This page aims to help you remove Hi.fo “Virus”. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
If something unexplained and weird has been disturbing your browsing experience recently and you have found out its name is Hi.fo “Virus”. This article has been written with the basic purpose to answer all your question about the already mentioned piece of software.
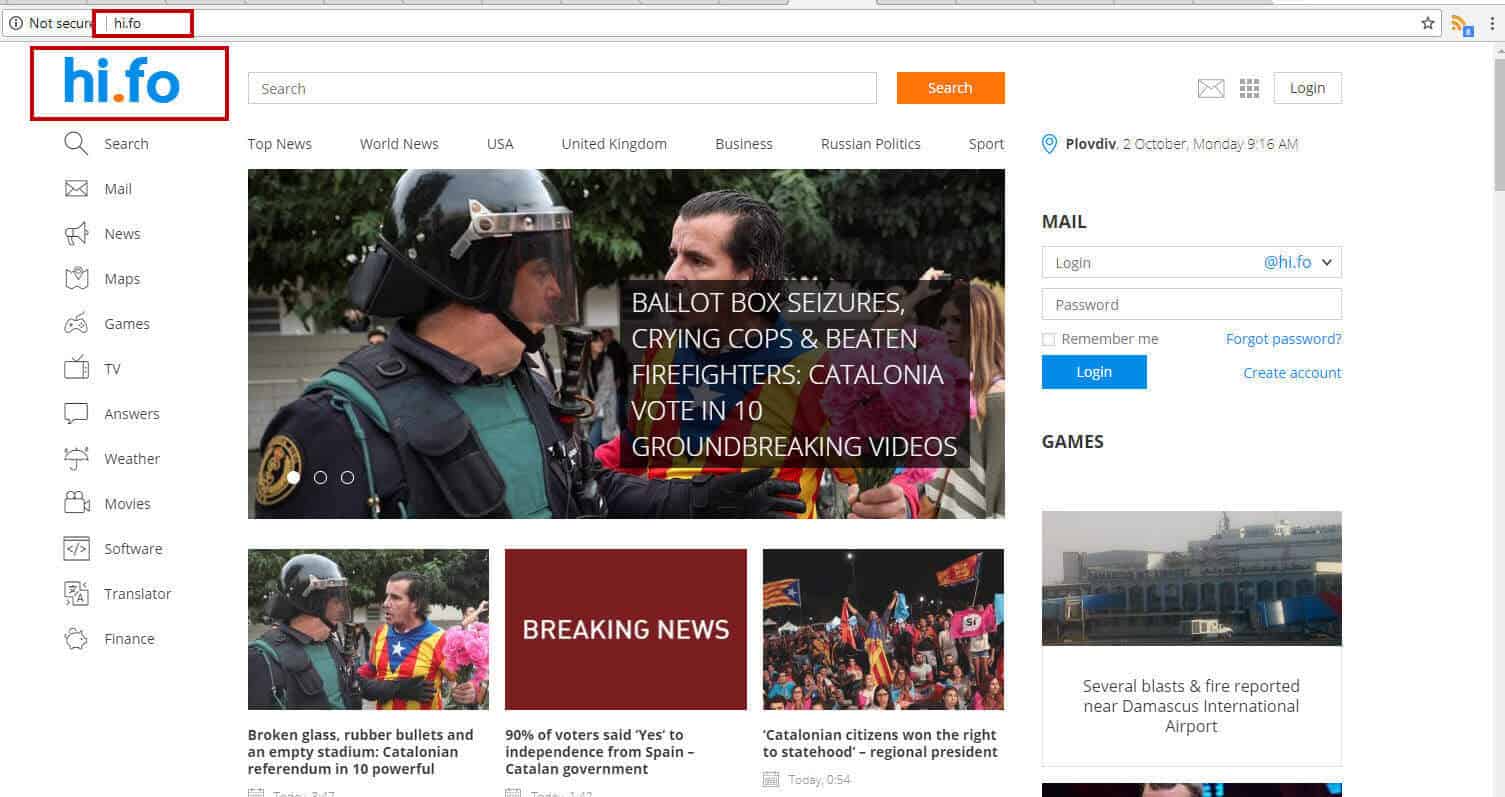
Today we are going to talk about the reasons why Hi.fo “Virus” normally targets only your browsers (Explorer, Firefox, and/or Chrome) and is classified as a browser hijacker. Moreover, we are going to discuss all the characteristics that usually describe a piece of software like this. Among them we can distinguish the hijackers’ ability to distribute a lot of fairly irritating advertisements; to send you to web locations that you haven’t planned to go to; or to set some new homepages/ search engines to your browser apps. What’s more, we are going to give you some preventive advice in order to avoid that kind of software, once you have successfully gotten rid of the current Hi.fo “Virus” infection. In order to remove this irritating program safely we have created a handy Removal Guide, which you can use for free! You just have to scroll down and check it out.
Hi.fo “Virus” essential information
It is a piece of software that belongs to the browser hijacker category – a fact that gives a perfect explanation for why this program may be able to do some changes to the browser apps you have installed on your computer. A product such as this may repeatedly bring some even more irritating changes to your settings of the browser. Among the probable modifications may be the display of lots of online ads; and the likely occurrence of some bothering redirection processes. Also, the broadcast of some unfamiliar search engines and/or homepages could be quite odd. Any other effects resulting from Hi.fo “Virus” are more or less unlikely.
Are browser hijackers similar to malware (such as Trojans or Ransomware)?
Hijackers could indeed top the list of the most annoying software versions that you might ever catch while browsing. Nonetheless, they are not connected to any viruses, and they have not had or shown any damaging characteristics or effects so far. The characteristic features of malware (like Ransomware and Trojan programs) can incorporate reviewing your data and encoding it, particularly the pieces you access most often. What is more, any normal virus, for example, one from the Ransomware group, is always absolutely capable of ruining your system as a whole, or deleting any of your most important files. Plus one more characteristic of the famous malware versions, for instance – the Trojan-based programs, is their ability to spy on you and track every single of your actions online and often even offline. One more irritating aspect is that all these illegal and deleterious changes may occur so subtly that you may not notice them before they have resulted in some awful damage.
How does a normal infection process occur? Can Hi.fo “Virus” get self-installed on your computer?
The possible ways of distributing Hi.fo “Virus” are normally connected to the reasons why software like this gets created in the first place. Actually, programmers have the habit of spreading hijackers and other versions of ad-broadcasting software by mingling them in bundles with numerous different programs, apps and games. Generally, such software sets are typically free since the people who create them get paid for sending the ads the hijackers inside them can show on the victim users’ screens. Anyway, every infection which is caused by Hi.fo “Virus” is not probably to result from the ordinary act of downloading a mixture like this. Such contamination could only occur if you decide to install the already downloaded bundle in a wrong way by selecting an installation option, which does not give you the permission to select what to include into your computer, and what from a given bundle to exclude from the process.
If you really want to keep your system hijacker-free, and to have the chance to install only the components of one particular bundle that you really need, it’s compulsory that you go with the most detail-giving installer characteristic (either the Custom, the Customized or the Advanced one). This is the only way to control the installation process of any bundle or a specific program all the time and stay safe from any threats!
For the infections that have already occurred, you can find your solution in our Removal Guide here. Check it out!
SUMMARY:
| Name | Hi.fo |
| Type | Browser Hijacker |
| Detection Tool |
How To Remove Hi.fo “Virus”
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment