue for many, as it could potentially lead to serious account-related consequences. Game developers often have strict policies against modifications that provide unfair advantages or alter the game experience in ways not intended by the developers. Violating these terms can lead to account suspension or permanent bans, impacting the player’s ability to access the game. Therefore, it is vital for players to understand Fortnite’s terms of service regarding the use of this third-party software and modifications, as well as take into consideration any safety concerns related to it.
SUMMARY:
| Name | Galaxy Swapper V2 |
| Type | Trojan |
| Detection Tool |
How To Uninstall Galaxy Swapper v2
To try and remove The Galaxy Swapper v2 virus quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Galaxy Swapper v2 virus extension (as well as any other unfamiliar ones).
- Remove The Galaxy Swapper v2 virus by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of The Galaxy Swapper v2 virus and any other suspicious items.
If this does not work as described please follow our more detailed Galaxy Swapper v2 virus removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the Galaxy Swapper v2 virus app and kill its processes
Uninstall the Galaxy Swapper v2 virus app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from the Galaxy Swapper v2 virus. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to the Galaxy Swapper v2 virus, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to the Galaxy Swapper v2 virus.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo The Galaxy Swapper v2 virus changes made to different system settings
Undo The Galaxy Swapper v2 virus changes made to different system settings
It’s possible that the Galaxy Swapper v2 virus has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for specific system elements that may have been affected, and pressing Enter to open them and see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window


Leave a Comment