*Ggeo is a variant of Stop/DJVU. Source of claim SH can remove it.
Ggeo
Ggeo is a cyber infection of the ransomware type that “kidnaps” digital files from the system of a given computer and demands a ransom payment for their liberation. Ggeo uses encryption to restrict access to the files and displays a ransom-demanding message on the screen of the infected machine.
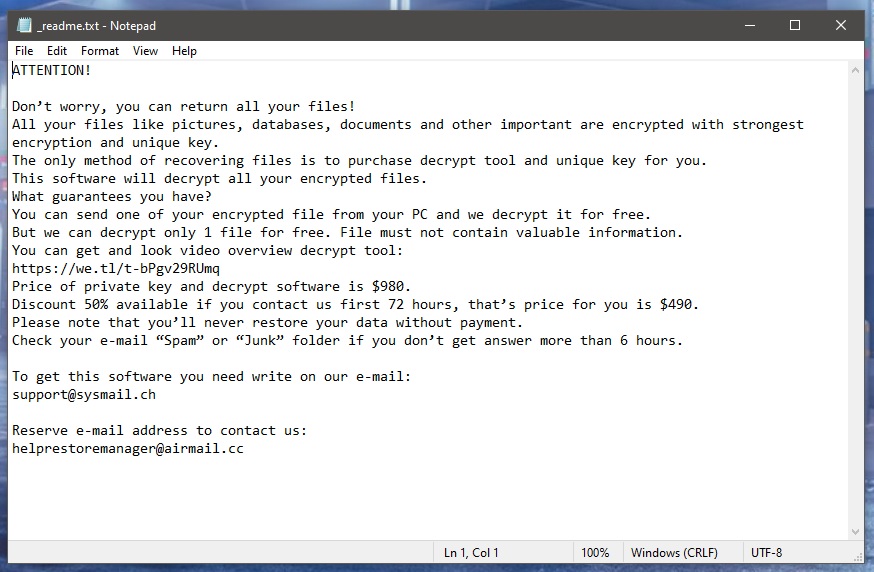
We wrote this article to help you understand the nature of one specific Ransomware – Ggeo – and to find smart and hopefully effective ways to counteract its attack. Generally speaking, Ggeo is a data-encrypting ransomware variant that sneaks into your system without your consent. After doing that, it does not allow you to access the information that it has encrypted. The malicious piece of software even displays a message to let you know what the hackers behind this cyber attack are expecting from you. Usually, this is a money transfer that needs to be made within a given deadline to a specifically mentioned crypto account. In exchange for your money, the crooks offer to send you a decryption key with the help of which you can restore your files to their previous state.
The Ggeo virus
The Ggeo virus is a malicious piece of software that usually performs a rigorous file-encryption process in the background of your system. After completing this process, the Ggeo virus asks for a money transfer from its victim in order to undo what has been done.

Once the entire encryption process is complete, nothing can be done. Unfortunately, the viruses that encrypt files are exceedingly difficult to combat. In fact, even experts could find removing the virus and, at the same time, saving the files very difficult. However, in most situations only one of the above is possible. As terrible as this sounds, when it comes to data encoded by Ransomware infections, there are indeed very small chances of success. However, trying to remove the malware is still a solution that can leave you with a safe and virus-free computer. Therefore, self-help removal guides like the one below are worth the try if you don’t want to risk sending your money to some anonymous criminals. Consulting a specialist may indeed cost you some money but is still a better option than sponsoring extortionists. Or perhaps buying professional software is what you will need to remove the infection.
The Ggeo file encryption
The Ggeo file encryption is a process that blocks some of your very important files and makes them unavailable to anyone. The worst part about the Ggeo file encryption process is that it typically goes unnoticed by most security programs and cannot be stopped on time.
Obviously, prevention is the best way to deal with ransomware; that’s why our best advice is to take the necessary precaution measures to avoid such threats in the future. Also, do one smart thing and create backup copies of the files that you never want to lose. In this way, threats like Ggeo, Ggwq, Ggew cannot blackmail you as you can always have access to your information. And last but not least, invest in reliable anti-virus software that has comprehensive databases and can alert you of possible infectious spots or even remove security threats on time.
SUMMARY:
| Name | Ggeo |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Data Recovery Tool | Not Available |
| Detection Tool |
*Ggeo is a variant of Stop/DJVU. Source of claim SH can remove it.
Before you begin this guide
Please, take note of the following aspects before starting the guide:
- External drives, USB sticks, phones, or tablets still connected to your PC must be unplugged immediately!
- We recommend against paying the ransom, but if you are still going for it, then it is advisable to wait for after the payment is made to remove the virus using the next guide.
- It may look like Ggeo is not in your PC anymore even without performing the removal steps. Even in such cases, however, it’s still recommended to complete the guide.
Remove Ggeo Ransomware
To remove Ggeo from your computer, you can either use the powerful removal tool posted on this page or complete the next steps in the order they are given:
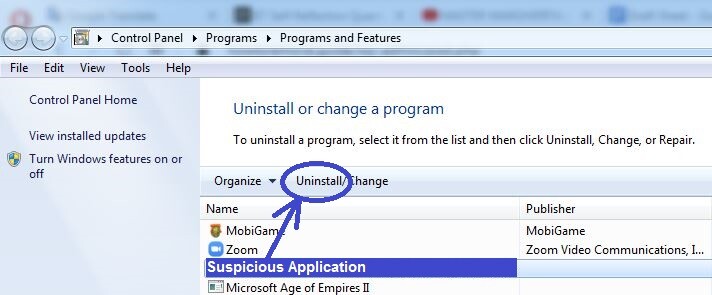
- Search for the software that got your PC infected in the Programs and Features list and uninstall it.
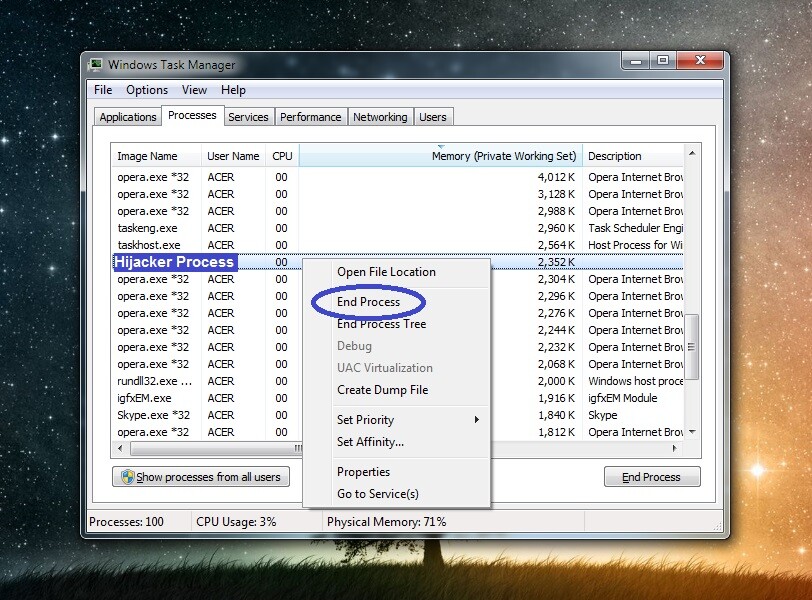
- Make sure to stop any Ransomware processes by ending them in the Task Manager.
- Clean the following folders from malware data: LocalAppData, ProgramData, WinDir, AppData, Temp.
- Clean the following system settings: Task Scheduler, Hosts file, Registry Editor, Startup items list.
To correctly complete every step, please, take your time to familiarize yourself with the detailed instructions we’ve shown below.
Detailed removal instructions
Step 1
Search for Control Panel in the Start Menu, open the Control Panel, and go to Uninstall a Program (Programs and Features). There, you must look for a program installed around the time Ggeo infected you that looks untrusted and suspicious. If you find such a program in that list and think it may be related to the Ransomware infection, right-click its name, then click Uninstall, and complete the uninstallation. If there is a dedicated uninstallation manager, be sure to carefully explore its settings and use the ones that would ensure the full removal of the unwanted program and all of its data and settings.
Step 2
WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Ggeo is a variant of Stop/DJVU. Source of claim SH can remove it.
Open the Task Manager window (Ctrl + Shift + Esc from the keyboard), go to the Processes section, and carefully look for processes that:
- Have unusually high RAM and/or CPU usage
- Have a strange/unfamiliar/suspicious name
- Don’t seem related to any of the legitimate programs on your PC and/or seem related to the suspicious program from the previous step
Google the name of any such processes found in your Task Manager to learn more about them, and also check their folders for malware files. To go to the folder of a given process, right-click the process in the task Manager and select open File Location. Once in the location folder of the suspected process, use the advanced and free malware scanner from below to test each file for malware.


If, based on the information you’ve been able to find on the Internet and the results from the malware scans, you determine that a given process is malicious, end it and then delete the folder of that process.
Step 3
Next, you need to stop Ggeo from running any more harmful processes on your computer. To do this, reboot the PC in Safe Mode.
Step 4
*Ggeo is a variant of Stop/DJVU. Source of claim SH can remove it.
Click your Start Menu, type in the search box below it Folder Options, and then press the Enter key. In the next window, click on View from the top, then see if the Show hidden files, folders, and drives option is enabled, and if it isn’t enable it and then click on OK.
The next thing you must do is type %Temp% in the Start Menu search bar (including the “%” symbols) and press Enter. A folder should open on your screen, and when it does, you must press Ctrl + A, to select everything, and then press Del and click Yes, to delete it.
Using the Start Menu again, go to the folders %AppData%, % LocalAppData%, %WinDir%, %ProgramData%, sort their contents by order of date of creation, and then delete only the files and subfolders created since the virus’ arrival.
Step 5
For Windows 10 users, access the Task Manager, and open Startup. For Windows 7 users, type msconfig in the Start Menu, press Enter, and click Startup in the System Configuration window. In the Startup items list, search for anything that could be linked to Ggeo – any unknown, suspicious, or questionable entries must be unchecked, after which you must click on OK.
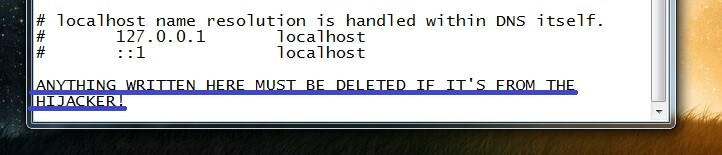
Next, you need to go to the C: drive of your PC, and navigate to the folder Windows\System32\drivers\etc. There, you will see a file named Hosts, which you must double-click and then select Notepad to open it with that program. Once the file opens, scroll down and, if there are any IPs under the “Localhost” lines at the bottom of the text, copy those IPs and send them to us in the comments below this post. We will inform you if those IPs are rogue and if it’s necessary to delete them from the file.
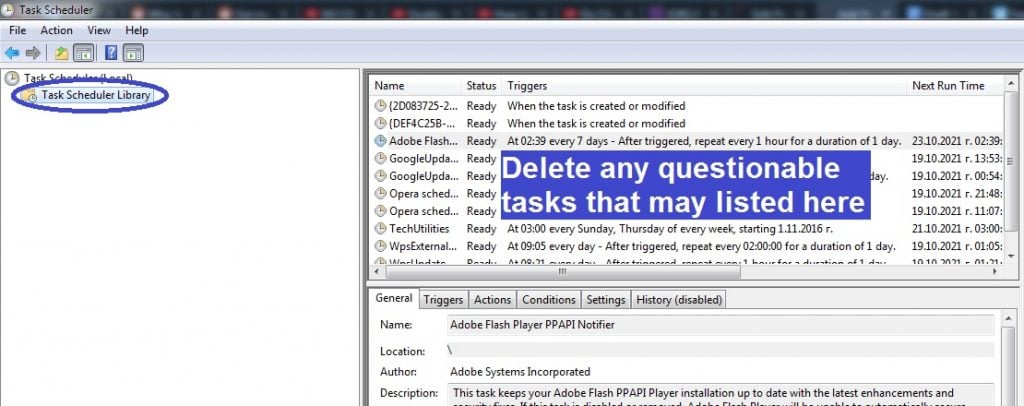
Now you must go to the Task Scheduler app – search for it using the Start Menu and open it. Then open the Task Scheduler Library that should be visible in the top-left corner of the app. Next, look at the different tasks listed in the central pane and delete the ones that seem untrusted or unfamiliar (right-click > Delete or left-click + Del from the keyboard).
Step 6
Open regedit.exe (search for it in the Start Menu), and when you are asked to provide your Admin confirmation to start the app, click Yes.
Press Ctrl + F once the Registry Editor shows up and then type the name of the virus. Click Find Next/press Enter to search for items related to the virus and delete the item that gets found (if anything gets found). Search and delete again and again until no more items are showing up when you click Find Next. After that, repeat the same thing with the program from Step 1 as your search phrase.
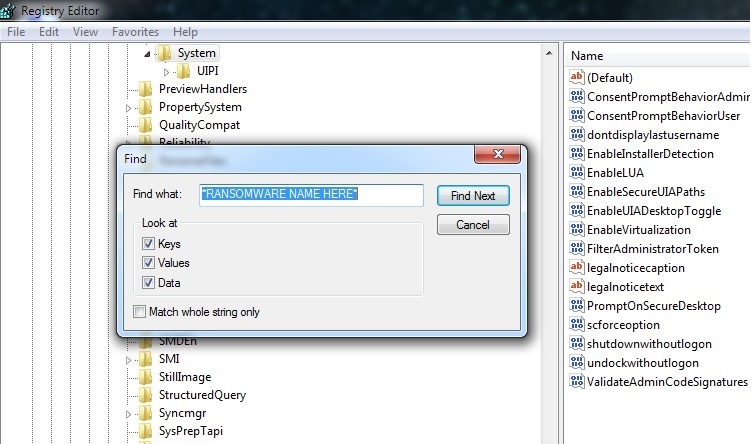
The last thing you must do here is to check the Registry folders lost below for items that have unusual names – main items with names that seem to be a random combination of numbers and letters, much like this “e09r09e09223e09tu20egyt43109rut09u2e3290“. Tell us in the comments about anything like this that you may find, but do not delete it unless we tell you in a reply below your comment that the suspicious item must indeed be erased.
- HKEY_CURRENT_USER > Software
- HKEY_CURRENT_USER > Software > Microsoft > Windows > CurrentVersion > Run
- HKEY_CURRENT_USER > Software > Microsoft > Internet Explorer > Main
If Ggeo is still in the system
It is, of course, possible that trying to delete the Ransomware manually may not always work as intended. If you think or know that the Ggeo virus is still on your computer, we recommend deleting it with the help of the advanced anti-malware program included in the guide above. Sometimes, automatic removal is indeed the only viable option (unless you are willing to reinstall Windows) and so we strongly recommend it in cases where the manual removal steps didn’t yield the necessary results.
How to Decrypt Ggeo files
To decrypt Ggeo files, it’s recommended to first try using specialized decryption software to obtain the private key for your files for free. Note that to decrypt Ggeo files in this way, you will need access to pairs of encrypted files and their original versions.
The good news if you have been hit by Ggeo is that you may be able to restore the files that it has locked on your computer using a specialized file-decrypting program that you can download and use for free. As already mentioned, however, you will need several file pairs that consist of an encrypted file and the original and accessible version of that file. The only condition regarding the files is that they need to be larger than 150 KB. To find the original versions of encrypted files, look in your other devices, cloud storage, or email accounts. Also, before you start the decryption process, you need to be certain that the malware is fully gone. If you still suspect some of the files found on your system may be malware-related, use our free scanner to test them and see if they are safe.
If you have the needed file pairs and are ready to begin the decryption process, here’s what you need to do.
- Select this link and click on the first of the Choose File buttons.
- Find and open the encrypted file version of one of the aforementioned file pairs.
- Click on the second Choose File button, find the original version of the same file pair and open it.
- Select the Submit button to begin searching for the correct key. If the search fails, you should try again with a different file pair.
- Download the app from this link, right-click on it when it downloads, and select Open as Administrator.
- Click Yes to provide your Admin permission, then agree to the Terms of use, and click OK.
- Select a drive or find a browse to a specific location where encrypted files are located and click Decrypt. The decryption process will begin, and your files will hopefully get unlocked once it’s finished. If any of the files do not get decrypted, this means that the private key for them is different – you can try extracting it with a different file pair, but it is also possible that the decryption tool simply doesn’t have the needed key in its database at the moment.

Leave a Comment