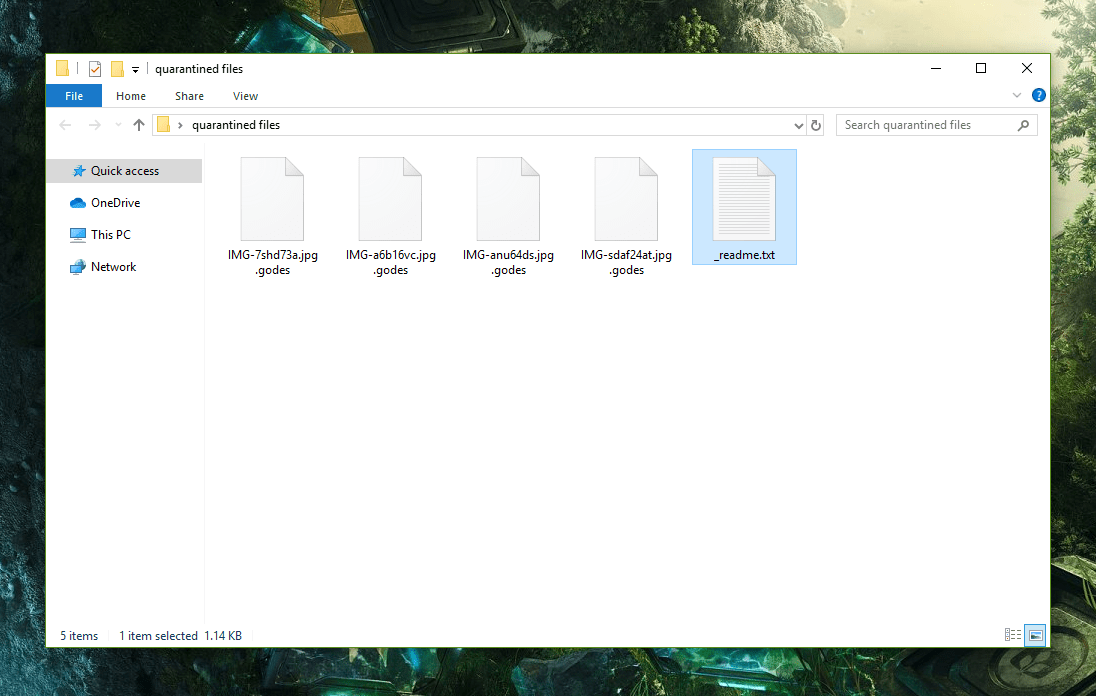
This page aims to help you remove .Godes Virus Ransomware for free. Our instructions also cover how any .Godes file can be recovered.
The Godes Virus
.Godes is a cryptovirus that operates in this same way – once it makes the files in your computer inaccessible, it tells you that you are supposed to issue a payment to the hackers behind the infection. And, in order to remain anonymous, the criminals usually want the payment in BitCoin or in another similar type of cyber currency – those currencies are very difficult to trace and any payments made with them will guarantee that the receivers’ true identities do not get revealed. This, of course, puts you in a particularly unpleasant spot – if you don’t pay, your files will stay locked, however, if you do pay, there is no guarantee that the criminals will actually help you with the decryption of your files. This is why we recommend that you try a third option – remove .Godes and then try to restore the files yourself, using the methods that we have included in the second section of our .Godes Virus removal guide. To remove the cryptovirus from your system, use the instructions that you will find below and if you face difficulties, know that the recommended removal tool could help you with the elimination of the malware. And after you are done with the removal of the malware, go to our file recovery section and try some of the suggestions there – they may help you recover some of the lost files (though no guarantees can be given).
Can a godes file be decrypted?
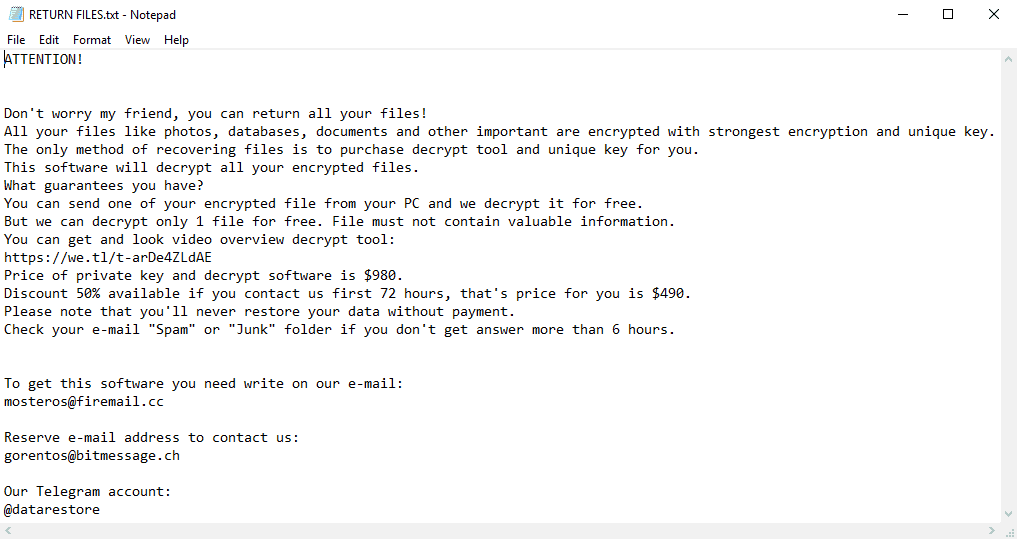
The Ransomware infections, such as .Godes, .Lokas or .Actin that lock up your files and tell you that the only way to get them back is through a ransom payment are among the most unpleasant malware programs that a user can encounter on the Internet. Although they do not directly threaten the health of the system or the files that you have, through the complex encryption algorithm that they use, they are able to make all of your data totally inaccessible. Usually, the only thing that can make an encrypted file accessible again is the corresponding decryption key. Of course, if you have backups of your files on other devices or on cloud storages, removing the virus is all you’d need to do, as you’d be able to restore your files from the backups instead of trying to restore the ones that are in your computer. However, as it turns out, most users do not really have extensive backups of the files that they consider important. Most people have some valuable data in their computers but they do not have backup copies of it, which means that a Ransomware cryptovirus attack could be particularly problematic. This is how many customers get their work or education-related files locked up and once such valuable data becomes inaccessible, the targeted victim would surely be willing to give quite a lot in order to get their files back. This is, of course, what the hackers are counting on – once they have your data under their virus’ encryption, they offer you to pay for your files. This type of viruses even display notifications on the users’ screens, in which notifications they provide ransom-payment instructions that the user is supposed to comply to if they want to retrieve the sealed files.
SUMMARY:
Remove .Godes Virus Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Reply