.Hese
.Hese is a catch-all term for a ransomware of the STOP DJVU ransomware strain. .Hese will therefore reveal itself only when extensions with it are added to your files.
This page aims to help you remove the Hese Virus for free. Our instructions also cover how any .Hese file can be recovered.
Hese is one of the latest representatives of the growing list of Ransomware infections that are spreading around the web. This one, along with other similar infections like Gero, Carote, uses a special file-encrypting algorithm to block the access to the victim’s personal files and ask for a ransom payment in exchange for their decryption. This simple blackmailing scheme is a very lucrative money-extortion model for the cyber criminals who stay behind those threats. According to the information available, it generates them enormous amounts of money sent from the victims, who suddenly get greeted by a scary ransom-demanding notification on their computer.
If you have been among the unlucky web users who have been attacked by Hese, on this page, you will find a step-by-step Removal Guide and a professional removal tool which may help you remove the nasty malware from your system. There is also a section with file-recovery suggestions which do not involve giving money to the hackers behind Hese. We recommend you check it out once you clean your computer and see if you can avoid the ransom payment.
The .Hese Virus
The Hese virus is a ransomware of the DJVU variety – currently the most prominent ransomware type. The Hese virus in particular rose together with .Gero and it is possible for users to be infected by both at the same time.
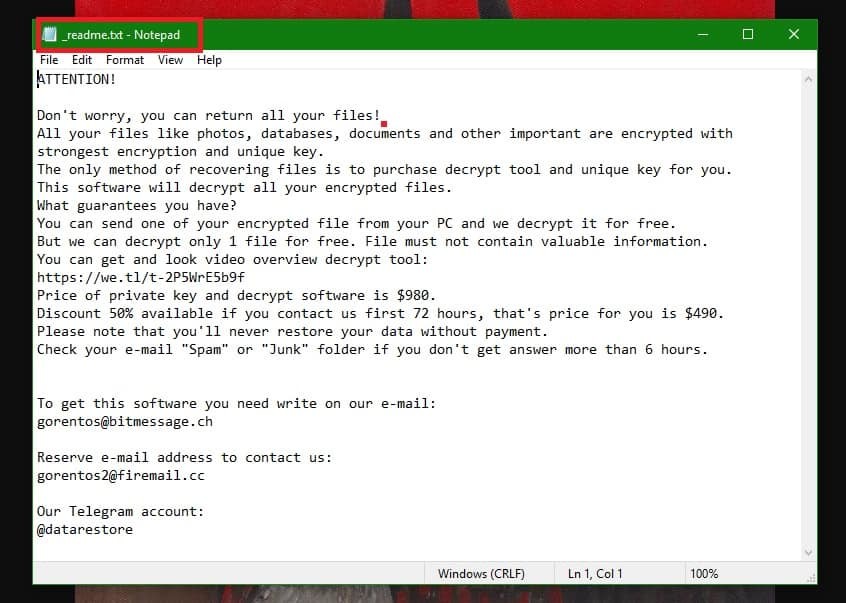
The Hese Virus will leave a _readme.txt file with instructions
The modus operandi of Ransomware is actually relatively simple: the malware finds a way to infiltrate a victim’s computer (either via spam emails, malicious attachments, fake ads, misleading links, etc.), and then applies an encryption code to its files. After that, the malware informs the users that, in order to get the files back, they would need to pay a ransom. The cybercriminals just have to wait for the shocked user to despair and finally make the payment. In most of the cases, they use fear and frustration as the main weapons, and threaten the victims with deadlines, ultimatums, and the total loss of the locked data, in order to make them pay faster. Typically, they offer to send a special decryption key to those who agree to pay as soon as possible. Security experts, however, warn that there is a significant number of cases where the victims have never received such a key even after they have paid the ransom. Therefore, they don’t advise the web users to risk their money by sponsoring the hackers and their criminal scheme, and advise them to seek legitimate methods of dealing with the infection.
The .Hese file extension
The .Hese file extension is NOT a normal extension, but rather an encryption. The main difference is that a .Hese file cannot be opened by normal means. It requires a key to unlock the files and remove .Hese.
Ransomware evolves quickly and its creators apply different social engineering techniques and psychology tricks in order to improve their distribution methods and reach as many victims as possible. Many people who get infected with Ransomware become victims of phishing campaigns or malicious spam distribution. The users typically receive emails that appear legitimate and mimic the messages of some popular company or institution. Many take the bait and access the link or the attachment in those emails, which contaminates them with malware. That’s why, in order to avoid such an infection, it is best to keep away from spam and shady messages and have a reliable security program installed. Also, it is a good idea to keep regular backup copies of your most important files somewhere on an external drive or on a cloud so you can easily access them in case of a sudden encryption of the files on your computer.
SUMMARY:
| Name | Hese |
| Type | Ransomware |
| Detection Tool |
Hese Virus Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

127.0.0.1 space1.adminpressure.space
127.0.0.1 trackpressure.website
127.0.0.1 htagzdownload.pw
127.0.0.1 360devtraking.website
127.0.0.1 room1.360dev.info
127.0.0.1 djapp.info
127.0.0.1 sharefolder.online
127.0.0.1 telechargini.com
127.0.0.1 fffffk.xyz
127.0.0.1 smarttrackk.xyz
0.0.0.0 telemetry.malwarebytes.com
Delete these IPs from your Hosts file, and save the changes.
102.54.94.97 rhino.acme.com # source server
38.25.63.10 x.acme.com # x client host
localhost name resolution is handled within DNS itself.
# 127.0.0.1 localhost
# ::1 localhost
You do not need to do anything about those IP addresses – they are okay.
hello guys,
my computr was affected by .hese virus vrus. I scanned the computer with spyhunter and actually i dont know restore my files. I will be pleased to get your help.
thank you
yes sir i also having the same problem pl help me out to restore the file in the original association as it was
Hello. After using the spyhunter, for recovery the information, need to use the recovery software??
And spyhunter deleted oll of virus and we be sure our system is clean??
The system should be clean, but this anti-malware program isn’t a decryptor – it doesn’t decrypt Ransomware. For suggestions on what you can try to recover some of your files, try the instructions from ouy How to Decrypt Ransomware article.