Gesd
Gesd is a harmful Windows-targeting virus that encrypts user files, thereby restricting access to them. Experts categorize Gesd as Ransomware due to the ransom message it shows the user after it encrypts the files. The Gesd ransom is demanded for the file’s release.
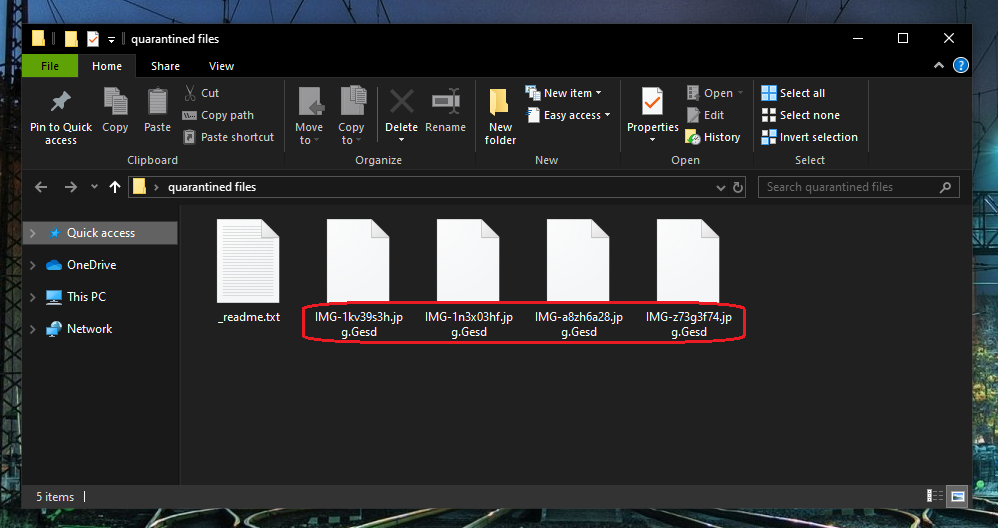
The Gesd Virus will encrypt your files and leave a _readme.txt file behind.
Gesd is a really harmful virus of the Ransomware family and anybody who encounters on their computer gets all of their personal data encrypted. The Gesd encryption is very advanced and normally only a special key held by the blackmailers may unlock it. The hackers behind this encryption-virus want your money in exchange for the private key that will set all locked files free. However, there are a number of problems with the ransom payment as a potential course of action after a Ransomware attack. Gesd is a malware virus specifically made to get the money of as many users as possible by keeping their files hostage for blackmailing leverage. Once the Gesd victims pay the sum requested by the hackers, the latter have no reason to keep their promise. Indeed, in many instances where users pay the sum, the criminals behind the Ransomware refuse to provide their victims with a functional decryption solution. Of course, at that point, the ransom money is gone in the hands of the hackers and nothing the victim does could bring it back. This is why the more advisable course of action, when faced with Ransomware encryption on your files, is to try to ameliorate the situation without interacting with the hackers or sending them your money. Unfortunately, this too doesn’t guarantee success. The Gesd virus is an advanced piece of malware that would keep your data under its encryption even after you remove the threat itself. The Gesd file encryption is very difficult to break, but there may be methods to circumvent it.
In the guide following this article, we will tell more about those methods, but you must bear in mind that when dealing with Ransomware there are simply no guarantees. Sometimes, there are specialized decryptors for different versions of Ransomware that have been created by reputed security specialists, but not all Ransomware viruses have a corresponding decryptor tool. We have a list of such decryptors on our site as well as some other suggestions on how you may be able to recover some of your data, but before you get to that, you must first remove the infection from your computer. As we said, this won’t set your data free but it will prevent the future encryption of new files you create or download or the re-encryption of any data you may manage to recover.
The Gesd virus
The Gesd virus is a malware program that employs encryption to lock-up files located on the hard-drives of Windows computers. The aim of the Gesd virus is to harass its victim into spending money on a decryption key that is held by the malware’s creators.
The first step towards mitigating the severe consequences of the attack from this virus is to remove the virus itself. As we pointed out, this will both make your computer safer for future use and aid you with your attempts to restore the locked data. You may be able to remove the virus manually if you follow the guidelines presented on this page, but to increase your chances of fully eliminating everything related to this Ransomware, our advice is to also employ the recommended anti-malware program linked below. Using both the removal software and the manual instructions, you should be capable of getting rid of everything that this virus may have left in your system.
Warning: One of the best ways to recover Ransomware-encrypted files is through the use of external backups from other devices. However, you MUST NOT connect those devices to your computer if the Ransomware is still in it, or else the files in the backup will get encrypted as well.
The Gesd file encryption
The Gesd file encryption is what keeps the data on the infected computer inaccessible. The Gesd file encryption requires a unique key to unlock it and without that key, it’s usually not possible to access any of the encrypted files.
If you don’t want to pay for the decryption key, however, you will need to find a roundabout way of dealing with the encryption. There are several options you can try and though none of them are guaranteed to succeed in recovering your files, it is still better to try them all before even thinking about paying the ransom to the hackers. The alternatives we mentioned can be found in the recovery section of our guide down below.
SUMMARY:
| Name | Gesd |
| Type | Ransomware |
| Detection Tool |
Gesd Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible). You can find the removal guide here.

Very nice way and tool to understand,
Hi,
I have .gesd virus in my external drive that came from my pc as i connect the cable. Kindly help me to remove from external as i have office data in my external drive and i am depressed now.
Hi Asim,
follow the guide and you will remove the ransomware. At the end of the guide you will find links to a Decryption page, where you can find methods for decryption.