This page aims to help you remove как удалить Time to Read. These Time to Read removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows. Russian readers may want to check Как Удалить Тime to Read.
Time to read
Do you experience reduced quality of browser experience due to intrusive ads? Time to Read may be the reason for that.
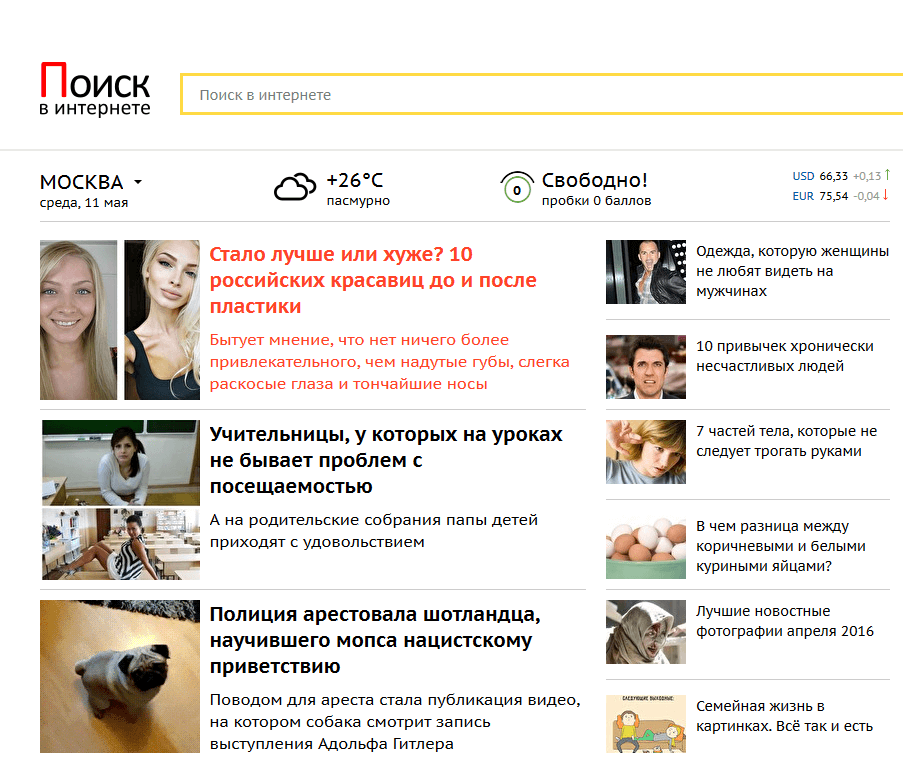
The browser add-on Time to Read is one of the many programs that fall under the Browser Hijacker category. These are generally considered unwanted due to their intrusive character and tendency to annoy people and prevent them from effectively using their browser. Browser Hijacker affect all of your browsers, so you’ll want it removed asap. It won’t matter if you’re using Chrome or Mozilla or IE – the Browser Hijacker will get to them all. Once inside your system, Time to Read will start generating all sorts of intrusive adverts for your browser: pop-ups, banners, box messages – everything you can think of. Occasionally it will also redirect you to a page that you did not attempt to open at all – Time to read.ru. All of this may sound kind of nasty, but there’s no actual reason to worry. As frustrating as Browser Hijacker add-ons are, they are pretty much harmless for your system. Besides, it is quite easy to deal with them if you know what you’re supposed to do. For that, we have prepared a guide focused on the uninstallation and removal of, as well as как удалить Time to Read.
Even though the program usually poses no real danger to your PC, it’s better to have it removed as soon as possible. The first reason for that should be obvious – the ads can be extremely annoying and won’t let you enjoy your browsing. Second and arguably more important reason is that there’s still some possibility that Time to Read may lead you into exposing your machine to potential danger. We already said that the intrusive plug-in is not harmful itself, however the ads it displays might be. That’s why clicking on them is considered a bad idea. Though rare, it is possible that some of these pop-ups may land you a nasty virus or redirect you to a malicious and illegal website. There’s just no need to compromise your PC’s security in such a way. There is currently no information about ransomware infections originating from Browser Hijacker, but there are plenty of other nasty viruses out there, so watch out! Therefore, we strongly advise you not to click on any of the displayed ads. Should you get redirected to a page that you did not mean to open, make sure you close it as quickly as possible.
Prevention
Knowing how the intrusive program gets installed on your computer is essential when dealing with Browser Hijacker. It’s just so much easier to prevent Time to Read entering your PC, than it is to deal with it removed afterwards. There are several distribution methods, via which the program gets in people’s systems. Here, we’ll list the most common ones:
- Torrent and file-sharing sites – this type of sites are often potential distribution points for Browser Hijacker. The reason for that is because many of those sites are illegal and usually everyone can upload everything. Furthermore, since most Browser Hijacker programs are actually legal, you may find yourself landing one even if you’ve downloaded something from a legitimate site. Just remember – the shadier the site you visit, the greater the chance of landing a unwanted program becomes.
- Spam e-mails – this is probably the most common distribution method for Time to Read and other Browser Hijacker. This one, however, is somewhat ineffective. That is because unwanted e-mail letters usually go to the spam folder so that you know you should not open and read them. However, there’s always the chance that a spam message may get into your regular inbox. Therefore, make sure that you always pay attention to the title of the letter and the name of the person who’s send it to you.
- Program-bundling – arguably the most successful method for Browser Hijacker distribution. The reason for its effectiveness is users’ lack of attention to the installation menu of the programs they install. When Time to Read is distributed via this method, it is bundled with a program (usually a cheap or a free one) and once that program is installed, the Browser Hijacker gets installed along. Preventing this from happening is easy. You just have to find the list of the added installs and uncheck everything that seems suspicious. Sometimes the list will be displayed in the regular menu, sometimes you may need to go to the custom/advanced settings menu. Keep in mind that it is possible for Time to Read to go under a different name there. If you are not sure, you can simply uncheck everything.
And there you have it – follow these simple rules and you should have no problems with any intrusive software for future. If you feel that you need better defense against Browser Hijacker programs, you may consider investing into an anti-Browser Hijacker tool – a good way to add an extra layer of protection for your PC. If you currently have Time to Read on your PC, head down to our guide below this article.
SUMMARY:
| Name | Time to Read |
| Type | Browser Hijacker |
| Detection Tool |
Remove Time to Read
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment