*Source of claim SH can remove it.
The Geek Squad email scam
The Geek Squad email scam is aimed at tricking users into disclosing sensitive personal information to the scam’s orchestrators. The Geek Squad email scam targets are sent fake emails that state the user’s subscription to the Geek Squad company’s services has been automatically renewed.
Such email scams are very common and have been that way for a long time. By now, most users with any experience with using the Internet should know not to pay any attention to random email letters that are related to services or offers that the user doesn’t use/isn’t interested in. However, the thing about the Geek Squad scam that grabs the attention of its potential victims and, at the very least, makes them open the fake letter is that the bogus renewal is tied to a $399.99 fee that, according to the text in the letter, has been (or will be) withdrawn from the user’s bank account. In all likeliness, most people who receive such Geek Squad scam messages aren’t actual customers of the legitimate Geek Squad company, but even so, seeing that there’s a chance you may be charged $399.99 is undoubtedly enough for many people to at least use the contact information provided in the email in an attempt to determine what’s going on, regardless of whether they are customers of Geek Squad or not.
What is the Geek Squad email scam?
The Geek Squad email scam is a common type of online scam that lures people into sharing sensitive data like banking details and credit/debit card numbers. The Geek Squad email scam works by lying to the user about an automatically renewed Geek Squad subscription.
Obviously, the goal of the scammers is for the potential victim to actually use the provided contact information, which is typically a phone number, in an attempt to cancel their renewed subscription and get their $399.99 back (which hasn’t actually been withdrawn). Once the number is called, the user would likely be told that, in order to cancel their subscription, they need to provide a certain piece of personal data, which would usually be their credit or debit card numbers or other banking information. Once the data has been disclosed, the scammers could easily drain the user’s banking account before the victim realizes what has happened.
In many ways, this is a very blatant and obvious email scam that most users should be able to recognize from a mile away. Needing to call a random sketchy phone number to cancel an automatically-renewed subscription only to be told that, to complete the cancellation process, you need to provide details about your banking account, debit or credit card, or another type of highly-sensitive personal data, adds up to a bag full of red flags that most people should be able to recognize immediately. Despite this, the fact that this scam is as widespread and as successful as it is is a testament to how gullible an intimidated Internet user could be.
The Geek Squad email scam 2022
The Geek Squad email scam in 2022 is one of the more common and successful scams, but there are many others like it. Therefore, even if that strange message in your inbox is not about a renewed Geek Squad subscription, you should still be careful.
For some time, the Geek Squad email scam campaign seemed to have gone away, but as it turns out, it has simply been lying dormant. Until now, the last instances of Geek Squad scams were in 2021, but recent reports about financially-motivated scams that use a Geek Squad subscription renewal as a pretext indicate that the same scammer or group of scammers have reappeared. Case in point, a member of the East Midlands Cyber Resilience Centre (EMCRC) recently reported getting targeted by the Geek Squad scam. The EMCRC member confirms that the scam scenario is that the potential victim is sent a message in which they are informed about an automatic renewal of their subscription to Geek Squad (a Best Buy subsidiary specializing in electronics maintenance and repair). According to the message, the renewal would cost around $400 which would be automatically charged. Since the scammers have no way of knowing which of their targets are actual Geek Squad customers, such scam messages usually end up in the inboxes of people who have never used the services of Geek Squad.
There are many helpful tips and safety rules that, if adhered to, will help you prevent falling victim to this or any other similar type of online scam. A closer examination of the Geek Squad email scam should prove informative and helpful for anyone who’d like to be able to better recognize the potential red flags that signify there may be something fishy about a given email letter.
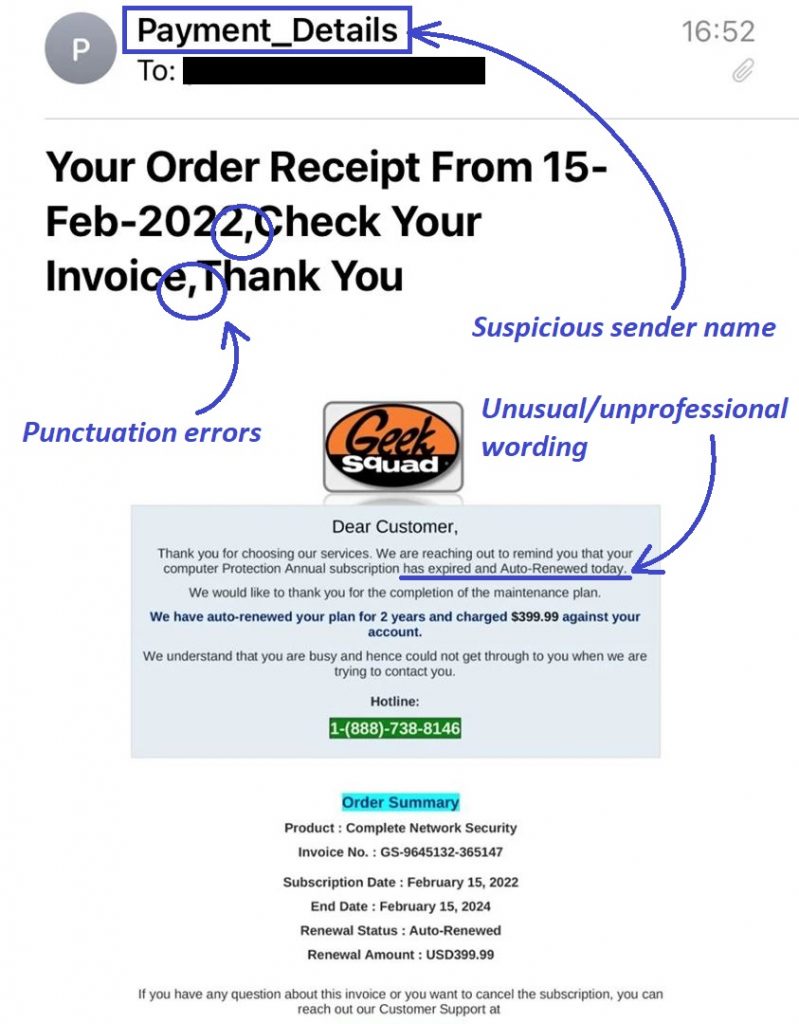
First, let’s focus on the sender of the scam message. In many such email scams, the sender’s name is not the same as the person or entity they are trying to impersonate. In the current case with the Geek Squad scam, many of the emails related to this scam campaign aren’t sent from accounts that have Geek Squad as their account names. Case in point, pay attention to the sender’s name in the image of one such scam email that we’ve shown above – the name “Payment_Details” is unlikely to be used for an official email of a reputable company, and also doesn’t suggest any relation to Geek Squad.
Another giveaway related to the sender’s name is when the name and the email address differ. Even if the sender’s name is Geek Squad (or something similar), the actual email address would either be something entirely different, or there would be a spelling mistake in the address’ name (oftentimes both). Also, one of the best things you could do to determine if a given email sender is trying to impersonate a certain company or organization is to go to the site of said company/organization and check what their official email(s) is in the site’s contacts page. If the two emails don’t match, you should ignore the contents of the suspicious message and delete the latter.
Next, you should also closely examine the actual text in the message and focus on how it’s written and if there are any grammatical, spelling, or punctuation mistakes in it. An email from a reputable company such as Geek Squad would not have any mistakes in its email messages.
These are only three types of red flags that could give away a scam email message. There are many more, but these are the ones we deem the easiest to notice and so if you make sure to be on the lookout for them the next time you are going through your online mail, you should have no problem identifying the ones that are likely to be fake scam messages, so that you’d know to delete them.
Geek Squad Tech Support
The Geek Squad tech support is often used as the front of a blatant email scam aimed at collecting and using sensitive user data. The scammer impersonates the tech support of the actual Geek Squad company and thus tricks their victims into providing personal data.
A very easy way to tell if the Geek Squad tech support phone number, shown in a suspicious email you’ve received, is fake is to simply go to the official Geek Squad website and check their contacts page. Compare the information given in the email and the official contacts page of Geek Squad and if the information doesn’t match, then you’d know that the email is a scam and should be ignored.
Furthermore, even before you do that, the fact that the people who’ve sent you the sketchy email are asking for your personal data should immediately raise a red flag in your mind. The actual Geek Squad tech support team wouldn’t request that you share such personal details in order to cancel your subscription. Therefore, if you ever get such an email, it’s best to ignore it and delete it from your inbox.
SUMMARY:
| Name | Malware related to the Geek Squad email scam |
| Type | Trojan |
| Detection Tool |
*Source of claim SH can remove it.
How to get rid of the Geek Squad email scam 2022?
To get rid of the Geek Squad email scam, first, we recommend blocking the sender’s email address:
- Go to your Gmail (or another email provider) and open the scam message.
- Click the three dots in the top-right.
- Select Block *sender name*.

Additional actions that we recommend are to also use the Report spam and Report phishing buttons from the three-dot menu in order to let Gmail know that this email address is used by scammers to trick users, which should hopefully lead to the address being taken down.
One important thing that you need to be aware of is that, oftentimes, scam campaigns like this one are closely related to the distribution of malware. There’s a chance that a rogue app that’s already on your computer has led to you getting targeted by the Geek Squad scam. Conversely, it’s also not excluded that, if you’ve interacted with any links present in the message, you may have inadvertently landed some undesirable software that’s currently on your PC. In either case, we strongly recommend checking your system for any programs and software components that are unfamiliar and that may be unwanted. In some of the more serious scenarios, getting targeted by such a scam campaign may also mean that there’s a Trojan Horse on the computer. To make sure that everything on your PC is safe and continues to be this way, we advise you to complete the following guide.
Step 1
*Source of claim SH can remove it.
For the first step, you should search for Apps & Features in the Start Menu search bar, click the first result, scroll down a bit, and take a look at what items are shown in the list of programs installed on your computer. We recommend sorting the items by their installation date so that the most recent ones are shown at the top. You should be looking for anything unfamiliar, suspicious, and/or potentially unwanted and if you find such a program or app, you need to select it, click Uninstall, and perform the uninstallation.

Step 2
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Now you need to open the Task Manager by pressing Ctrl + Shift + Esc, and see what processes are listed in the processes tab. If there are any unusual and unfamiliar processes with high RAM or CPU consumption as well as processes that seem related to the program(s) from the previous step, you should loop up their names to see what comes up in the results. If a certain process in your Task Manager is related to a rogue program, you will most likely find online relevant results that confirm it.
Another thing we recommend doing is to right-click the questionable process, go to the File Location Folder, and scan whatever files are stored there with the next malware-detection tool.


If one or more of the scanned items are detected as threats, you’d know that the related process is something that shouldn’t be running on your PC.
In case you do find out that one or more processes in the Task Manager are rogue and potentially dangerous, open their location folders, quit them in the Task Manager, and then delete the contents of the related folders.

Step 3
If there’s any malware left on your PC, it’s advisable to enter Safe Mode – this will keep any potential threats from interrupting you during the next steps. If you need help with booting your PC in Safe Mode, this guide can help you with that.
Step 4
There are several types of settings in your system that you need to go to and override in them any changes that may have been made there any undesirable or rogue programs that could currently be on the computer. One by one, search in the Start Menu search bar for each of the following items, open them, and perform the provided instructions:
Services.msc – Explore the list of services that will open, looking for anything that looks suspicious and may be related to a rogue program on your computer. If a potentially harmful service is found, right-click it, open Properties, set the Startup type to Disabled, and click OK.


Task Scheduler – First, click on Task Scheduler Library in the top-left, then look for suspicious and/or rogue tasks in the list that appears, and delete any tasks that may be linked to malware.

System configuration/msconfig – Click on the Startup tab, then, if you are on Windows 8 or later, click Open Task Manager, and look for apps that may be harmful or unwanted. If you notice one or more such apps, disable it so that it doesn’t start automatically when you turn on your PC.

Regedit.exe – To open the Registry Editor (regedit.exe), you must first click Yes to provide your Admin approval. Then, when the Editor opens, press Ctrl + F, type the name of the program you uninstalled in Step 1, and search for related items. If anything is found, delete that item, search again, delete the next result, and continue this way until all related items are removed. If you uninstalled more than one program in Step 1, do this for each of them.

Once you’ve deleted all found items, use the panel to the left to navigate to the following Registry locations/folders, and then look at what items (Registry keys) are available in them. If you notice any keys with suspiciously-long names that appear randomly generated, tell us about them in the comments, and we will let you know if you’d need to delete them.
- HKEY_CURRENT_USER/Software
- HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run
- HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main
Step 5
Finally, there are several folders on your PC that you should go to and delete from them any potentially rogue files. Before you do that, however, type Folder Options in the Start Menu, and open the first result. Then click View, enable Show hidden files, folders, and drives, and click OK – this will let you see and delete hidden files, thus helping you ensure that no rogue data’s left in the following folders.

Now, click in the Start Menu again, type %AppData%, and press Enter. Now sort the items in the folder that appears by creation date and delete everything created after you first began to receive the scam messages. Once you are done with the AppData folder, do the same thing with these other four folders:
- %WinDir%
- %LocalAppData%
- %ProgramData%
- %Temp%
Once you reach the Temp folder, rather than deleting only the most recent items, you should delete everything. Since this folder usually contains hundreds or thousands of items, the easiest method of deleting everything is to press Ctrl + A when in the folder, press Del, and press Yes.

Additional Help
Even though it’s often enough to perform the manual steps to check your system and delete potentially rogue software and data, malware is sometimes able to remain hidden or re-enter the computer even after having been deleted with the help of helper files hidden deep in the system. For this reason, we recommend that you combine the steps we’ve shown above with the professional anti-malware tool that you will find linked on this page, as the latter can perform a deep scan of your system, detect even the most obscure rogue files, and components, and remove them from your PC so that you’d know there’s no harmful software left in the system.

How the heck do I remove SpyHunter5 ??? I tried uninstalling it the normal way with Windows, but it still shows up in the directory C:\Program Files\EnigmaSoft\SpyHunter. I want to uninstall it and delete every trace of it on my PC.
Hi Edward Martin,
if you uninstalled it, then maybe these are some user settings left behind. If you uninstalled it like an App, then you will be fine to delete the whole folder.
How do I know you’re not part of Geek Squad????
Hi Ellen,
Howtoremove.guide is created in order to help people in need to remove any kind of viruses and help them in the process. We are simply trying to help and we have nothing to do with Geek Squad.
My outlook is spammed by African Manhood ACE for instance and 100s of similar product emails. You cant block them. Do you know how to get rid of them?
Hi William,
if it is in your email it is probably spam. Try contacting Microsoft and ask them if they can resolve this. Outlook should filter the spam emails and put them in a separate Spam folder.