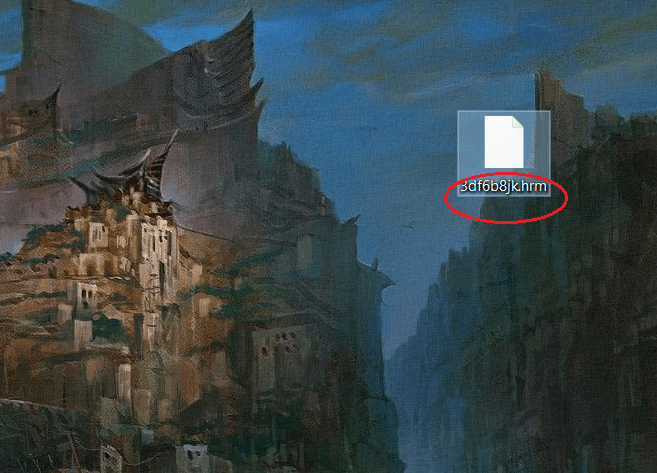
Hrm
One of the latest ransomware variants to be doing the same by encrypting users’ files is a virus called Hrm ransomware. If you were infected by this variant, surely by now you have noticed that the extensions to the files you can no longer open have been changed and that is part of Hrm Virus’s malicious encryption and blackmail scheme to extort money from you and thousands of others like you.
Ransomware viruses have proven to be among the most devastating forms of malware known to mankind. These stealthy little workers of evil are capable of robbing individuals, business and whole institutions of access to some of their most vital information. The good news is that you may yet be able to recover from this infection without having to level with the hackers behind this horrible malware. A possible solution to the problem may lie in the removal guide we have designed specifically for locating and removing Hrm Virus, as well as subsequently attempting to restore the encoded data from system backups. Now, while it’s imperative that you do indeed get rid of the ransomware, success with recovering the files is far less definitive. Read on and we will explain.
The Hrm Virus
Before we get into the details of how to fend of Hrm Virus and its consequences, it’s important to first understand how viruses of this type operate and what is that makes them so elusive. For one, they don’t really have any symptoms.
A ransomware infection is silent and may sometimes only cause a slowdown in your computer’s overall performance. But generally that’s not something that would trigger your average user’s suspicion. In addition to that, even most antivirus software doesn’t recognize ransomware as a real threat, as absurd as it may sound. And the reason is because it doesn’t detect encryption as a malicious process, because, in essence, it isn’t one. Furthermore, the encryption algorithms that ransomware viruses use are often very complex, which is what makes the consequences so devastating. Oftentimes there’s just no possibility to have the encrypted files decrypted.
As a matter of fact, numerous users end up disappointed when they submit to the hackers’ demands and still end up with a bunch of useless data, because they never received a decryption key. Alternatively, decryption keys that are sent may also not always work as they should and the result is ultimately the same. This is actually one of the reasons we wouldn’t recommend paying the ransom. Another reason is the fact that once you’ve done that, you will have pretty much funded a criminal scheme with no way for the authorities to track the money flow and bring the cybercriminals to justice. Normally this is because the people behind viruses like Hrm request they be sent the ransom in Bitcoin or some other cryptocurrency. And these are impossible for anyone to track.
The Hrm file recovery
The Hrm file recovery requires either a full personal data backup source or a file decryption key. For one, regardless of what happens next, you should by all means tend to the immediate removal of Hrm Virus from your system. This is to prevent any other files that come into contact with your system from getting encrypted.
And it’s also a way to avoid getting infected by other malware that the ransomware could potentially introduce to your computer. After that, you can try to recover your files from system backups, as shown in the removal guide below. And if that doesn’t work, you can also try using specialized software designed to decrypt data, such as the decryptor tools that we have listed on our site.
Another important point we need to make is regarding preventing future ransomware attacks. The best way to make sure you don’t end up in this situation again is to keep copies of your most important files on a separate hard drive that isn’t constantly connected to a computer. That way, even in case of an infection, the hackers’ efforts will be fruitless. But it’s best to of course not get infected in the first place and you can minimize the chances of that happening by following basic safety measures when browsing the web. Do no interact with shady content, don’t open spam emails and simply just use your common sense.
SUMMARY:
| Name | Hrm |
| Type | Ransomware |
| Detection Tool |
Hrm Virus Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment