Generic.malware.ai.dds
If you find yourself here, it’s likely that you’ve noticed some unusual activities on your computer, like sluggish performance, unexpected system crashes, or some unfamiliar alerts and program errors. While these issues can have various causes, one of them might be a lurking Trojan threat known as Generic.malware.ai.dds. This type of malware has the ability to mimic regular system processes and files, gradually destabilizing and compromising your computer, the longer it remains there. Generic.malware.ai.dds, similarly to threats like Trojan.Generic.hetyo and CloudCheck.exe, can gain access to your system through different channels, disguising itself within spam messages and email attachments, masquerading as legitimate software or enticing free programs, or lurking in malicious websites that deceive you into downloading the threat under the guise of a helpful application.
What is generic.malware.ai.dds?
Generic.malware.ai.dds stands as a notorious Trojan Horse malware, well-versed in the art of deception. It often masquerades as a seemingly innocent and free download, luring unsuspecting users into installing it. After it gets inside the system, however, the malware can execute a number of harmful activities that may cause sudden crashes of regular programs, corrupted files, and even a potential theft of personal information from the compromised computer. It can be very challenging for inexperienced users to detect Generic.malware.ai.dds before it inflicts significant harm because there usually are no visible symptoms before the attack. Therefore, to stay one step ahead, we recommend you to rely on a robust antivirus software and exercise utmost caution when dealing with email attachments and spam messages.
Is Generic.malware.ai.dds a Virus?
It’s crucial to understand that Generic.malware.ai.dds is not an ordinary virus. It operates as a ruthless Trojan Horse with capabilities far surpassing those of a computer virus. In fact, unlike typical viruses that replicate and spread on other files and machines on their own, Generic.malware.ai.dds cannot do that. This threat employs stealth to deceive web users about its true intentions and harmful nature in order to get installed on a system. Often disguised as legitimate software, it tricks victims into downloading and executing it without suspicion. Once this is done, the malicious actors behind the Trojan can exploit the compromised system, gaining full access and enabling a wide range of criminal activities.
Generic.malware.ai.dds Virus
The Generic.malware.ai.dds virus may stealthily harvest sensitive information, such as login credentials, personal data, financial details, and more, and then use it for fraudulent purposes like identity theft, financial fraud, or blackmail. The attackers who are in control of the Trojan can also remotely manipulate the system, and carry out various malicious actions, such as spreading spam, launching Distributed Denial of Service (DDoS) attacks, distributing malware to other systems, or even turning the infected device into a part of a botnet for further cyber-attacks. The consequences of these exploitations can be devastating, causing significant harm to both the individual infected with the Generic.malware.ai.dds virus and organizations targeted by the malevolent actors.
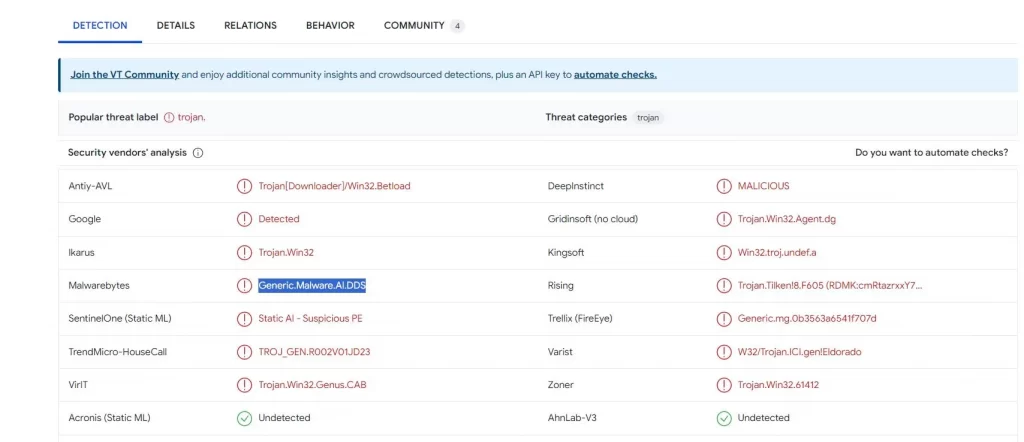
The generic.malware.ai.dds virus total detection
The Generic.malware.ai.dds virus total detection possesses the unique ability to remain dormant and undetected, concealing its presence until the hackers behind it decide to launch a specific attack. Operating stealthily, this malware cleverly disguises itself as regular system files, making it challenging for inexperienced users to detect it without proper guidance. The Generic.malware.ai.dds virus total detection can even disable some antivirus programs, leaving the system vulnerable and defenseless. For these reasons, if your computer has fallen victim to this insidious Trojan Horse, we urge you to follow the step-by-step removal guide below to swiftly eliminate the threat and any related potentially dangerous files.
SUMMARY:
| Name | Generic.malware.ai.dds |
| Type | Trojan |
| Detection Tool |
Generic.malware.ai.dds Removal
To try and remove Generic.malware.ai.dds quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Generic.malware.ai.dds extension (as well as any other unfamiliar ones).
- Remove Generic.malware.ai.dds by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Generic.malware.ai.dds and any other suspicious items.
If this does not work as described please follow our more detailed Generic.malware.ai.dds removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the Generic.malware.ai.dds app and kill its processes
Uninstall the Generic.malware.ai.dds app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from Generic.malware.ai.dds. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to Generic.malware.ai.dds, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to generic.malware.ai.dds.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo Generic.malware.ai.dds changes made to different system settings
Undo Generic.malware.ai.dds changes made to different system settings
It’s possible that Generic.malware.ai.dds has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for specific system elements that may have been affected, and pressing Enter to open them and see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window


Leave a Comment