Cloudnet
Cloudnet Virus is a Trojan that uses your computer as a cryptocurrency miner. While cloudnet.exe is running on your computer resources are used up, and as a result, it dramatically slows down your computer performance. This particular virus can be very malicious, used to cheat on your system or exploit its vulnerabilities in a number of ways. Approximately 70% of all computer infections are usually with Trojans, which makes them the most common threat you can encounter.
How to Uninstall Cloudnet?
The Cloudnet Virus
The Cloudnet Virus is a trojan horse infection that infiltrates the target’s system via other malware already present inside a system or downloaded from infected websites. The Cloudnet virus executes the cloudnet.exe which is known to mine cryptocurrency without the user’s knowledge.
The Cloudnet Virus
There may be many ways in which a virus script like Cloudnet can integrate into your PC. For instance, your computer can catch such malware through a variety of sources, such as suspicious-looking websites with potentially infected content, program packages, infected links, ads or messages and their attachments, especially some spam that you may find in your e-mail inbox. Typically, one click on the virus transmitter is enough to activate the script and help it fully exploit the vulnerabilities of your system. The absence of an effective and reliable antivirus tool can also be considered serious negligence towards your system’s safety. In most of cases, good antivirus software can detect and notify you about the potential threat, while without it, the virus can secretly infect you and it may take months or even years for you to realize what malware is lurking inside your windows software. Unfortunately, most of the victims come to know about it after serious damage has been done to their machine.
Cloud Net
Cloud net is a Trojan-based virus that can stealthily invade a computer and initiate many different malicious activities on it. In some cases, Cloud net can serve as a backdoor for other viruses and insert Ransomware or Spyware inside the infected computer.
Basically, every virus can be programmed to perform a wide range of malicious tasks. It all depends on the hackers, who control the infection and their intentions. If you have one on your computer, you are facing probably the worst type of malware ever developed, and you can never be sure what damage it may cause and what the criminals may use it for. We can only give you an idea about some of the most common issues, reported by the victims of viruses, so you could understand the harmful abilities of such an infection and take immediate action to remove it from your PC.
- A possible usage of the Cloud net Virus is for fun. Oftentimes, hackers, who create such malware, use it to entertain themselves by destroying random victims’ computers. This may sound sick but you never know how sick the brain of cybercriminals is. In most of the cases, the results of the attack are the complete damage of the OS and all the data on it.
- A virus-like Cloud net can be used as a tool for data theft. In such a case, the malware could be programmed to secretly create copies of your login credentials, passwords, banking, and payment details and deliver them to the crooks. There is no need to tell you what they can do with this data once they get their hands on it. Drained bank accounts and online profiles theft are just some of the possible scenarios.
- This virus may deliver another dreadful “buddy” inside your windows computer. In most of the cases, the virus comes in a combo with some other malware such as Ransomware or another nasty virus, that’s why you should scan your system throughout and remove all the malware that could have snuck inside.
Removing the threat:
When it comes to removing such a serious threat from your system, we recommend you use the instructions in the removal guide below and combine them with a thorough scan with the professional Cloudnet Virus removal tool. This will ensure that no malicious scripts will remain hidden on your machine and you will be able to clean everything and use your windows (7,10) computer safely.
Can’t uninstall Cloudnet Virus (cloudnet.exe)? This page includes detailed instructions on how to remove Cloudnet Virus that can be found at the bottom half of this article which works for windows 7 and windows 10.
In the text below, you will find all the important details about one recent Virus infection called Cloudnet also know as Cloud Net. If you stay on this page, you will come to know more about the possible negative effects you may experience due to this particular virus as well as all the possible methods to remove it from your system. For this, please find the manual removal guide that we have published below. Our most sincere desire is to help you cope successfully with this infection because the longer it stays on your computer, the worse the consequences for your system and your safety would be.
SUMMARY:
| Name | Cloudnet – Cloud Net – Cloudnet.exe |
| Type | Trojan |
| Danger Level | High (Viruses are often used as a backdoor for Ransomware) |
| Removal Tool |
How to Uninstall Cloudnet
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
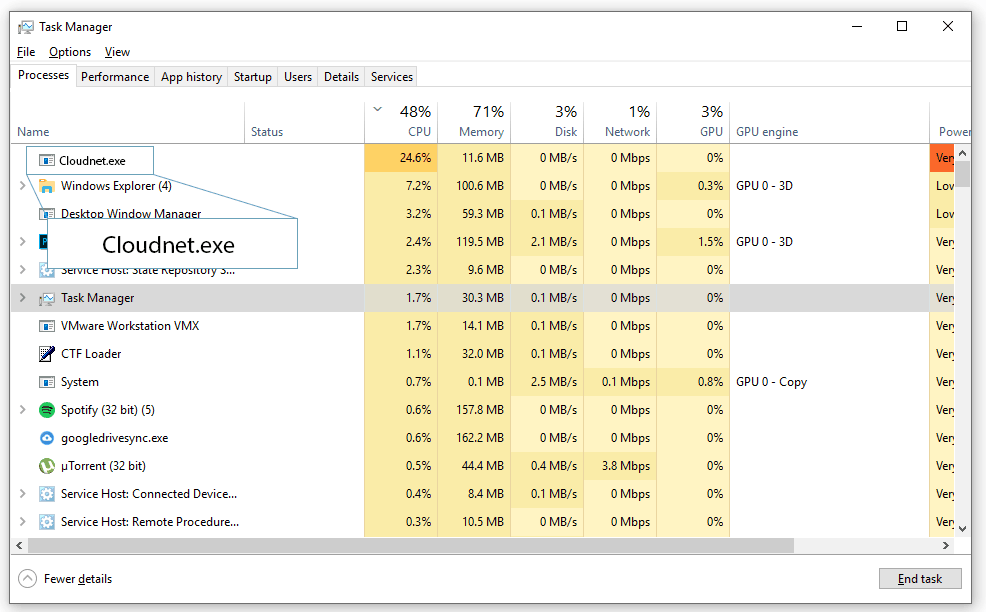
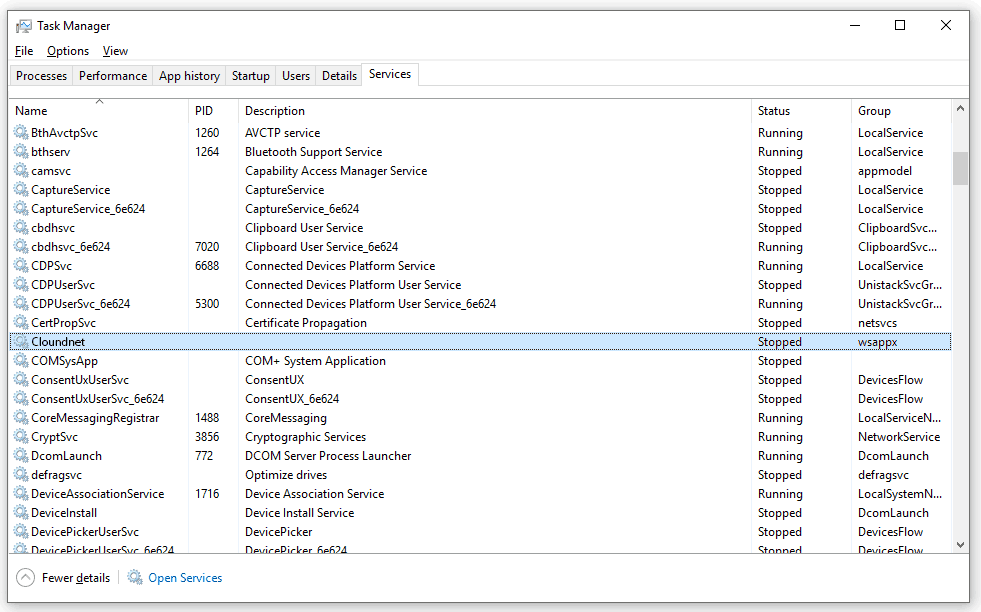
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.

The IPs at the bottom of the Hosts file need to be removed from it so make sure you do that and save the changes afterwards. Those are the ones you need to remove:
127.0.0.1 cpm.paneladmin. pro
127.0.0.1 publisher.hmdiadmingate. xyz
127.0.0.1 hmdicrewtracksystem. xyz
127.0.0.1 mydownloaddomain. com
127.0.0.1 linkmate. space
127.0.0.1 space1.adminpressure. space
127.0.0.1 trackpressure. website
127.0.0.1 doctorlink. space
127.0.0.1 plugpackdownload. net
127.0.0.1 texttotalk. org
127.0.0.1 gambling577 .xyz
127.0.0.1 htagdownload. space
127.0.0.1 mybcnmonetize. com
127.0.0.1 360devtraking. website
127.0.0.1 dscdn. pw
127.0.0.1 bcnmonetize.go2affise. com
127.0.0.1 beautifllink .xyz
Thanks
127. 0. 0. 1 activation. cloud. techsmith. com
127. 0. 0. 1 oscount. techsmith. com127. 0. 0. 1 www. techsmith. com
127. 0. 0. 1 updater. techsmith. com
127. 0. 0. 1 camtasiatudi. techsmith. com
127. 0. 0. 3 tsccloud. cloudapp. net
127. 0. 0. 2 assets. cloud. techsmith. com
You should delete those IPs from the Hosts file in your computer and then save the changes you have made to it.
My PC heats a lot with this virus, I am afraid my PC burns something meanwhile I do this steps, so I am shuting it down.
Ok first, im sorry im a noob
But what should i do after scanning and find all the malware with the spy hunter
I mean i know i should delete it, but how?
You can either go to the locations of the infected data and delete it from there or buy the full version of the tool for automatic removal. Also, did you try the guide from this page, the instructions in it could also help.
127.0.0.1 space1. adminpressure. space
127.0.0.1 trackpressure. website
127.0.0.1 htagzdownload .pw
127.0.0.1 texttotalk. org
127.0.0.1 360devtraking .website
127.0.0.1 room1. 360dev .info
127.0.0.1 djapp.info
127.0.0.1 technologievimy. com
the ones in my pc
We advise you to remove these IPs from the Hosts file on your computer, save the changes and then continue with the next steps from the guide.
162. 222. 193. 86 aoaomo. tremorhub. com
188. 95. 50. 62 bobomo. tremorhub. com
162. 222. 193. 86 www. howcast. com
162. 222. 193. 86 howcast. com
162. 222. 193. 86 www. ustream. tv
162. 222. 193. 86 ustream. tv
162. 222. 193. 86 www. livestream. com
162. 222. 193. 86 livestream. com
162. 222. 193. 86 www. dailymotion. com
162. 222. 193. 86 dailymotion. com
192. 192. 3. 8 www. virustotal. com
192. 192. 3. 8 virustotal. com
You should delete the IPs from the Hosts file as they are not supposed to be there and may be the cause behind your issue. Delete them, save the changes and continue with the rest of the guide.
These are what is in my pc:
127.0.0.1 space1.adminpressure. space
127.0.0.1 trackpressure. website
127.0.0.1 htagzdownload. pw
127.0.0.1 360devtraking. website
127.0.0.1 room1.360dev. info
127.0.0.1 djapp. info
127.0.0.1 sharefolder. online
127.0.0.1 telechargini. com
127.0.0.1 fffffk. xyz
127.0.0.1 smarttrackk. xyz
Those are definitely rogue IP addresses and must not be kept in your Hosts file – remove them from the file and save the changes. After that, complete the rest of the guide to ensure that everything unwanted or potentially dangerous is removed.
I just recently got this virus. I am currently resetting my computer to factory settings. Will this help delete the trojens or make it worse. I quickly detected since I always check my programs installed in control panel to make sure nothing extra was installed.
Will resetting my computer to factory settings remove this trojen?
It should remove it but it’s advisable that you first try the instructions from the guide or the removal tool in it, as they may allow you to remove the Trojan without resetting your computer to its factory settings.
127.0.0.1 space1.adminpressure.space
127.0.0.1 trackpressure.website
127.0.0.1 htagzdownload.pw
127.0.0.1 360devtraking.website
127.0.0.1 room1.360dev.info
127.0.0.1 djapp.info
127.0.0.1 sharefolder.online
127.0.0.1 telechargini.com
127.0.0.1 fffffk.xyz
127.0.0.1 smarttrackk.xyz
127.0.0.1 space1.adminpressure.space
127.0.0.1 trackpressure.website
127.0.0.1 htagzdownload.pw
127.0.0.1 360devtraking.website
127.0.0.1 room1.360dev.info
127.0.0.1 djapp.info
127.0.0.1 sharefolder.online
127.0.0.1 telechargini.com
127.0.0.1 fffffk.xyz
127.0.0.1 smarttrackk.xyz
Those IPs are definitely not supposed to be in the Hosts file on your computer – be sure to delete them from the file, save the changes, and complete the rest of the guide.
it says ” unable to delete specified values”
Where does it say that?
I see the:
0.0.0.1 mssplus.mcafee.com
127.0.0.1 space1.adminpressure.space
127.0.0.1 trackpressure.website
127.0.0.1 htagzdownload.pw
127.0.0.1 360devtraking.website
127.0.0.1 room1.360dev.info
127.0.0.1 djapp.info
127.0.0.1 sharefolder.online
127.0.0.1 telechargini.com
127.0.0.1 fffffk.xyz
127.0.0.1 smarttrackk.xyz
127.0.0.1 space1.adminpressure.space
127.0.0.1 trackpressure.website
127.0.0.1 htagzdownload.pw
127.0.0.1 360devtraking.website
127.0.0.1 room1.360dev.info
127.0.0.1 djapp.info
127.0.0.1 sharefolder.online
127.0.0.1 telechargini.com
127.0.0.1 fffffk.xyz
127.0.0.1 smarttrackk.xyz
When I highlight and backspace, then save the changes they merely reappear.
Do you have Admin privileges on the computer? Try right-clicking on the Hosts file, and then selecting the “Run as an Admin” option, and then try to delete the IPs again. Also, try doing all this from Safe Mode in case you didn’t do that before.
hi sir could anyone help me as i had removed cloudnet virus from computer but later when i check on my saved files i see its extension change to other format how can i use my corrupted files like normal pls help me out thank you much appreciated
127.0.0.1 space1.adminpressure.space
127.0.0.1 trackpressure.website
127.0.0.1 htagzdownload.pw
127.0.0.1 360devtraking.website
127.0.0.1 room1.360dev.info
127.0.0.1 djapp.info
127.0.0.1 sharefolder.online
127.0.0.1 telechargini.com
127.0.0.1 fffffk.xyz
127.0.0.1 smarttrackk.xyz
127.0.0.1 space1.adminpressure.space
127.0.0.1 trackpressure.website
127.0.0.1 htagzdownload.pw
127.0.0.1 360devtraking.website
127.0.0.1 room1.360dev.info
127.0.0.1 djapp.info
127.0.0.1 sharefolder.online
127.0.0.1 telechargini.com
127.0.0.1 fffffk.xyz
127.0.0.1 smarttrackk.xyz
Those IPs shouldn’t be in your hosts file – delete them from there.