Hurawatch
Hurawatch is a piece of software that operates as an advertising tool in users’ browsers. Specifically, Hurawatch falls in the category of browser hijackers.
The Hurawatch virus redirect the page at any given moment to some sponsored web location
And it gets its name due to the fact that it integrates with the main browser on your PC and introduces certain changes to its settings, thus ‘hijacking’ it.As a result, the hijackers changes the browser’s homepage and usually also sets a new default search engine. In doing so, it makes sure that these particular websites get more traffic. And we should also point out that it doesn’t really matter what particular browsing program you’re using. Software like Hurawatch is perfectly comfortable in Chrome, Firefox, Edge and most other massively used browsers.
In addition to the above, software of this type is notorious for generating vast streams of online ads throughout your browsing sessions. This means that every website you visit will basically be filled with various advertising materials that have nothing to do with the website in question. Everything from popups and in-text links to box messages and banners – you will likely see it all. Furthermore, browser hijackers like Hurawatch or Poshukach are notorious for their ability to redirect the page at any given moment to some sponsored web location. And we all know how frustrating that can be when you’re trying to get something done online.
But luckily you won’t have to be exposed to all this ad-harassment for much longer. You will be able to restore your browser settings to their initial state and rid yourself of all of the intrusive advertisements by removing Hurawatch from your OS. To do this, however, you will have to take a few extra steps compared to when uninstalling most regular software. And we’ve got you covered. Below we’ve compiled a removal guide that will help you do just that.
The Hurawatch Virus
One of the more common misconceptions circulating regarding programs like the Hurawatch virus is that they are in fact viruses. This is not the case. Moreover, unlike actual viruses, the Hurawatch virus cannot harm your system in any way, they cannot gain access to your personal information and have virtually no interest in causing any type of damage.
All they want is your attention. Namely, they’re interested in your clicks and views, as this is the way that the developers of such pieces of programming earn revenue. But with that in mind, that doesn’t make software like Hurawatch entirely safe either.
In fact, many experts classify these types of programs as potentially unwanted for several reasons. And one of them is that as a result of their page redirects and other activities, users may potentially end up on an infected site or bump into compromised web content. Hence, if your system isn’t adequately protected (which you really might have no way of knowing until it’s too late), you could easily get infected with terrible threats such as Trojans and ransomware. For this reason, it’s always best to just remove Hurawatch from your system and avoid dealing with any of its ads.
SUMMARY:
| Name | Hurawatch |
| Type | Browser Hijacker |
| Detection Tool |
Remove Hurawatch Virus
To remove Hurawatch from your Windows PC, you have to check the browsers on the computer for any suspicious extensions that must be deleted.
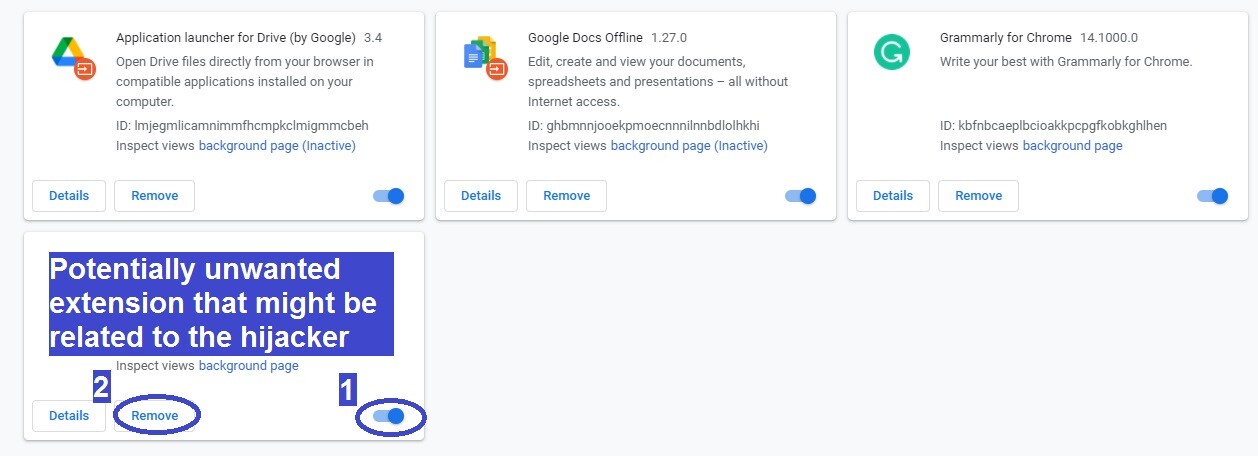
- First, open the main browser on the computer, select the menu from the top right/left corner, and click the Extensions (or Add-ons) option.
- Then look for extensions that you didn’t install yourself and/or that seem like they shouldn’t be in the browser.
- If you see a potentially unwanted extension, disable it and then delete it.
- Go to your other browsers and do the same thing there to remove Hurawatch from them.
In case those steps didn’t rid you of the hijacker, then it is likely that other changes have been made by Hurawatch in the system, and you’d first need to take care of them as well before the unwanted software goes away. You will find detailed instructions on how to clean the rest of your system down below.
Extended Guide We suggest that you bookmark this page or open it on another device so that you don’t lose it, because you will be required to close the browser and restart the system while completing the guide.
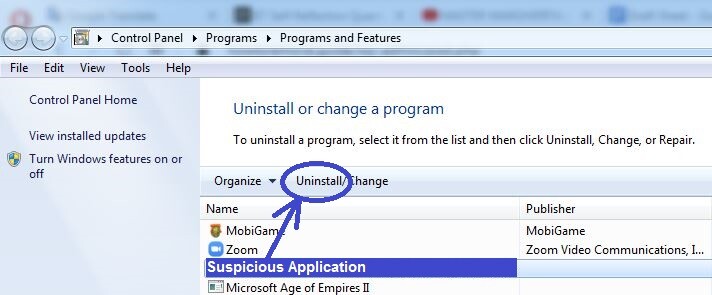
Step 1 The first thing you should do is go to Start Menu > Control Panel > Uninstall a Program where you will see all programs that are on the computer. Since it is likely that Hurawatch got in the system because a rogue program got installed on the computer, check the list for items installed around the time of the hijacker’s first appearance. If there are any sketchy-looking programs installed around that time, you should uninstall them. To uninstall a given program, simply select its entry from the list, click Uninstall at the top, and follow the prompts from the uninstaller. Make sure that everything related to that program is deleted, including personalized user settings.
Step 2
WARNING! READ CAREFULLY BEFORE PROCEEDING!
The next thing to do is to go to the Task Manager by pressing together the Ctrl, Shift, and Esc keys. Go to the Processes tab of the Task Manager and take a look at the processes that are using the most RAM and CPU power – if among them there is one (or more) with an unusual, suspicious, or unfamiliar name, perform an online search for that process name and see what you can find.
Chances are that if the suspected process is linked to Hurawatch, there will be reports from other users on the Internet addressing that fact. If you find any such information posted on reputable sites, return to the Task manager, right-click the suspicious process, and click the Open File Location option. Now use the scanner that we’ve offered below to check for malware each of the files contained in the location folder.


If even a single file gets flagged as malicious by our scanner, this means you must quit the suspicious process and then delete its location folder. To quit the process, right-click it and select the End Process option.
When trying to delete the location folder, you may get an error message that says some of the files contained in it can’t be deleted at the moment. If this happens to you, try to delete the remaining files from the folder and then go to the next steps. Once the rest of the guide has been completed, return to the location folder and attempt to delete it again.
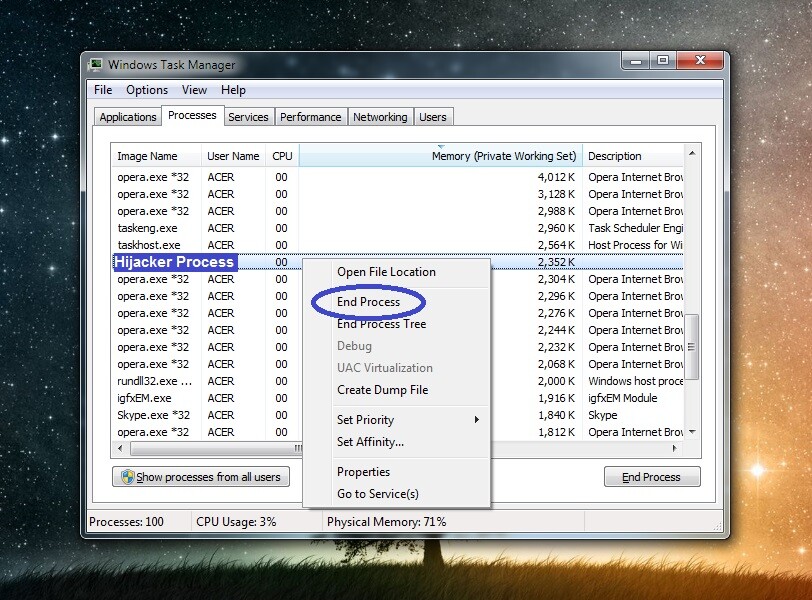
One more thing to mention is that, even if you didn’t spot malware while scanning the files, if there are reports from reputable sources online that state the process is unwanted, you should still quit that process and delete its files and folder.
Step 3 For this step, you must enter Safe Mode on your PC – this will help keep any hijacker processes that you may have missed during the last step from obstructing you while completing the rest of the guide.
Step 4 Press Winkey and R to evoke the Run search box and copy-paste in it the following line:
- notepad %windir%/system32/Drivers/etc/hosts
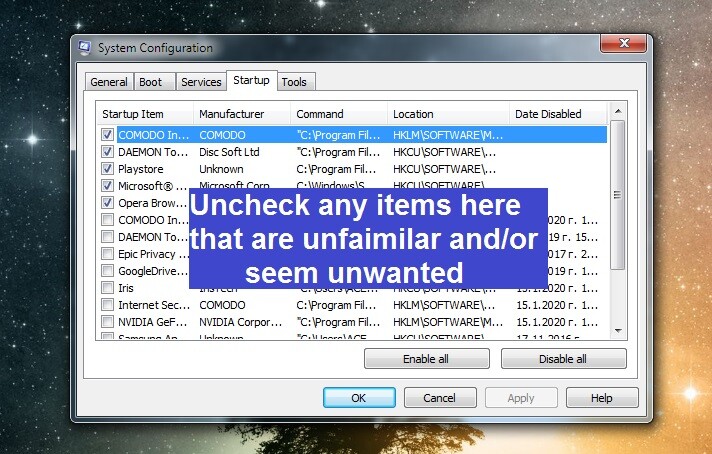
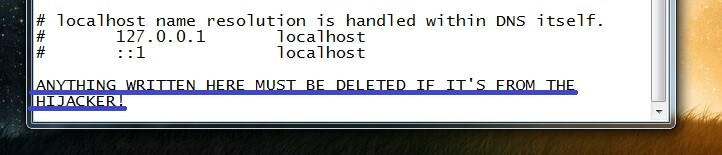 Open Run again, type msconfig, hit Enter, and select the Startup section. If any of the startup items listed there seem odd, unfamiliar, and/or potentially linked to Hurawatch, uncheck them and then select OK.
Open Run again, type msconfig, hit Enter, and select the Startup section. If any of the startup items listed there seem odd, unfamiliar, and/or potentially linked to Hurawatch, uncheck them and then select OK.
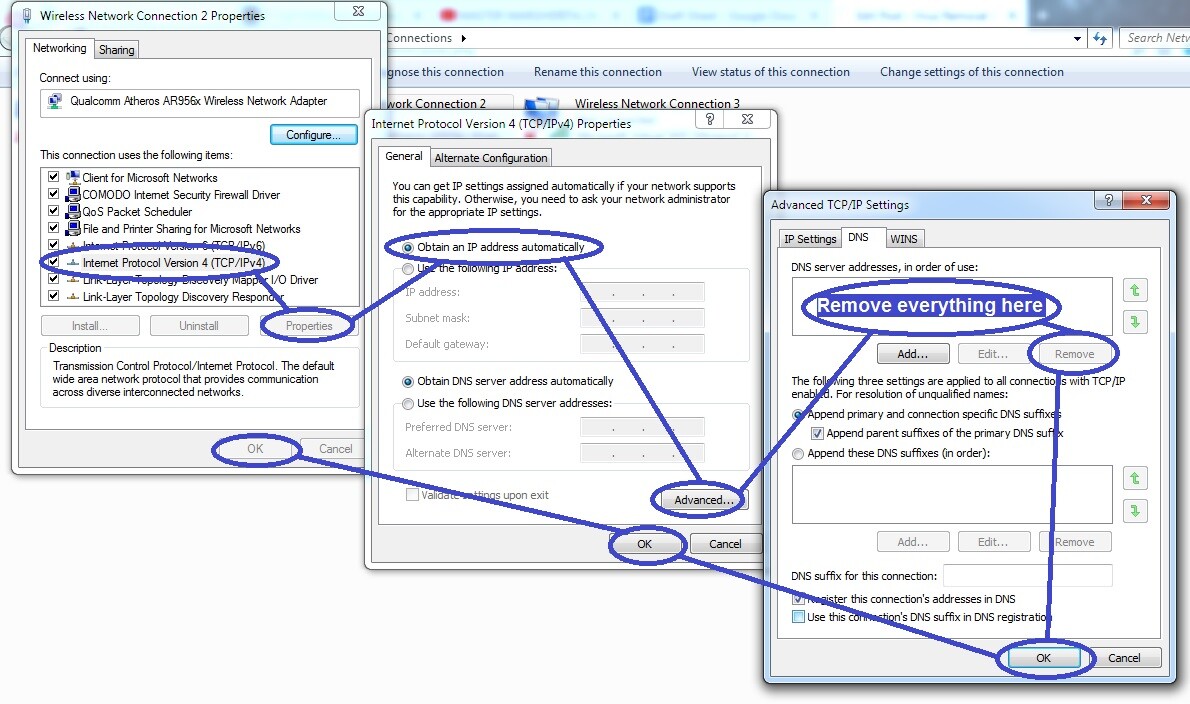
 Go to Run again, this time type in it ncpa.cpl, press the Enter key, and right-click the icon that represents the network that you are currently connected to. Next, select Properties and in the window that opens click the Internet Protocol Version 4 item from the list. Click on the next Properties button and check/select the Obtain an IP address automatically setting in the next window. After that, access the Advanced options and there open the DNS tab. See if there are IPs listed in that tab and if there are any, delete them and click OK on everything.
Go to Run again, this time type in it ncpa.cpl, press the Enter key, and right-click the icon that represents the network that you are currently connected to. Next, select Properties and in the window that opens click the Internet Protocol Version 4 item from the list. Click on the next Properties button and check/select the Obtain an IP address automatically setting in the next window. After that, access the Advanced options and there open the DNS tab. See if there are IPs listed in that tab and if there are any, delete them and click OK on everything.
Step 5
WARNING!: It is very important to be careful while completing this step so that you don’t delete any items that you aren’t supposed to. If you are unsure about any item/items – ask us what to do about them in the comments instead of outright deleting them. Otherwise, you could end up causing more problems for your system.
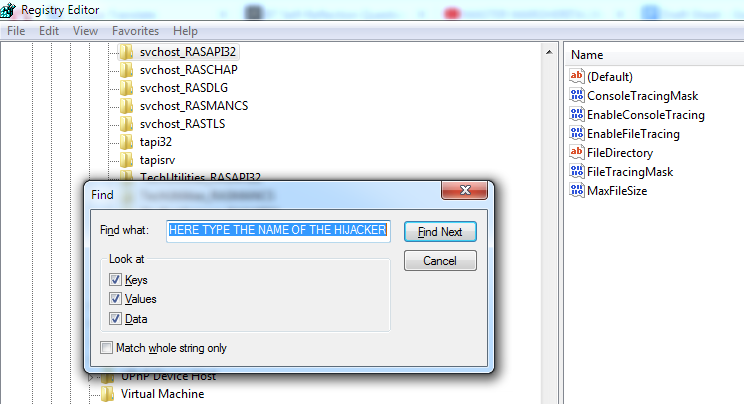
Open the Start Menu and in it type regedit. An item named regedit.exe should show up in the results – click it and then click on Yes to start the Registry Editor tool. Next, press Ctrl and F from the keyboard to evoke the Registry Editor search and in it type Hurawatch and click the Find Next button to begin the search.
Delete the first found item (if such an item is found), do another search, delete the next thing, rinse and repeat until all items that are related to Hurawatch are gone from the Registry of your PC.
Lastly, go to the next three locations in the Registry Editor by using the sidebar to the left.
- HKEY_CURRENT_USER/Software/Random Directory.
- HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run
- HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main
Look for folders in those locations that have very long names with random letters or numbers in the names. If there are such items in either of the three locations, delete those items. However, if you don’t know if an item is to be deleted, we once again remind you to consult us through the comments section.
Step 6 The last step is to once again have a look at your browsers (even if it seems you’ve cleaned them at the start of the guide). First, right-click the browser icon, go to Properties, open the Shortcut section, and delete anything that may be written after “.exe” in the Target text field. Next, start the browser itself and click its menu – most browsers have their menu icons in the top right or top left corner of the screen. From the menu of the browser, select the Extensions or Add-ons option and then look through what extensions are listed on the next page. Any entries there that are unfamiliar to you or that may be unwanted should first be disabled and then deleted.
- If you are using the Google Chrome browser, you must first click More Tools from its menu and then you will see the Extension option in the sub-menu.
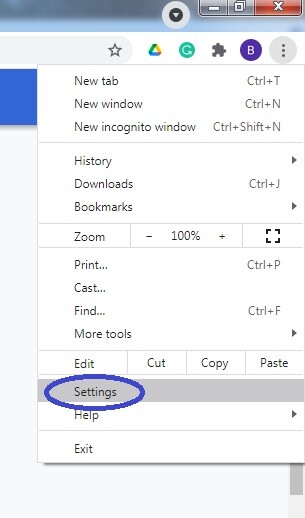
After you’ve cleaned the extensions, open the menu again and click Settings/Options.
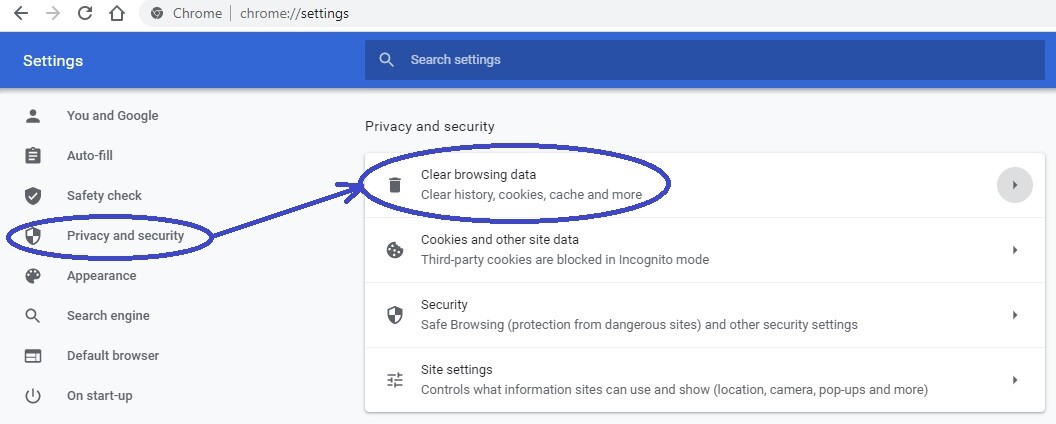
Find and click the Privacy and Security options and then select the Clear Browsing Data button. In the Microsoft Edge browser, you should be looking for and click on the Choose what to clear button.
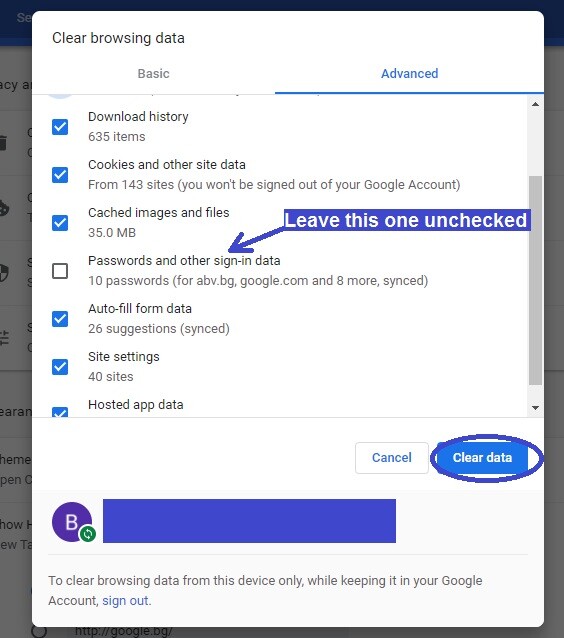
In the dialogue window that shows up, you must select all items except the one that relates to your passwords and then select the Clear Now/Clear Data button to start the process.

Leave a Comment