GlobeImposter
GlobeImposter is deemed a ransomware type of a computer virus. GlobeImposter is a very dangerous malware which renders the computer it infects almost useless by encrypting all the files and making them unusable. Once the process is finished it will display a message containing instructions for online payment.
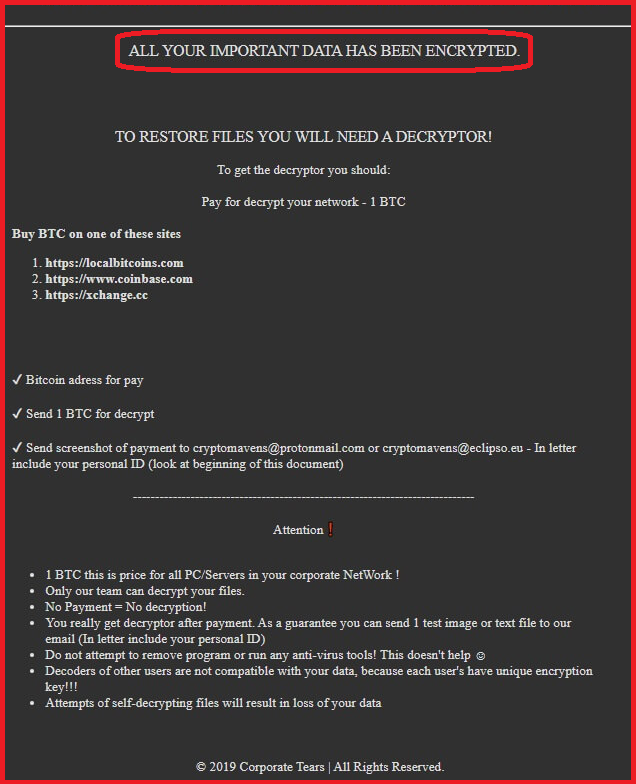
The GlobeImposter Ransomware will display this message.
Ransomware programs have been around for decades now, but it wasn’t until recent years that they became a genuine massive phenomenon, with millions and millions of unique samples being released on the web, making users today watch their every step when using the internet. Well, almost every step. After all, you, dear reader, have ended up here perhaps due to lowering your guard and ending up infected with one of the newest ransomware variants called GlobeImposter Ransomware. Today’s article is dedicated to this particular ransomware virus, the encryption it uses to lock you out of your files and the possible ways you may have landed it in the first place. But aside from that, it is very important that you see to the removal of GlobeImposter Ransomware as soon as possible and for that purpose we have created a detailed removal guide, which you can use for free, just below this article. For those of you, who don’t feel as confident in dealing with system files and deleting things from their PCs, you can also use our specialized removal tool, which will do the job for you in a matter of a few minutes. And last but not least, in our guide we have also included file restoration instructions that may succeed in recovering at least some of your encrypted data. Give them a try to see if they will be helpful for you.
GlobeImposter 2.0
Viruses like GlobeImposter Ransomware use very complex, sophisticated encryption algorithms when working on the files of one’s PC. They first need to locate the file types they’re after, which can be anything from system files to pictures, music and videos. And once that is done, they proceed to create encrypted copies of that data, whilst deleting the originals, which, in turn, leaves the victims with nothing but a pile of useless data. In the majority of cases, this process will run without any interruption or without any symptoms.
Even your antivirus program will most likely be powerless to detect an issue, because encryption is not an inherently malicious process. As a matter of fact, it’s used to protect data, not harm it, which is why most security software will simply ignore it altogether.
Now as for the distribution of these viruses, this still remains a very important part to understanding them and learning how to defend your system against them in the future. We did hint earlier many of the infections could have easily been prevented and that is the actual truth. Applying your common sense when browsing the web can really save you a lot of trouble, even of the ranks of GlobeImposter Ransomware and other ransomware viruses. For example, one of the most common sources of ransomware is still spam email campaigns. You’d think that it’s the oldest trick in the book and people shouldn’t be falling for that anymore, yet here we are. Most commonly the virus will be included as an attached file, even one as seemingly harmless as a Word document or PDF files. Alternatively, the email (or other message) may contain a hyperlink, which you will be encouraged to follow under whatever pretext. The trick is to look out for suspicious signs, like weird email addresses, strange and perhaps even illiterate content of the email itself or even just the subject. Do not under any circumstances interact with the attachments or links in it, unless you are 100% sure it’s trustworthy.
Another very common way of getting infected is by clicking on a malicious online ad. The trick with these is that they can be literally anywhere, on any website. Of course, you’re more likely to find them on sketchy or illegal pages, but to be on the safe side, you’d be wise to simply steer clear of any online popups, banners or box messages. Fake system requests can also be a common source, so be sure to manually install system updates and security patches, as opposed to trusting a random notification that showed up and is offering to do so for you. One last thing we would like to advise you on before you can move on to the removal guide is backing up your most important files from now on. This is essentially what will render any ransomware virus totally harmless and unable to leverage anything to extort money from you.
SUMMARY:
| Name | GlobeImposter |
| Type | Ransomware |
| Detection Tool |
GlobeImposter 2.0 Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Let me ask
How could we decrpt file with .626 extension?
And can I recovery my encrypted file after format C drive??
Thank you
First, you will need to find out what Ransomware has encrypted your files, we advise you to go to our How to Decrypt Ransowmare guide for more detailed information on the matter.
Hi There
Just discovered that my PC and the external hard drive ave been infected by GlobeImposter2.
Alot of the documents are unaccessible. Is there any software programe I can I can use to de-encrypt
and access the lost documents?
Kind regards
Roger
Hello there, for more decryption information, visit our How to Decrypt Ransowmare article (link at the bottom of this article).
Thank you. Is it possible to use SpyHunter 4 to get all the files back?
This is an anti-malware tool that can help you detect and remove mawlare. However, it isn’t a decryptor so it cannot unlock any files that have already been encrytped by a Ransomware. For that, you’d need a dedicated decryptor tool.
Hi All ,
I will require GlobeImposter 2.0 virus exe file if you have any one pl send my below my mail id
Vslknsgr @yahoo .com
Thanks in advance