This page aims to help you remove [email protected] for free. Our instructions also cover how any [email protected] file can be recovered.
In case you landed on this page because your files have been encrypted by [email protected] then stay with us because here we’ll help you clean up your system from this dangerous Ransomware. Dealing with this type of malware can be very challenging but, in the next lines, you will find some helpful instructions on how to remove it, as well as some good tips for preventing future infections and better protecting your system.
The [email protected] virus
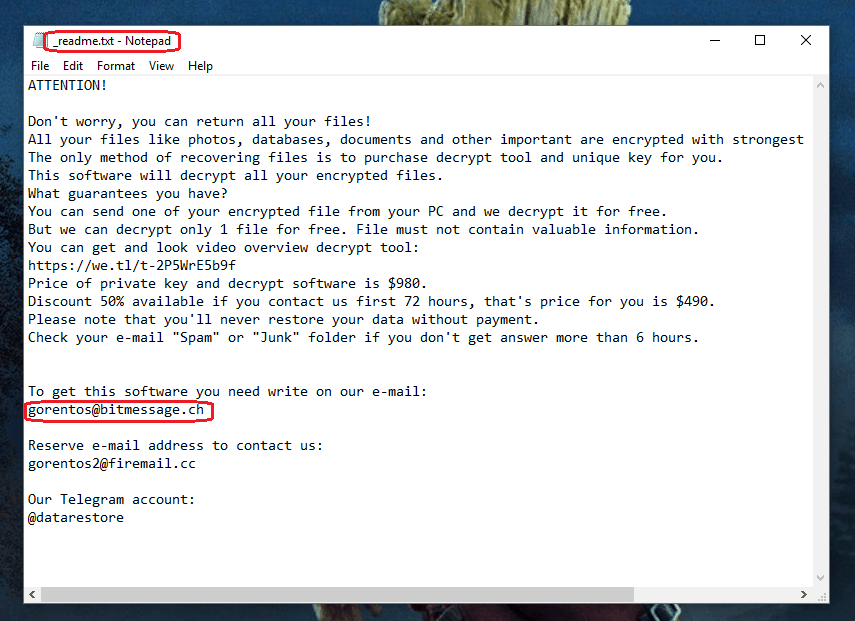
The message displayed by the [email protected] Virus.
[email protected] is created as a typical Ransomware cryptovirus with the sole purpose of infecting as many unsuspecting web users as possible and applying a strong encryption to their most valuable files. In order to attack as many computers as possible, this threat spreads through various transmitters, including email spam messages, malicious attachments, infected files, fake ads or compromised software installers. Trojan horses, torrents, sketchy content, infected programs, and seemingly harmless files or commercials could also be potential carriers of an infection like [email protected]. The hackers behind this form of malware rely a lot on the effect of surprise in order to shock their victims. Therefore, they use different methods of social intelligence to mask the harmful payload and hide it well. Therefore, detecting and removing the danger is really difficult without a reliable security program. A single careless click is usually enough to get you infected.
The Ransomware tries to remain unnoticed while on the system and quietly encrypts all the information found in the machine with the help of a complex encryption algorithm. The targeted data usually involves photos, videos, documents, archives, music, films and even files of the system. Once encrypted, the files become unreadable and impossible to open. A name change and a file extension change may also be applied. Upon completion of the process, the malware reveals itself on the victim’s screen with a ransom note. The victims are asked to pay a certain amount of money (usually in Bitcoins) for a decryption key if they want to access their information again.
The [email protected] file encryption
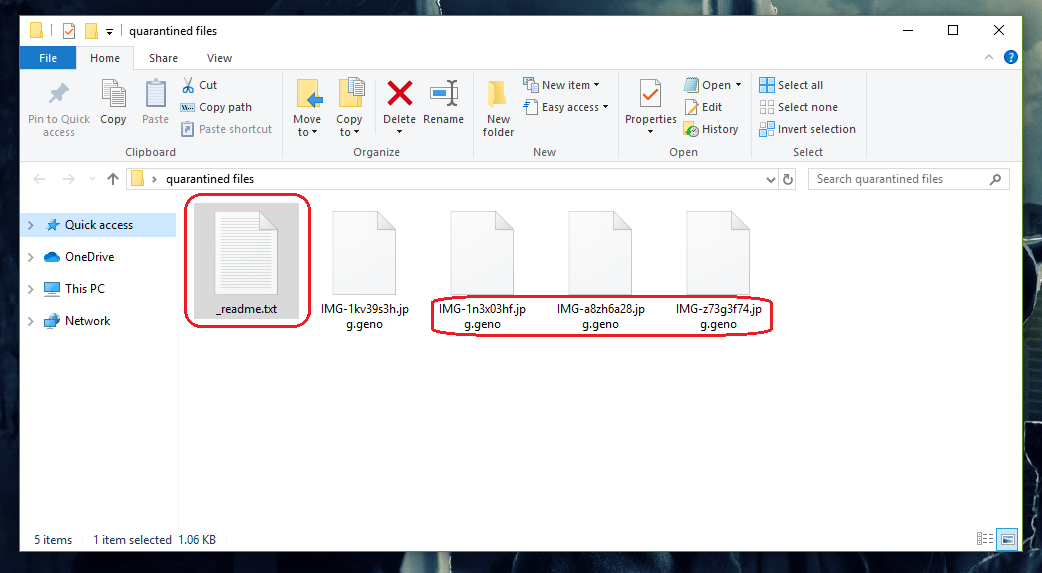
A different strain of encryption of the [email protected] Virus.
Keep in mind, though, that fulfilling the ransom demands of the criminals does not guarantee that your files will get back to normal. There’s a great chance you won’t get a decryption key at all. If, by any chance, the criminals do send you one, there is still a chance that your files may still not be decrypted successfully. At the same time, a computer compromised by Ransomware, you are more susceptible to all kinds of threats.
That’s why we recommend that you focus on how to remove the infection and clean your computer if you want to be able to use it in the future. In the event that you have external backup copies of your files, you can safely connect them to the clean machine and recover the encrypted information. If you don’t have backups, however, don’t despair. There are still some things you could do. For instance, take a look at our free file-recovery suggestions in the guide below or check out our list of free decryptors. If nothing works, you still may want to consider contacting a security professional rather than the criminals and seek legal assistance.
SUMMARY:
| Name | [email protected] |
| Type | Ransomware |
| Detection Tool |
[email protected] Ransomware Virus Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

file me not .moka not remove
How do I recover my files?
text.moka.
.text ?
it’s too bad nearly my 450GB files are converted to .bora file i can’t recover it… what can i do it is very horrible
if hacker come instead of me i will kill him
Friends please tell any Solution for recover my Files
my all files end with .domn
and i dont have a back up ???
any help ?
Hi Mohamed! Firstly, we advise you to complete the guide from the current page in order to remove the malware and clean your PC.For now, the only other alternative to paying the ransom and best thing to do is back those files up onto another drive for safe keeping until a decrypter becomes available.