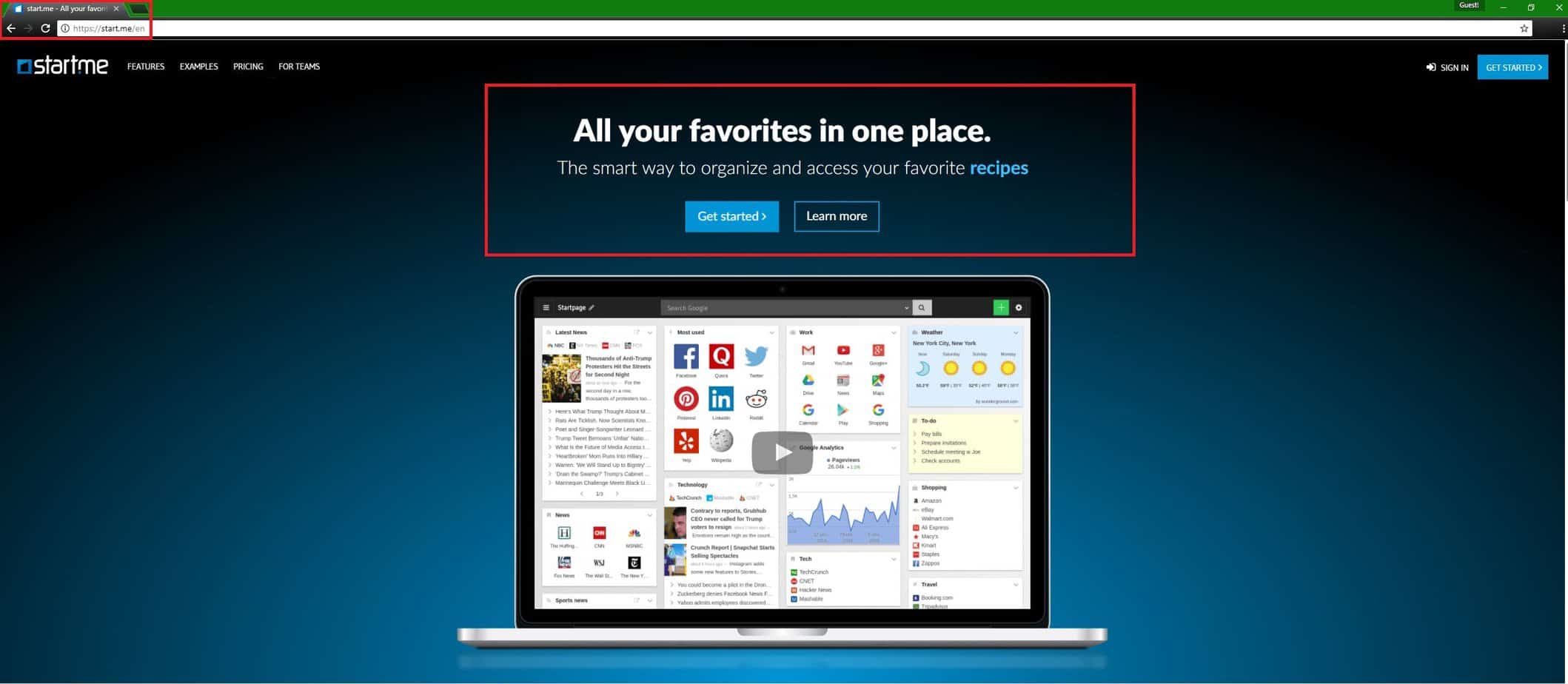
Start.me
When Start.me gets installed on your system, your default browser (be it Chrome, Firefox, Explorer or other) usually starts to behave strangely. Sudden page redirects, modifications in its homepage or search engine may take place without your approval and as a result, a flow of aggressively popping ads, banners and promotional messages may cover up your entire screen.
This is a typical browser hijacking activity and in the next lines, we are going to tell you how exactly to deal with it. For that, we have prepared a special removal guide with exact instructions on how to uninstall Start.me and remove its changes. First, however, we would advise you to read the information that follows below, because it will give you a good idea about the typical behavioral traits of such software.
The main reason for writing this article is Start.me – a legitimate browser extension that modifies the new-tab page of the user’s browser, thus allowing for more customization options, easier access to various forms of web resources and other useful features. However, we haver received reports that Start.me sometimes gets promoted and potentially added to user’s browser by actual hijackers. Although many users might indeed find Start.me to be useful and helpful, we still need to elaborate upon the methods it could might get added to your browser via hijacker applications and what you’d need to do if such a thing happens to you. Remember, getting your new-tab page changed with Start.me might actually be an improvement but if it happened without your knowledge or permission, this might indicate a browser hijacker-related issue that needs to be taken care of.
What is actually a browser hijacker?
Hijackers are often mistaken for viruses or some other type of a nasty online infections, similar to Trojans and Ransomware. However, we have some good news. Most such programs have no malicious capabilities and are not among the cyber infections that can cause many problems for their victims. Apart from messing with your Chrome, IE or Firefox browser (or any other browser you might be use), such software cannot typically cause you any major system harm, corrupt your files, steal your passwords or involve you inn some type of a cyber crime. These harmful activities are specialties of the real viruses and a threat the likes of a Trojan or a Ransomware will definitely not spare you from them.
A browser hijacker, on the other hand, is only seen as a potentially unwanted program, which is related to common browsing disturbance and some indirect risks. As we mentioned, it could try to alter the functionality or appearance of your browser by adding to it a new search engine, a new homepage or in this case – a new new-tab page such as Start.me. Still, it is not fatal if you have such software on your system, but there are also a number of reasons why you may want to uninstall it. Even if Start.me isn’t causing you any problems, there might be other things caused by the hijacker that could actually cause some irritation and maybe even expose your system to certain indirect risks. The most obvious irritation coming from hijackers could be the constant redirect to unwanted web pages. In most of the cases, such a technique is used to help these pages increase their rank or sales, so it is not surprising that they are full of commercial ads, links, banners, and similar content. It is not advisable to open them because you can never be sure how safe they are and some ads may eventually mislead you or trick you into installing some other potentially unwanted programs or even dangerous viruses on your computer. As mentioned above, after the hijacker becomes part of the system, it may change some of the browser settings such as a cover page (or new-tab page), a default search engine, and so on. After changing the browser configuration, this threat may begin to track the victim’s browsing habits and may collect information about the most frequently visited web pages and the data that is entered when visiting these pages. Although this activity is not considered dangerous, it could still be seen as a privacy violation and a good reason for this software to be uninstalled.
How did the browser hijacker promoting Start.me has gotten inside my computer?
A browser hijacker may appear in your browser after downloading free software. In most of the cases, the programs used to distribute such software are free installers, download managers, torrents, spam email attachments, PDF creation programs, and other similar applications that are available for free. Keep in mind that you should monitor the installation process of each of these programs because they may contain different components. Usually, the presence of additionally bundled applications like the browser hijackers promoting Start.me is indicated somewhere in the installer with a small print, so you must always choose Custom or Advanced settings to install free software and uncheck the pre-loaded bookmarks. You should know that the browser creators usually have nothing to do with this issue. In fact, the browser hijacker is hiding on your computer. To remove it, use the instructions below.
How do I remove such unwanted software?
First of all, you should know that removing a browser hijacker requires certain knowledge about computers and their systems. That’s why, if you are not really confident in detecting and deleting the hijacker that has added Start.me to your browser manually, it’s better to think about automatically removing the unwanted program with the help of a specialized removal tool like the one suggested below. Still, if you think you can handle manual removal of the program, here’s the guide to follow.
SUMMARY:
| Name | Browser hijackers promting Start.me |
| Type | Browser Hijacker |
| Detection Tool |
How to Remove the browser hijacker promoting Start.me
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment