This page aims to show you how to remove Tech-connect.biz. These Tech-connect.biz removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
What to do if your browser has been hijacked?
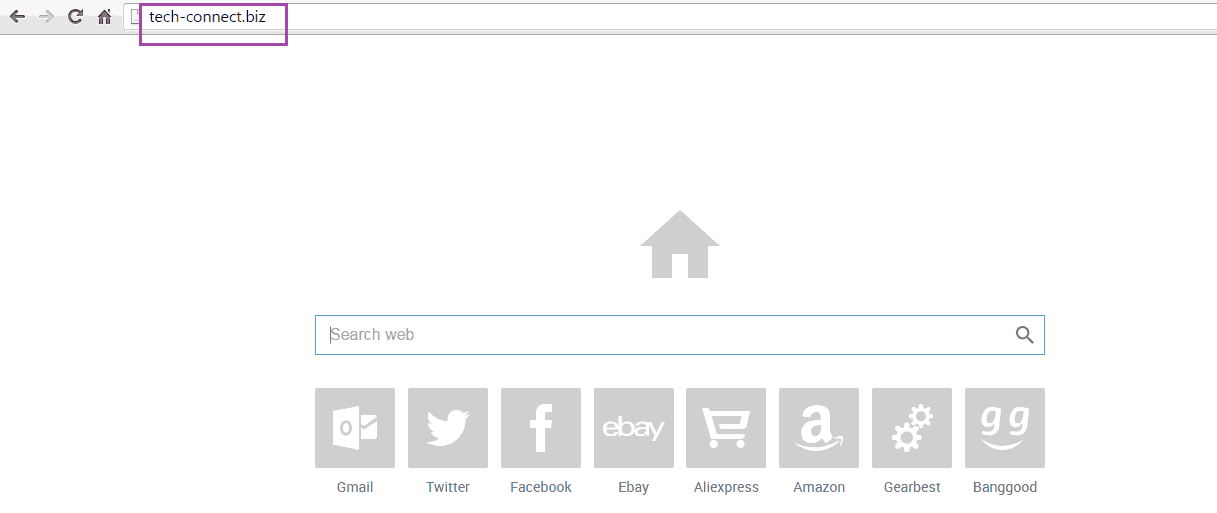
Having your browser invaded might sound scary for those of you who have not been acquainted with the program responsible for this. However, once you understand how it actually works and how you can deal with it, you will realize that there’s nothing to be worried about, as long as you remain careful and make sure you eliminate the unwanted software as soon as possible. If that is your case and you’ve found out that your browsing program is no longer under your control, then you have probably had Tech-connect.biz installed on your PC. This is a program of the Browser Hijacker type. Once inside your PC, it integrates itself within all your browsers (Chrome, Firefox, IE, etc.) and starts messing with them: it might change their homepage or default search engine or even redirect you to unwanted pages as soon as you try to use them. All in all, a pretty irritating piece of software to have around. This invasive behavior of Browser Hijackers is the reason for the existence of this article. Since there are so many people out there who have fallen prey to Tech-connect.biz and probably all of them are seeking a way to remove it, we are here to help by providing all the necessary information and tips regarding this unwanted software. Apart from that, below the main article there is a manual that contains detailed instructions on how to get rid of the intrusive program. Still, our advice for you is to first read the rest of the article and then go to the removal guide. It is essential that you learn more about Browser Hijackers in order to effectively deal with them in the future.
Tech-connect.biz “Malware” – is it malicious or is it a mere annoyance?
You might find different opinions concerning this topic – some might claim that Tech-connect.biz is malware or some sort of a nasty harmful virus similar to the infamous Ransomware, while others will tell you that there is nothing dangerous about this program. Well, the truth lies somewhere in between. What we can say though is Tech-connect.biz is not “malware” in the true sense of this term.
On one hand, Browser Hijackers are undoubtedly not viruses. There is a big difference between these two types of programs. Malicious software such as Ransomware or Trojan Horses can definitely cause a lot of harm to your system, files and online security. Compared to that, a simple Hijacker such as Tech-connect.biz can merely irritate you with its presence and obstruct your regular online experience. That is why, when faced with such a program, the most important thing is to remain calm. There’s most likely no need to call a specialist, since you should be able to deal with the issue yourself as long as you follow the instructions in our guide.
On the other hand, though, there are several questionable and obscure traits of Browser Hijackers that you need to be aware of. For example, a program of this type might look through your browsing history and monitor your online activity. The acquired data could later be used to spam your browser with intrusive ads that have been modified according to your personal interests. Another thing you need to know about Tech-connect.biz is that it could display false warning messages in your browser, claiming that your PC needs a certain software tool in order to either deal with a certain unlikely security threat or to resolve a number of non-existent PC errors. If you fall for this warning, there’s a high chance that you might end up installing even more unwanted and intrusive software on your PC. On top of all that, a Browser Hijacker might decrease the productivity capabilities of your PC, causing it to experience a serious slowdown due to high resource consumption of the unwanted software.
How to prevent installing Browser Hijackers
One other substantial difference between Hijackers and viruses is that the former, unlike the latter, often get on people’s PC’s by actually being installed by the user. This happens via the method known as file-bundling. A file bundle is a program installer that has some other minor add-ons incorporated within it beside the main install. Often users want to install only the main program, but since most of them use the Quick (Default) installation settings, they also get the add-ons. If one of the added applications is a Browser Hijacker, it also gets inside the PC without the user’s knowledge. To avoid this in the future, make sure to always opt for the custom settings when installing new software. From there, you can actually see all added content and determine which stays and which is left out of the installation. If something there seems shady and potentially unwanted, do not hesitate to uncheck it before continuing with the installation of the main program.
SUMMARY:
| Name | Tech-connect.biz |
| Type | Browser Hijacker |
| Detection Tool | Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Tech-connect.biz “Malware” Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Reply