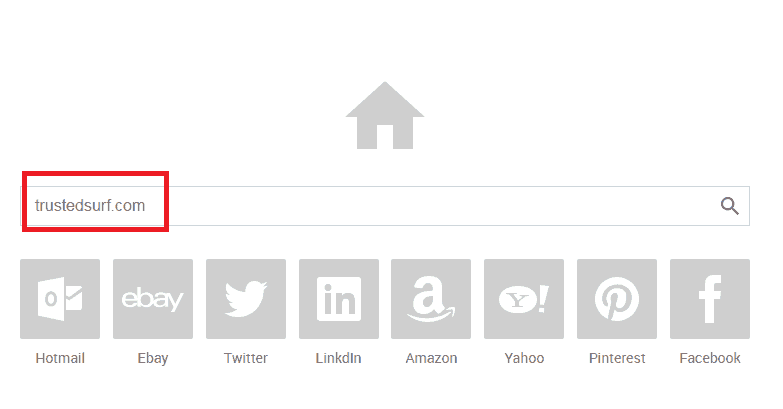
This page aims to help you remove the Trustedsurf.com “Virus.” The Trustedsurf.com home page removal guide works with Chrome, Firefox and Internet Explorer, as well as every version of Windows. But, before we go into the removal process, it is good to have an idea of what you are dealing with. Bear in mind that although the Trustedsurf.com .com homepage is commonly believed to be a virus, it is not. PC viruses can potentially cause a lot more damage to your PC than what is described here. Although we call Trustedsurf.com “virus”, we only do it for expediency in order to not confuse our readers before we explain what it actually is.
What is the Trustedsurf.com “Virus”?
Trustedsurf.com is an browser hijacker. It is a non-malicious piece of programming code that seeks to provide you with information in the form of advertisements. Do note that browser hijacker and virus are very different. A virus is a piece of programming code that is harmful – it is programmed to inflict damage to you and your computer. According to this definition, browser hijacker may seem harmless and hence, not necessary to remove. However, if you do have the Trustedsurf.com “Virus” homepage on your computer, it is still recommended for you to remove it.
Why should I remove the Trustedsurf.com “Virus”?
This seemingly harmless browser hijacker can actually cause a lot of unwarranted trouble. It is programmed in such a way that it is able to track your browsing patterns and history, favorites and bookmarks. After gathering these information, it will, then, generate convincing and tempting ads for your viewing. These ads may appear in the form of banners, pop-up ads and boxes or even as a separate window. It may be displaying coupons or deals of items that you are inclined towards purchasing. Regardless of the form that these ads take, do not click on them. If you do happen to click on these ads, you will be directed to sites that are of no value to you. These sites may be previous webpages that you have visited where the “deals” can be found. As these are sites that can be found in your browsing history, re-accessing these sites will not value-add in any way, and thus will only be a waste of time. Alternatively, these sites might be one of the many pay-per-click sites that will allow the creators to earn some money when you access these pages. Worst case scenario, these sites might be those that acts as a portal that allows other browser hijacker to gain access into your computer. Hence, you can see that clicking on the ads and accessing the sites is, in no way, beneficial to you.
How do I get Trustedsurf.com in the first place?
It is always good to know how you got infected the first time round, to be able to avoid being infected again.
One of the most common ways in which people get infected is via the many free and illegal program downloads that are readily available on the Internet. This is achieved through a process called bundling. Through bundling, this browser hijacker is being combined with the program together as a set. Thus, when people download said program, the browser hijacker gets downloaded along with it,, without the knowledge of the user. However, know that this browser hijacker is unable to function without it being installed. Therefore, it is crucial for you to take extra caution and be diligent when it comes to the installation process.
During installation of the program, instead of attempting to save time and opting for the “Automatic Installation” option, go, instead, for the “Custom Installation”. Though it might take a few minutes, trust me, it is worth the hassle that ensues otherwise (like having to remove the browser hijacker separately after). During the custom installation, there will be a step where you are able to see a list of the files and folders that are to be installed onto your computer. This is the part that you should be careful and diligent about: look carefully through the names and uncheck any that seems unfamiliar to you. You can always reinstall any missing files, if needed, later on, but that, usually, will not be the case.
SUMMARY:
| Name | Trustedsurf.com |
| Type | Browser Hijacker |
| Detection Tool |
Trustedsurf.com Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Hello,
You should definitely remove the bottom 5. Let us know how that goes.
Hello,
is the problem browser restricted to Firefox only? Or do you experience problems with other browsers as well?
The homepage has been removed on all my browsers, the problem now is that occasionally I get an ad pop up on a separate tab while browsing a website.
Hello Elexy,
This is entirely possible, even if you have rid of trustedsurf. Do you use any kind of Adblocker?
got some
127.0.0.1 down.baidu2016..com
127.0.0.1 123.sogou..com
127.0.0.1 http://www.czzsyzgm..com
127.0.0.1 http://www.czzsyzxl..com
127.0.0.1 union.baidu2019..com
Hello, please delete all of these lines from your Hosts file.
delete the lines in the notepad and save it back in the same folder? It prompts me with save in MyDocuments instead? If I save it there and I type in notepad %windir%/system32/Drivers/etc/hosts again it just pulls up the original file with the lines still there
127.0.0.1 down.baidu2016..com
127.0.0.1 123.sogou..com
127.0.0.1 http://www.czzsyzgm..com
127.0.0.1 http://www.czzsyzxl..com
127.0.0.1 union.baidu2019..com
Hi johnnyapple,
Hosts that start with 127.0.0.1 are legit. These are local hosts and can’t harm your system.
Hi Gary, we’ve tried to explain it as simple as possible. If you are having problems it might be a better idea to pay a few bucks for a program that can do it for you without your involvement.
Good to hear!
Delete all of these. I think they are part of your problem.
Everything is fine with this. It’s not part of the problem.
Hello martio,
Without checking them out it is really hard to give you any sound advice. You can always copy/paste them in another .txt file and delete them from your hosts file. If any problems would occur – just paste them back into the hosts file and we will take it from there.
Hello Arthur,
Please post the whole entry that you deem suspicious, not just the IP but the text next to it. We will try to help you out.