.Hard
.Hard is a new representative of the malicious software category called Ransomware. The purpose of .Hard is to secretly encrypt the victim’s data and demand a ransom “fee” to decrypt it.
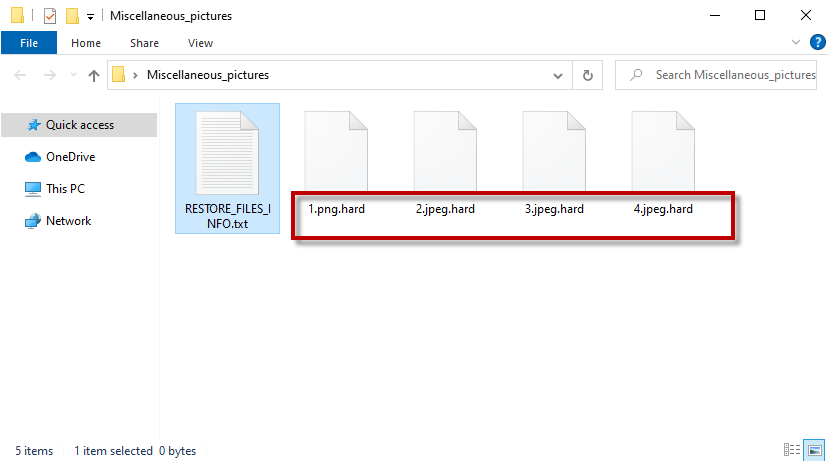
The .Hard file ransomware virus
Today’s article is dedicated to .Hard – one of the latest Ransomware representative. Like most other malicious programs of this kind, this threat encrypts the files of the users and then puts a threatening ransom note on their monitor to scare them into paying a ransom. Since you are on this page, however, we assume that you are don’t particularly like the idea of paying a ransom to the criminals behind .Hard. That’s why, in the next paragraphs, we’ll try to help you avoid the ransom payment by providing you with alternative file-recovery suggestions and instructions on how to remove the Ransomware.
The .Hard virus
The .Hard virus is a stealthy ransomware-based infection. In most cases, the .Hard virus will sneak inside the system without any symptoms and encrypt user files without further notice.
As noted, the Ransomware programs use file encryption as their weapon. The irony here is that the file encryption is a popular method of data protection which has an implementation in many sectors where highly important data needs to be kept safe and secure from unauthorized access. Under normal circumstances, the encrypted information is accessible with a special decryption key which only the owner of the information has. Without encryption, you wouldn’t be able to safely shop online or transfer money from and to your accounts. Sadly, the Ransomware attackers have found a way to use this data protection mechanism to block access to your files and blackmail you. They just lock your information with a complex algorithm and don’t give you the decryption key for it. This is a simple, yet very effective blackmailing scheme, and may web users fall victims to it.
The .Hard file encryption
The .Hard file encryption is a special code that keeps your files inaccessible. Decrypting the .Hard file encryption is only possible with a unique decryption key which is in the hands of the hackers who demand a ransom payment for it.
You may have noticed that the hackers have requested their ransom in bitcoins. This is a very popular online cryptocurrency because the bitcoins are very hard to trace and this ensures that the hackers are not identified. So, anyone who pays them actually inadvertently helps them keep their anonymity further and funds their criminal scheme. At the same time, there is absolutely no guarantee that the victims will obtain the decryption key that the hackers promise to send after the money has been transferred. In fact, it is quite common for the victims of Ransomware to be left with nothing but a lighter wallet and heavily encrypted files at the end.
So, in our view, risking your hard-earned money is not the best thing you could do. Of course, it is up to you to choose how to act but we do encourage you to try all other alternative options and maybe consider the ransom payment only in case everything else fails.
Having the .Hard virus removed, however, is the first and most important thing you should do as this will ensure that no further file encryption happens in your system. If you don’t know how to do that, in the guide below we’ve prepared a set of detailed instructions that can help you. You will also find a section with instructions that can assist you with potentially restoring some of your files. So, check them out and see if they can help you avoid the ransom payment. And from now on make sure to keep backups of your most important files on separate drives or a on clouds as this is the best preventive measure against accidental data loss.
SUMMARY:
| Name | .Hard |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
| Data Recovery Tool | Not Available |
| Detection Tool |
Remove .Hard Ransomware
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.
![]()
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!
![]()
How to Decrypt .Hard files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment