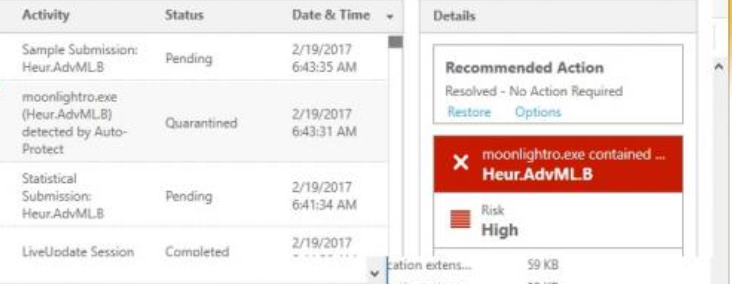
Heur.advml.b
Trojans, like Heur.advml.b, are very dangerous programs, which can be used for achieving almost any malicious goal. The cyber criminals often rely on such programs to perform different types of cyber crimes without the knowledge of the victims. Unfortunately, new and more sophisticated variants of Trojan horse infections are getting created often and Heur.advml.b is one of them.
On this page, we are going to discuss its malicious capabilities and the most effective ways to remove it from your system. Stay with us if you are looking for reliable removal instructions or a trusted malware removal tool that can deal with Heur.advml.b without risk for your system.
What is Heur.advml.b?
With an advanced Trojan like Heur.advml.b, the cyber criminals can achieve a lot. The malware can be programmed to launch a specific attack, to activate certain malicious process or create vulnerabilities for more malicious viruses such as Ransomware to take over the machine. With Heur.advml.b in your system, you should basically be prepared for the worst. It may turn your machine into a bot, which can be remotely controlled by the hackers.
The crooks may decide to spread spam or launch targeted virus attacks by using your computer’s resources. Your own machine may also get secretly compromised by other destructive pieces of software thanks to the background activities of the Trojan. As a result, you may end up with a computer, totally controlled by anonymous criminals, which might have access to all of your personal or professional information that is stored in the system. What is more, the crooks may activate tracking processes, which can monitor all of your activities by recording your keystrokes or watching you through your own camera so that they can later blackmail you or take advantage of your details by hijacking your profiles and accounts. And this is just a small portion of what the crooks might be able to do with the help of a Trojan like Heur.advml.b on your machine. So, the best you could do to protect yourself is to remove the infection as soon as possible.
Heur.advml.b – a new Trojan threat which is ready to damage your computer in a number of ways!
One thing you should know about Trojan horse infections is that they are the most common and some of the most malicious Internet threats you may encounter. Such pieces of software have numerous sources and very different ways of harming your PC. A virus such as Heur.advml.b, for example, contains very advanced malicious scripts, which can activate and run different criminal tasks. Unfortunately, you may not be able to notice the presence of the infection inside the system, because it has the ability to remain hidden and perform its criminal activities in stealth. Heur.advml.b normally exploits a certain vulnerability inside the PC. Such vulnerability could be an outdated software or the absence of a proper antivirus tool. The Trojan generally tries to hide all of its traces and remain hidden for as long as possible before a major system damage or dysfunction reveals the consequences of its criminal activities. Sadly, by the time you spot the infection, a lot of damage might have already been caused, which is why this malware group is considered to be one of the worst ones that you could come across.
What are the potential transmitters which can deliver Heur.advml.b inside your PC?
The possible sources of Trojans could be numerous. These malicious pieces of software typically use camouflage to mislead the web users and disguise their real nature and intentions. That’s why, oftentimes, the Trojans can be found in many different web locations. The hackers normally use harmless looking transmitters such as ads, pop-ups messages, social shares, attractive looking offers, free download links, and pages that provide free streaming. Torrent platforms, freeware, and shareware sites may also be places where threats like Heur.advml.b could lurk. However, the most common and effective way of distribution is the email spam. Disguised as a message from an unknown sender or from a certain authority, the Trojan can compromise your system the moment you open the message. The malicious payload is often delivered via attachment, which could be a PDF file, an .exe file, an archive or an image. To stay safe, we advise you to not click on anything, which comes from non-reputed sources and avoid interaction with popping messages, ads, links, software downloaders or anything that looks sketchy.
If your system has been infected with Heur.advml.b, you should take immediate actions to remove it with the help of the instructions in the Removal Guide below. A scan with the professional Heur.advml.b removal tool is also much recommended for a fast and risk-free removal process.
SUMMARY:
Heur.advml.b Trojan Virus Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android , iPhone

Leave a Reply