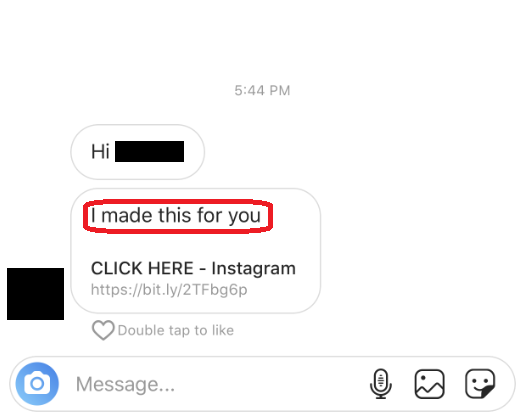
“I made this just for you”
The “I made this just for you” message on Instagram is a scam. If you open the link sent in the message you will be redirected to a page very similar to the login screen of Instagram, once you enter you account and password in the space given you will be exposed to an unknown potential threat.
In this article, you will find important details about “I made this just for you” and the possible problems you may face due to its activities. If you are looking for more than that, then you probably will be interested in how to remove the Trojan from your system. That’s why, apart from the information in the next paragraphs, below we have added a removal guide to help you deal with the malware once and for all.
“I made this just for you” Instagram Scam
If you have received a message on Instagram saying “I made this just for you” it means you are a victim of a scam attempt. Clicking on the link will open a page which will ask for your account information, do not type anything or your system will be exposed to a potential threat.
Every Trojan horse can be used for many different criminal purposes. Often, the hackers who control the infection use it as a tool for personal data theft. A Trojan such as “I made this just for you” can be designed to simply copy and steal passwords, login details and/or credentials to bank accounts and transfer them to remotely-controlled servers. This malware can also log and keep copies of your keystrokes, take screenshots of things on your screen and monitor your online activities such as the websites you visit, the videos you see, etc. This allows the criminals who control the Trojan to steal someone’s information or identity and perform crimes or their behalf or directly abuse them.
Other Information about Trojan Horses
By definition, any malicious software that enters a device by misleading users about its true intentions and abilities can be considered a Trojan horse. All the Trojans have one thing in common: they are usually used by hackers to stealthily access a computer and launch different criminal activities in it without the victim’s knowledge. There are many sneaky ways in which hackers may render an infection like “I made this just for you” part of your machine. The malware may come from free software packages that have been compromised, or from infected e-mail letters and attachments. However, there are many suspicious web pages that actively distribute Trojans and if you land on some of them, you may get infected in a matter of seconds. In general, threats like “I made this just for you” can use the vulnerable spots in a computer system or any installed program. These could often be outdated applications, the absence of recent OS security patches or the absence of high-quality antivirus software.
A very important thing that needs to be mentioned about most Trojan-based infections is that they can often serve as a backdoor to other infections. Typically, threats like “I made this just for you” can be paired up with Ransomware and Spyware viruses which means that, by getting infected with the Trojan, you may automatically get compromised with the accompanying malware.
Therefore, one of the most important things is to prevent such infections by investing in reliable system protection. A good security program can prove invaluable in detecting the malware on time and is much more effective than relying on your personal observations to catch the virus because, in most cases, the Trojans don’t show any visible symptoms which can give them away. Besides, threats like “I made this just for you” may be quite challenging to remove if you are not armed up with a trusted removal tool or at least a detailed removal guide like the one below.
SUMMARY:
| Name | “I made this just for you” |
| Type | Trojan |
“I made this just for you” Instagram Scam Removal
You are dealing with a browser hijacker that can restore itself. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
- Locate and clean up your phone’s calendar events if they are infected.
- Find browser extensions related to the threat and how to remove them.
- Ensure your passwords were not stolen or tampered with.
You can find the removal guide here.

Leave a Comment