The Gummy Browsers
With the use of a new attack, hackers are now able to collect and alter the digital fingerprints of browsers. Users’ browser fingerprinting information might be exploited by attackers to impersonate the victims without their awareness, thereby violating their privacy.
According to researchers at Texas A&M University, the attack mechanism has been nicknamed “Gummy Browsers“, and is similar to a nearly two decades old technique known as “Gummy Fingers”, which mimics fingerprint biometrics.
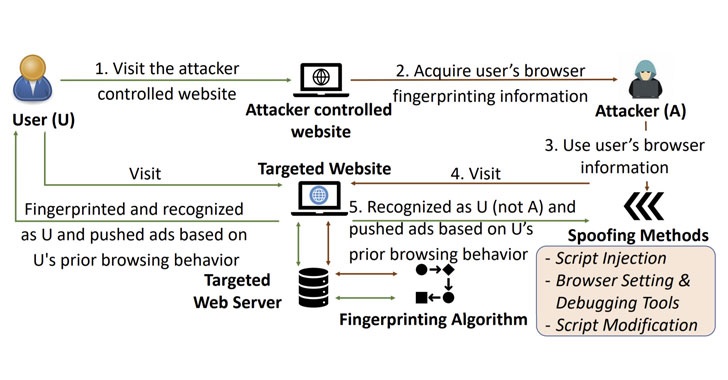
It’s a simple idea: The hacker tricks the user to connect to his website (or a well-known site under his control) and then transparently gathers information from the user for fingerprinting purposes just as any fingerprinting website would normally obtains similar information. Once that’s done, the attacker operates a browser on his own system to reproduce and send the same fingerprinting information while connecting to a website, deceiving the latter into believing that the user is the one requesting the service.
The idea of this browser fingerprinting tracking technique, which is also referred to as machine fingerprinting, is to allow the web users to be uniquely identified on the internet by gathering data about the software and hardware that they use (such as the browser used, language, timezone, etc.), and the behavioral characteristics when interacting with the device’s web browser.
If the website serves targeted ads based solely on browser fingerprints, a remote attacker may be able to profile any target of interest for an extended period of time by changing their fingerprints to match the ones he likes. Both the user and the website would be completely unaware of the attack.
In case of such an attack, the user would see advertisement identical to those of the victim that the attacker has impersonated. What is more, by taking advantage of the fact that the server treats the attacker’s browser as the victim’s, a malicious actor may be able to exploit sensitive information about the user (such as gender, age, health condition, interests, and income) and create a customized behavioral profile.
Based on results from testing, it seems that the attack can effectively fool digital fingerprinting systems into thinking the faked prints are authentic ones. As a result of that, ad privacy may be violated and defense systems used to verify users and identify fraud may be bypassed.
Considering that browser fingerprinting is becoming more commonly used in the real world, the effect of Gummy Browsers on online security and privacy of users may be serious and long-lasting, the researchers conclude. The analysis raises the issue of whether browser fingerprinting is safe to implement on a big scale in light of these types of attacks.

Leave a Reply