*Gyew is a variant of Stop/DJVU. Source of claim SH can remove it.
Gyew File
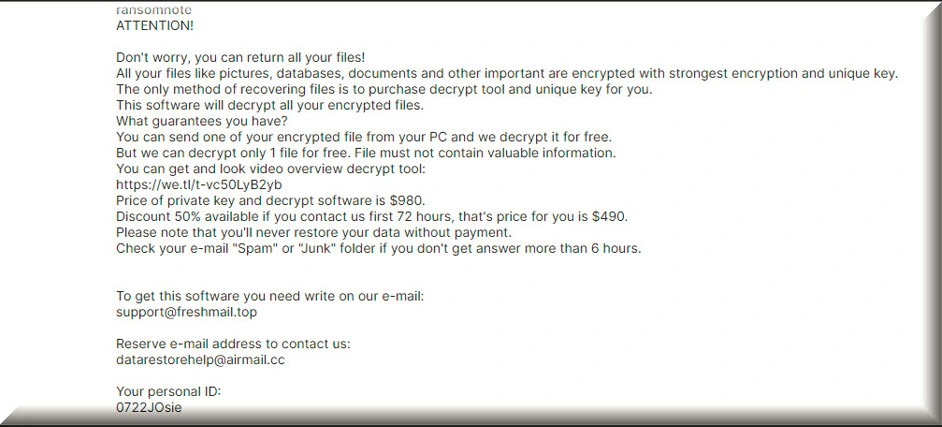
Picture this: you attempt to open a file on your system, only to be met with an error message. You might notice a strange Gyew file that your system just doesn’t seem to recognize. Sounds scary, right? On top of that, the mysterious Gyew file is unable to be opened by standard software, and requires a specific decryption key to unlock. If you’re faced with this experience on your computer, we are sorry to say, but it looks like you’ve probably been hit by a ransomware attack. Ransomware is a piece of software, created by cybercriminals to lock you out of your own files, and then demand a ransom for the access key. If you’re unable to meet their demands, you risk losing access to your files forever.
How to decrypt Gyew ransomware files?
In technical terms, it is possible to decrypt various types of ransomware, which is certainly encouraging. However, it’s crucial to note that decrypting Gyew ransomware requires specific decryptor tools tailored to each type of ransomware. One cannot use a single decryptor tool for all types of ransomware, as each variant possesses unique characteristics and coding.
How to remove Gyew ransomware virus and restore the files?
Dealing with the Gyew ransomware virus can be tough, but here’s what you can do to handle it. First, disconnect the infected device from the network to prevent further spread. Then, find out which specific ransomware you’re dealing with so you can explore potential recovery methods. Report the incident to the authorities, and use reliable antivirus software to remove the ransomware from your system. If you have backups, restore your files from a clean backup created before the infection. Check for decryption tools online that may help, and consider seeking professional help if needed.
Gyew Virus
So now you might be asking, “how on earth did this ransomware get onto my system?” Well, that’s the work of what we call the Gyew virus. This sneaky malware is a constantly evolving threat that is finding new ways to worm its way into your system. The most common route it takes is through spam email attachments. When you unsuspectingly download these attachments, you activate the ransomware virus, which then gets to work and encrypt your files. However, it doesn’t stop at emails. The cybercriminals behind Gyew virus also use malicious downloads, fraudulent ads, and chat messages to spread the ransomware. One popular method is hiding an executable file in a zip folder or a Microsoft Office document’s macros.
Gyew
At this point, you might feel a bit overwhelmed, but don’t worry! There are steps you can take to protect yourself against Gyew. The first line of defense is always awareness; understanding the risks of clicking on dubious links and downloading suspicious attachments can go a long way. Also, having a robust security software in place and ensuring that all your software is regularly updated can drastically reduce your risk of being victimized. In this fast-paced digital world, the bad guys are always looking for loopholes, so staying on top of your software updates is crucial. Lastly, one of the best ways to minimize the effect of a Gyew ransomware attack is to regularly backup your data on an external drive or a cloud storage system. This way, even if your files get encrypted, you’ll still have access to your important data.
.Gyew
The .Gyew ransomware file extension is the telltale sign that your files have been encrypted. Spotting the encryption process can be quite a task, as it generally happens without any noticeable symptoms. If you’ve been unfortunate enough to be hit by a .Gyew or Gycc, Eqza ransomware, it’s crucial to stay calm and not rush into paying the ransom. Why? Well, there’s a good chance you won’t receive the decryption key even after paying the ransom, as these cybercriminals aren’t exactly trustworthy. Instead, we advise trying out our free file recovery suggestions and using our expert-recommended ransomware removal tool.
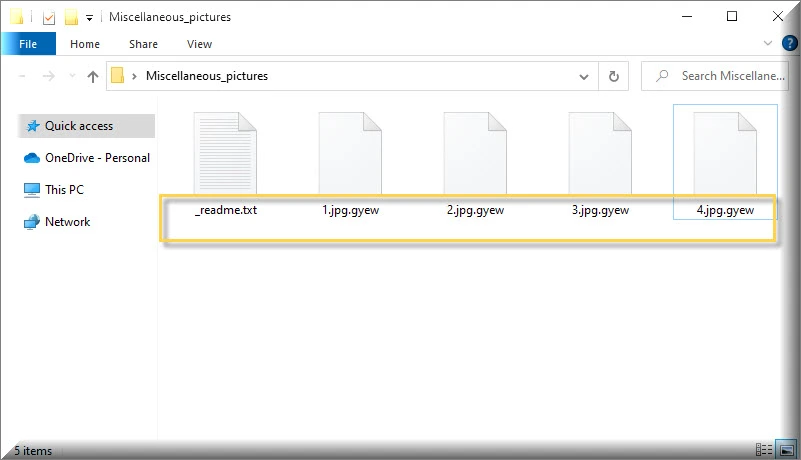
Gyew Extension
When the ransomware infects a system, it appends the Gyew extension to the original file extension, creating a new file name that includes both extensions. For example, a file named “file.docx” would be renamed as “file.docx.Gyew” after encryption. This alteration effectively separates the encrypted files from their original formats, making them inaccessible to users without the decryption key or appropriate tools. Users can easily identify which files have fallen victim to the ransomware attack by looking for the Gyew extension,. This can be helpful in assessing the extent of the damage and determining which files need to be prioritized for recovery or decryption efforts. However, it’s important to note that additional analysis and investigation are required to gather more information and explore potential decryption options.
Gyew Ransomware
Gyew ransomware employs various sophisticated techniques to infiltrate systems and exploit vulnerabilities. Often, it can spread through malicious websites or compromised online advertisements, known as malvertising, which can infect systems when users unknowingly click on infected links or ads. Another avenue for Gyew ransomware attacks is through exploit kits, which are malicious software bundles that target vulnerabilities in outdated software or operating systems. These exploit kits can automatically exploit security flaws, allowing ransomware to be installed without any user interaction. To protect against such infections, it’s crucial to maintain up-to-date antivirus software, regularly backup important data, exercise caution when opening email attachments or clicking on suspicious links, and keep all software and operating systems patched with the latest security updates.
What is Gyew File?
Simply put, a Gyew file is a regular file on your system (think documents, images, videos, databases) that’s been encrypted by ransomware. These files can no longer be accessed without a specific decryption key. You’ll usually be able to identify them by their unique file extension or altered filename. When it comes to decrypting a Gyew file, in some fortunate instances, security researchers or law enforcement agencies are able to obtain decryption keys or develop tools that can help victims recover their files without paying the ransom. These tools are often specific to certain ransomware variants and may not work for all types of encryption. Therefore, it’s essential to stay updated with the latest information from reputable sources, to see if any solutions have become available.
SUMMARY:
| Name | Gyew |
| Type | Ransomware |
| Detection Tool |
*Gyew is a variant of Stop/DJVU. Source of claim SH can remove it.
Gyew Ransomware Removal

As a first step in this guide, we recommend that you bookmark this page in your browser’s Favorites. This will help you to quickly reload it after the system restart that follows.
The next step is to perform a Safe Mode Restart on the compromised machine (see this link for detailed instructions on this). When you start your computer in Safe Mode, only the most essential programs and processes are launched, allowing you to detect any Gyew-related processes more easily.
Once in Safe Mode, type msconfig in the Windows search field and press Enter. After you’ve completed this, you’ll be able to see the System Configuration screen. Go to the Startup tab to check whether any of the items that start up when you start your computer are linked to the infection.

Do some online research if there are entries on your computer that have random names or Unknown Manufacturers, or anything else that cannot be related to any trusted programs you regularly use. Checking off the applicable checkbox box for them is the best way to disable them if you have enough solid information to do so.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Gyew is a variant of Stop/DJVU. Source of claim SH can remove it.
In the next step, look for suspicious processes that are running in the background of your system. This may be done by pressing CTRL + SHIFT + ESC to open the Task Manager window. The Processes Tab is where you’ll go to check if anything fishy is going on in the background. You can see how much memory and CPU are being used by each process and decide if this is a normal activity or not. Also, look at the names of the processes for something random or unusual. Right-click on any suspicious process and select Open File Location from the pop-up menu, just as shown below:

You can scan the files stored in the File Location folder for malicious code using the virus scanner provided below.

If the scan results indicate that the files are dangerous, go to the Processes tab, right-click on the process that is related to them and select End Process. After you have done that, delete the dangerous files from their location.

Open a Run command window by pressing the Windows key and R on the keyboard. Then, paste the following line in it:
notepad %windir%/system32/Drivers/etc/hosts
Click OK to run the command and open the Hosts file. You should be able to locate Localhost in the Hosts file that displays on your screen. A number of odd-looking IP addresses under Localhost at the bottom of your file may be an indication that your machine has been hacked. Look at the sample image below.

If you notice anything strange in your Host file, please leave a comment below this post, and we’ll tell you what to do and how to fix any problems we identify with the IPs.

*Gyew is a variant of Stop/DJVU. Source of claim SH can remove it.
When a computer is hacked, malicious items can be introduced to the registry without the victim’s permission or knowledge. Ransomware threats like Gyew are difficult to remove because of this – they tend to add helper entries that make it harder for the victim to get rid of the infection. In the following steps, however, you’ll learn how to look for files in your computer’s registry that need to be deleted.
Using the Windows search box, first type regedit and press Enter on the keyboard. The Registry Editor will be displayed on your screen. Next, CTRL and F can be used to look for entries relating to the infection. To do that, in the Find box that appears, type the ransomware’s name and click Find Next.
Registry file and directory deletions unrelated to Gyew may damage your operating system and the software installed on it. To avoid causing any harm to your computer, it is best to use a professional removal tool, such as the one on this website. When it comes to identifying and eradicating malware from critical areas of your computer, such as the registry, this application excels.
Aside from cleaning the registry, it is also a good idea to enter each of the lines below in the Windows search field and check them for any Gyew-related traces:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
In each place, look for files and folders with odd names or a date of creation near the date of the ransomware attack. If you can’t decide, use a powerful scanner and run a thorough check to help you decide whether or not something should be eliminated.
In the Temp folder, you can select and delete all the files that are stored there. This will remove any ransomware-created temporary files from your computer.

How to Decrypt Gyew files
Ransomware is one of the most difficult types of malware to recover encrypted data from, therefore you may need to rely on different methods to decode parts of your data. In order to decide on the best method for recovering your files, you must first determine which variant of ransomware has infected your system. Checking on the encrypted files’ extensions can give you this information quickly and easily.
New Djvu ransomware
If you come across files with the .Gyew extension, it means that your computer has been impacted by the latest version of Djvu ransomware known as STOP Djvu. However, there is some good news to consider. Presently, there is a possibility to decrypt files that have been encrypted by this particular variant, but it is important to note that this decryption method only works for files that have been encoded using an offline key. To gain further insights and access a file-decryption program that can assist in recovering your files, please click on the provided link.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
To obtain the decryptor STOPDjvu.exe, simply click on the “Download” button available in the provided link. Once the file is downloaded, right-click on it and select the “Run as Administrator” option, then confirm by clicking “Yes”. Take a moment to review the license agreement and carefully follow the instructions provided on how to utilize the tool. After completing these steps, you can initiate the decryption process for your data. It’s important to note that if your files were encrypted using unknown offline keys or online encryption methods, this tool may not be able to successfully decrypt them.
Before attempting any data recovery techniques, you must first remove the ransomware from the infected computer. Professional anti-virus software, such as the one on this site, can help get rid of Gyew and other viruses. For additional assistance, you can make use of the free online virus scanner on this page. The comments section is also a good place to ask us questions and share your experience. We would be glad to know if we have helped you.

Dear
Unfortunately, all files encrypted to .gyew and a problem for me
please my be help to decrypt of file
Hi gholam reza dashab,
Did you go through the whole guide on this page?