Harma
This page aims to help you remove Harma Virus for free. Our instructions also cover how any .Harma file can be recovered.
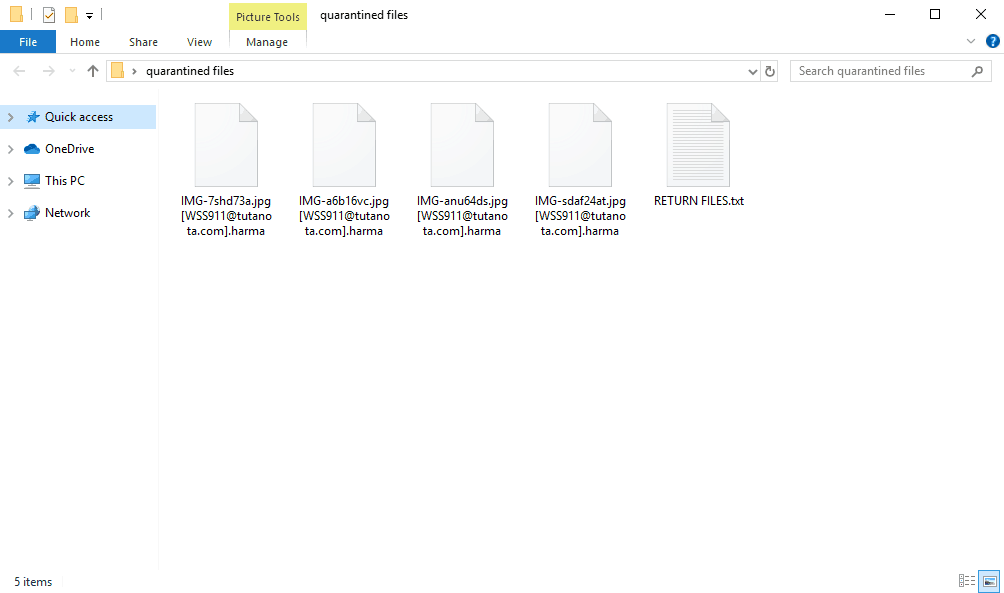
The Harma Ransomware will stealthily encrypt your files with the .harma extension.
The Harma Virus
The Harma virus is a cryptovirus that seeks to encrypt data that is stored on the infected computer. After the attack, the Harma virus will demand a ransom to unlock the encrypted files.
As soon as the Harma Virus is done with the encryption you will find a RETURN FILES.txt with instructions for paying ransom for your files.
All FILES ENCRYPTED “RSA1024”
All YOUR FILES HAVE BEEN ENCRYPTED!!! IF YOU WANT TO RESTORE THEM, WRITE US TO THE E-MAIL [email protected]
IN THE LETTER WRITE YOUR ID, [REDACTED]
IF YOU ARE NOT ANSWERED, WRITE TO EMAIL: [email protected]
YOUR SECRET KEY WILL BE STORED ON A SERVER 7 DAYS, AFTER 7 DAYS IT MAY BE OVERWRITTEN BY OTHER KEYS, DON’T PULL TIME, WAITING YOUR EMAIL
FREE DECRYPTION FOR PROOF
You can send us up to 1 file for free decryption. The total size of files must be less than 1Mb (non archived), and files should not contain valuable information. (databases,backups, large excel sheets, etc.)
DECRYPTION PROCESS:
When you make sure of decryption possibility transfer the money to our bitcoin wallet. As soon as we receive the money we will send you:
1. Decryption program.
2. Detailed instruction for decryption.
3. And individual keys for decrypting your files.
!WARNING!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
So, let’s take a step-by-step look at what should be done in case of a Ransomware attack:
- Isolate the contaminated machine – it is very important that the contaminated machine is isolated immediately to avoid contaminating other machines or connected devices. To do that, unplug the connected devices and the local network cable immediately.
- Install an antivirus or a professional removal tool and run a full scan with it. If a virus is found during the scan, remove it immediately – you can also use the manual steps from the guide below.
- Restore your files from a backup – if you have a backup of the encrypted files, now is the time to use it and thus avoid any ransom payment. It is very important that, if your backup is on an external device, you do not connect it directly to the affected machine. At least, not before you are sure that you have removed Harma Virus completely. For extra safety, copy the backup files to another device and then connect the backup to the machine. If you have no backup, you can try the methods we have explained in the recovery section of the removal guide.
The Harma file extension
If a Ransomware cryptovirus such as Harma, .Cezor or .Lokas has sneaked inside your system and has placed its complex encryption on all of your files, you probably are desperate to remove the infection and regain access to your most valuable data. Dealing with a malware of this type, however, may not be very easy. That’s why, below, we have prepared a special removal guide with detailed instructions on how to handle the malware and how to effectively remove it without causing more damage. Don’t worry if you are not an expert in computers because there is also a professional removal tool for automatic assistance, which can help you detect and delete the harmful files in only a few clicks. Before you scroll down to the actual steps, however, let us tell you a few more words about Harma and the Ransomware cryptoviruses in general.
A Ransomware cryptovirus attack can affect you in the following ways:
- Loss of important information: a threat like Harma Ransomware can block the access to your most important files by placing a complex encryption on all of them. Because the files are encrypted, the attacked user cannot open them without the application of a special decryption key. Unfortunately, that key is kept in a server which is controlled by the hackers who stay behind the infection, and they ask you to pay a certain amount of money in the form of a ransom to send it to you. The problem is that even if you pay the ransom, there is no guarantee that the criminals will give you the key and that you will have your files decrypted. This, in turn, leads to another risk of losing your money in vain.
- Financial loss: Imagine that you don’t get the decryption key? Or that it doesn’t work properly? In this scenario, not only would your money be gone for good, but you will still be unable to recover the encrypted information.
This, however, doesn’t have to be the case if you don’t fall for the blackmailing scheme and do everything possible to avoid the ransom payment. That’s why we encourage you to take a series of measures as soon as you detect an attack from Harma Virus. These measures are important to ensure that no other machine in your network or other connected devices get infected, and may increase the chances of recovery.
SUMMARY:
| Name | Harma |
| Type | Ransomware |
| Detection Tool |
Remove Harma Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible). You can find the removal guide here.

Leave a Comment