Hijack.host
Hijack.host Malware is a suspicious program, being flagged as a potential computer virus of the Adware family, by a number of security databases. Adware is a type of malware easily recognizable by the numerous unwanted advertisements or ads for short it subjects the affected users to. Also the so called browser redirects are a common theme – when the user tries to open a certain web address but instead of or in addition to it another one opens up in a new tab or a new window.
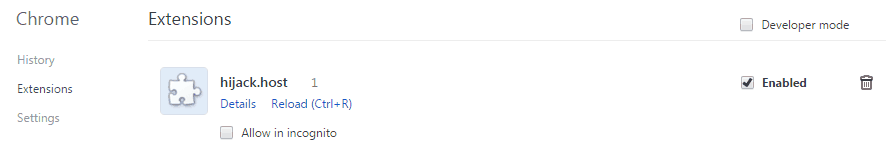
The hijack.host Malware will display pop up ads and messages
How did you end up with Hijack.host Malware?
There are a few ways in which you might have fallen victim to an Adware infection. We are going to list the most probably ones and provide some insights into how to avoid this from happening again.
- E-mail attachments. You are probably aware about that one as it seems it has been around forever. Yet a lot of viruses are spreading with the help of e-mails. Always scan any files attached to messages in your inbox before downloading them. Also be extra vigilant and carefully check the messages sent to you by seemingly legitimate companies and organizations if they contain any attachments. Very often phishing schemes are employed.
- Infected files downloaded from torrent or other file sharing websites. This is also a very common method for malware distribution. Such websites are notorious for the low level of control enforced upon the uploaders and the files being uploaded. That leads to compromised files often enough to make this one of the most probably ways for users to get infected with Adware. The same advice as for the e-mail attachments applies here as well – always scan any downloaded files before opening them.
- By far the most probable way in which you may have gotten Hijack.host Malware though is through something called a bundle installer. It is a fact that almost no one chooses to voluntarily and purposely install an Adware application. Yet for all intents and purposes that’s exactly what you probably did. Seems confusing, doesn’t it? Let us explain what a software bundle is and all this will be much clearer. Bundle software installers or bundle installations are programs, mostly free ones, which have other programs “hidden” in their installers. They are not actually hidden as you can easily prevent these additional features and programs from installing if you just click on Advanced installation options before starting the installation process. Most people don’t and that’s how they end up with software they didn’t want in the first place, just like Hijack.host Malware.
Now is a good time to clear up some things before you begin with the actual removal of Hijack.host Malware. We feel this is important, so it is probably a good idea to read to the end. Adware creators modify their software so that it is harder for removal blogs and guides not unlike our own to be able to present universal removal instructions to all affected users. It is true that this task is almost impossible. For this reason we have prepared a step-by-step removal guide that is extensive and covers almost all different scenarios. It is entirely possible that you may find some parts of it or maybe even whole steps redundant and unnecessary. If that happens just skip the parts you don’t find pertinent to your problem and continue with the other steps. If you have questions or suggestions for us, and we are always open to those, hit us up at the comments section, we are looking forward to your feedback.
SUMMARY:
| Name | Hijack.host |
| Type | Adware |
| Detection Tool |
Remove Hijack.host Malware
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android , iPhone

hello so ive been having problems. i found some ip addresses under my local host. i was wondering what i should do. thanks
Hi Nathan,
can you be more specific? Can you post them here or make us a screenshot so we can check them up ?
Hi amer,
i would suggest to you to delete these entries.
Hello there, you should probably remove those IP’s (delete them from the Hosts file). However, in order to be certain, we advise you to send us a screenshot of your hosts fie.
Normally, no IP addresses should be present below Localhost so you should probably remove those addresses from your Hosts file.