This page aims to help you remove I know Email Scam. Our removal instructions work for every version of Windows.
Trojans Horse viruses are malicious computer programs with some particularly unpleasant abilities. If you care about the safety and security of your computer system, you should definitely be aware of the main characteristics of the representatives of this malware category. Being well aware of what such a virus may be capable of, how it gets distributed, and what methods you can use to remove it could make the difference between maintaining a healthy and safe computer and getting your data corrupted, your system heavily damaged, and your online privacy invaded.
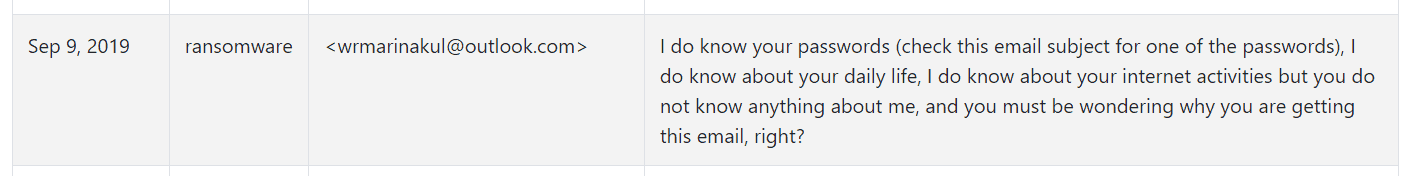
The I Know Email
The I know email is a phishing email scam resulting from a breached database containing the email of the victim. The creators of the I know email likely don’t have your passwords.
The I know Trojan Horse is a newly released malware program of the Trojan Horse category, and our goal within the next lines is to help you understand it better, and remove it from your system, in case it has already nested itself there.
One of the most typical traits of hazardous programs like I know is their advanced stealth. If you have I know in your computer, you have likely not noticed how it got there, and this is not surprising. Trojans like this one have all kinds of methods of infiltrating one’s computer without showing visible symptoms, and without raising the user’s suspicious. One example of that is when disguise is used to trick the user into opening the file that contains the virus. This disguise could be anything – the malware may be sent as an email attachment to a spam email letter, which the user is prompted to open under some misleading premise. In other cases, the victim of the malware may download a pirated software installer, which actually contains the virus in itself. Executing such an installer would immediately infect the computer and allow the malicious program carry out its nefarious tasks. Oftentimes, random deceitful ads, and clickbait prompts may also land you some nasty virus like I know if you interact with them. All in all, if you aren’t careful with your activities while on the Internet, as well as with the sites you visit and the content you download, the chances of getting a Trojan Horse in your computer are rather high. And even if you stay cautious while browsing the web, you could still land a Trojan, because even the most experienced and vigilant of users could get tricked. This is why you’d also need a second layer of defense for your system in the form of a reliable antivirus, and anti-malware tool. One such anti-malware tool you can find in the guide down below – it is a professional security program that can keep your system safe, as well as help with the removal of threats like I know.
The I know Scam
The “I know” scam is not truly a malware – rather it scares users into thinking it is one. In reality it is nothing more than a hacked database containing an old password that was used, hence how the creators of the “I know” scam know that password.
If you make sure to follow the instructions from the guide below, you should be able to quickly and safely remove the Trojan threat that’s in your computer, thus preventing the malware from spying on you, corrupting your data, causing BSOD crashes, taking over your whole computer, or whatever else it may have been tasked with completing in your computer.
SUMMARY:
| Name | “I know” |
| Type | Trojan/Fake email |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
I know Email Scam Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Reply