Hoop
Hoop is a computer infection based on Ransomware code and its goal is to prevent you from using or otherwise accessing your personal files. After Hoop locks your data, it will ask you to pay a ransom to release it from the lockdown.
If the ransom sum demanded by the virus isn’t paid on time, the hackers behind this virus threaten that they will never release the locked files. Of course, if the files on your PC are not important to you or if you have safe copies of them on another device or on a cloud storage, then the effects of the virus’ attack will be negated. In fact, if you have been hit by this virus and some of your data has become inaccessible, make sure to check your other devices (without connecting them to the infected computer) for any backup copies of the locked files. This is the first thing you should do in case of a Ransomware attack. If you find any backups that will allow you to restore your data, all you’d need to do is follow the removal instructions from below and, after you eliminate the virus, restore your data from the backup device.
The Hoop virus
The Hoop virus is a malicious program capable of secretly launching a data-encryption in your computer that would lock all of your files. The Hoop virus belongs to the Ransomware virus family because it asks you to pay a ransom for the private decryption key.

Through this key, the user should be able to recover their data, making it accessible again. However, the blackmailers don’t really give a guarantee that the key would be received by the victim after the payment. Of course, the hackers promise you that they will help you recover your files if you pay them, but can you really trust such a promise?
So, what can one do if some important data on their computer has gotten encrypted by Ransomware such as Hoop, Reqg, Noaa and there aren’t any backups from which the files could be recovered? Well, paying is certainly not the wisest of options here as we already established. The preferable course of action in such a situation is to first remove the virus. The removal itself won’t set the files free but will give you the freedom to try some alternative solutions for file recovery without fearing a second encryption of any of the data you may manage to restore.
The .Hoop file extension
The .Hoop file extension is a filename suffix that keeps encrypted files unrecognizable to any program the victim may have. The .Hoop file extension isn’t a regular extension and it doesn’t correspond to an existing file type so programs don’t recognize it.
You won’t be able to manually remove this extension, but if you try some of the suggested alternative recovery solutions from your guide, you may need to. We can’t guarantee anything with regard to the recovery of your files but it is certainly better to first try the suggested alternatives that are free before you consider the ransom payment as a possible option.
SUMMARY:
| Name | Hoop |
| Type | Ransomware |
| Data Recovery Tool | Not Available |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Remove Hoop Ransomware
![]()
To clear the Ransomware from your system, you must first disable the process or processes that it is running on your computer. You can see what processes are currently active in the system by accessing the Task Manager. One way to access it is by pressing Ctrl+Shift+Esc. From the window of the Task Manager, select Processes and there you will see all processes that are running on the machine at the given moment. Among them should be the one or ones behind Hoop but their name will likely be different so as to remain undetected for longer. Use your common sense to try to figure out which of the listed processes could potentially be linked to Hoop. Some potential red flags that could help you single out the Ransomware process are high RAM and CPU usage and an unusual and/or unfamiliar name. Another possible sign that a given process in the Task Manager may be linked to the malware is if there isn’t a program that’s currently open on your computer that is responsible for running the process in question.
An important thing to mention here, however, is that there are many system processes that, at times, could seem suspicious to less experienced users due to their odd-looking names and tendency to use lots of system resources. Therefore, the first step towards checking any processes you deem suspicious is to look up their names to confirm that they are not legitimate ones that are from your OS.

If the process you suspect isn’t from your OS according to your online search, then right-click on its name, select the Open File Location option and scan all the files stored in there using the free scanning app posted below:

If you have a reliable antivirus or anti-malware program on your PC, you could use that one as well for best results.
If during the scanning of the files either of the scanning options you are using warns you about detected malware, then the process you suspect of being linked to Hoop is probably the one you have been looking for. Go to that process in the Task Manager, right-click on it once more, and select the End Process tree option to quit that process as well as any others related to it.
Next, return to the folder with the files of the process and delete the whole folder. If an error comes up telling you that one or more files from that folder can’t be removed at the moment, open the folder, delete all files that you are allowed to remove, and go to the next steps. Upon completing everything from this page, come back to the File Location Folder and try deleting it again.
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
This next step will require you to access/enable Safe Mode on your PC – a very important step when troubleshooting most types of software-related problems. Safe Mode will only allow the most essential OS processes to start when Windows loads and will block any other processes that are launched on startup, including ones related to the Ransomware so that even if you haven’t disabled all Hoop processes in the previous step, they won’t be active to interrupt the troubleshooting. You can find instructions for different versions of Windows on how to enter Safe Mode on this link.
![]()
Next, you will have to check the apps and programs that are set to automatically start with Windows – oftentimes virus threats automatically add themselves to the list of startup items. You can check what programs are launched automatically on startup from the System Configuration tool. You can access it from the Start Menu. by typing system configuration and pressing Enter.
Once in the System Configuration window, go to the Startup tab and look at the listed startup items. Ones you think may be linked to Hoop and/or ones you don’t recognize must be unchecked (the tick in front of them must be removed). It is also a good idea to uncheck any items that are listed with Unknown manufacturers (unless you recognize and trust those items).
Finally, select the OK button to complete the changes and proceed with the remaining steps from the guide.
![]()
Access the Hosts file of your PC by placing this line of text “notepad %windir%/system32/Drivers/etc/hosts” (without the quote marks) in the Start Menu and pressing Enter.
Check if there’s any text under the “Localhost” line and if there is, copy that text and put it in the comments on this page. Many forms of malware and even some regular programs need to make changes in this file in order to complete their goal. If there is any text (usually IP addresses) written below Localhost in the Hosts file, this means that the file has been tampered with by third-party software. However, to confirm that the changes to your Hosts file have been made by a malware like Hoop and not by a legitimate program, we must first have a look at them.
After we receive your comment and examine the text/IP addresses from your Hosts file that you have sent us, we will reply to that comment, telling you whether you’d need to take any action. If the changes to your Hosts file are from the Hoop virus (or from another malware or unwanted software), will have to delete the what’s written below Localhost and then save the changes to the Hosts file.
![]()
Warning: This step is very important but could also lead to problems with your PC if not executed carefully. You will be required to delete malware-related items from the Registry of your computer. Lots of important and sensitive settings are stored there and so you must be certain that what you are deleting is from the virus and not from your system. In case you have any doubts about anything while performing this step, always make sure to ask us in the comments first before doing anything you aren’t certain about.
You can search for the Registry Editor by typing regedit in the Start Menu. An icon named regedit.exe should appear on your screen – right-click on it, select Run as Administrator, and then click on yes when asked to allow the app to make changes to the PC. Next, press the Ctrl and F keys when the Editor opens and type the name of the Ransomware threat. Click on the Find Next button to search for items with this name and if a such item is found, delete it, click on Find Next again, delete the next item, rinse and repeat until no more items with that name are left in the Registry.
Afterwards, find those next folders/directories in the left panel of the Registry Editor.
- HKEY_CURRENT_USER > Software
- HKEY_CURRENT_USER > Software > Microsoft > Windows > CurrentVersion > Run
- HKEY_CURRENT_USER > Software > Microsoft > Internet Explorer > Main
In them are likely to be located items related to Hoop that don’t carry its name. Usually, malware items in those Registry directories have very long names of randomized letters and/or numbers that stand out from the rest, so they shouldn’t be too difficult to spot. Still, if you are unsure whether there are any Ransomware items that need to be deleted in those folders, do not hesitate to ask us about it in the comments below.
![]()
Lastly, one by one, place the next lines in the search box of your Start Menu and hit Enter after each to access the folders that they link to.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
In those folders, you are supposed to delete all of the most recent files, so it would help if you sort the files in them by creation/modification date. All files from the moment the virus infected you to the current one must be deleted. The only exception is the Temp folder – in it, you must simply delete all files stored there.
The last thing you must do to complete this guide is go to the File Location of the Ransomware process (from Step 1) and try to delete it again – this time the error message stopping you from deleting the folder shouldn’t appear.
How to Decrypt Hoop files
It is important to understand that, while the steps provided here should help with the deletion of the Hoop virus and stop the threat from encrypting more of your files, they will not decrypt any of the files that have already been locked by the Ransomware. After you have cleaned your computer from Hoop, you will have to perform some additional actions to try to bring back your encrypted data. One option is to still pay the ransom, but we advise against this course of action because the hackers behind Ransomware threats such as this one cannot be trusted and also because not everyone may be able to afford the ransom sum. Because of this, we’ve tried to put together a separate How to Decrypt Ransomware guide that you can find on the provided link. In that guide, we have compiled several different alternative file-recovery techniques that you can use separately or in combination with one another to hopefully recover the Ransomware-locked data.
Do not forget to first make sure that the threat is truly gone from the PC to avoid a second encryption of files you may manage to bring back. If you suspect the virus may still be present in your system, you can use the aforementioned free scanner tool offered on our site to test suspicious files for malicious code.
Final Notes
We hope that the guidelines we have posted on this page will aid you in the successful removal of Hoop. In case completing the manual steps was not enough to clean the virus, do not forget about the recommended removal tool available on this page – its powerful anti-malware abilities allow it to quickly clean all sorts of malicious threats as well as to keep your system secure against potential future malware attacks.
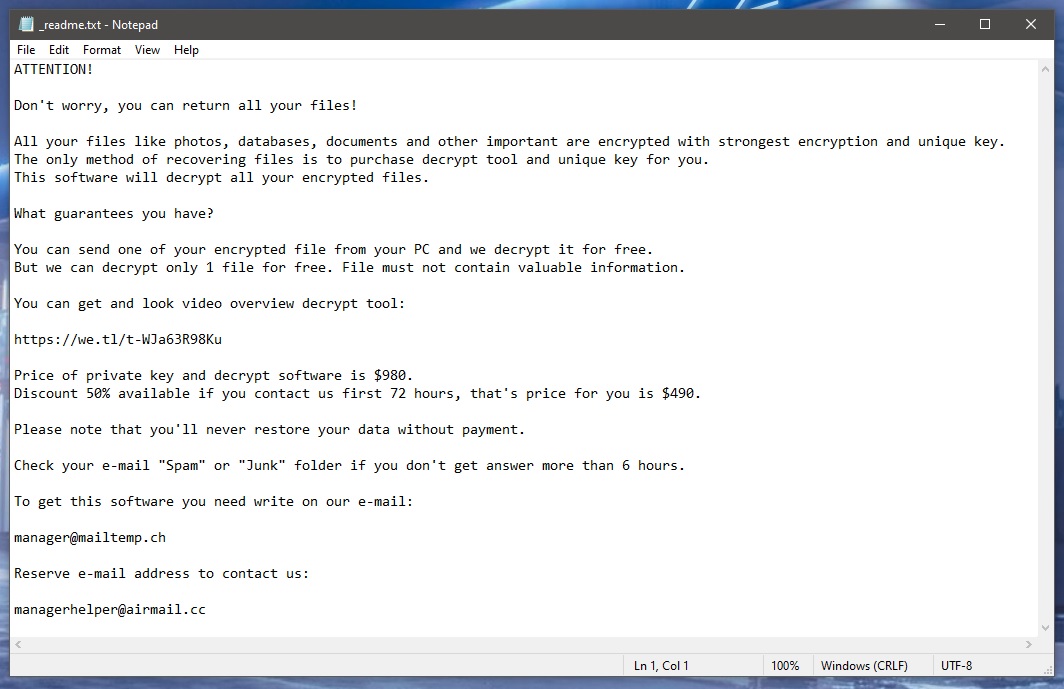
Hoop is a serious malware threat that can put encryption on the most important files on your computer and later blackmail you for the decryption key. Once Hoop completes the file-encrypting process, it displays a ransom-demanding note, where it’s explained how to pay the ransom.
If Ransomware like Hoop attacks you, you will likely not notice anything at first. Most Ransomware threats are very sneaky and are able to remain unnoticed by the built-in defenses of the system and any third-party antivirus software that the user may have installed. Furthermore, many forms of Ransomware are helped by Trojan backdoor viruses that enable the Ransomware to secretly sneak into the machine and perform its file-encrypting actions without triggering any security warnings.
After the targeted files have been encrypted, the virus automatically reveals its presence through the aforementioned ransom note, which details the specifics of the attack and the required payment methods. Typically, the hackers require the ransom sum in Bitcoin or another cryptocurrency in order to ensure that the transaction cannot be traced to them.
Hoop is a special type of malware virus known as file-locking Ransomware. The goal of the Hoop virus is to lock your files through the method of encryption and then demand a ransom payment from the victim if the latter wishes to restore their data.
Other than encrypting your files and displaying a ransom note on your screen, the Hoop virus would likely not cause any other type of harm. Because of this, if you have backup copies of the important files that the virus may have managed to lock up or if there aren’t any important files on the computer that got encrypted, then the effect of the Ransomware attack would be pretty much nullified. However, it must be said that it’s possible that other threats may have arrived in the computer alongside the Ransomware, including Trojans and Rootkits that may cause other types of harm. For this reason, even if no important files have been locked by Hoop, it’s still important to check the entire system for malware and delete anything suspicious and/or potentially harmful.
To decrypt Hoop files, you can either pay the ransom required by the hackers or attempt to recover the data through alternative means. If you choose to decrypt Hoop files via an alternative method, it’s important to first remove the virus from your PC.
It is usually strongly recommended that users do not give in to the demands of the blackmailers and send them the ransom sum. The main reason for that is the lack of certainty with regard to what’s going to happen next – it’s possible that the victim receives the correct decryption key, but it’s also possible that no key gets sent to them or that the key they receive doesn’t work as intended. Another possibility is that the hackers may no longer be using the crypto-wallet they’ve included in the ransom-demanding note, meaning that you may end up sending your money to someone who has nothing to do with the Ransomware and cannot help you with the decryption of your files.
For these reasons, it’s preferable if you first at least try some of the available alternatives to see if any of them can help you with your data recovery.

Leave a Reply